
Microsoft Azure Monitor alerts are being abused to send callback phishing emails that impersonate warnings from the Microsoft Security Team about unauthorized charges on your account.
Azure Monitor is Microsoft’s cloud-based monitoring service that collects and analyzes data from Azure resources, applications, and infrastructure. It enables users to track performance, notify about billing changes, detect issues, and trigger alerts based on various conditions.
Over the past month, numerous people have reported receiving Azure Monitor alerts warning of suspicious charges or invoice activity on their accounts, urging them to call an enclosed phone number.
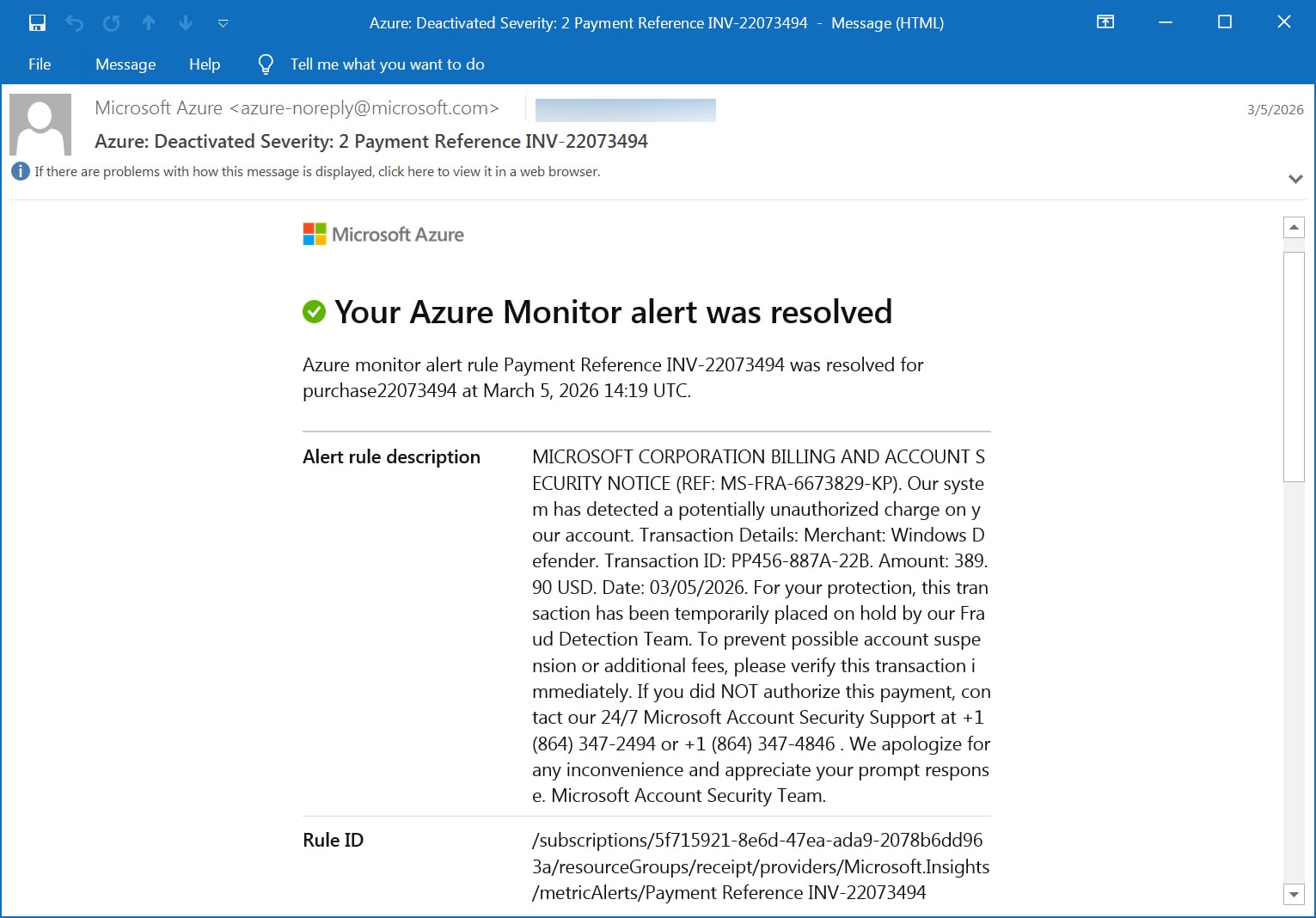
“Alert rule description MICROSOFT CORPORATION BILLING AND ACCOUNT SECURITY NOTICE (REF: MS-FRA-6673829-KP). Our system has detected a potentially unauthorized charge on your account. Transaction Details: Merchant: Windows Defender. Transaction ID: PP456-887A-22B. Amount: 389.90 USD. Date: 03/05/2026l,” reads the fake billing alert.
“For your protection, this transaction has been temporarily placed on hold by our Fraud Detection Team. To prevent possible account suspension or additional fees, please verify this transaction immediately. If you did NOT authorize this payment, contact our 24/7 Microsoft Account Security Support at +1 (864) 347-2494 or +1 (864) 347-4846.”
“We apologize for any inconvenience and appreciate your prompt response. Microsoft Account Security Team.”
Source: BleepingComputer
Unlike other phishing campaigns, these messages are not spoofed, but are sent directly by the Microsoft Azure Monitor platform using the legitimate azure-noreply@microsoft.com email address.
As the emails are sent through Microsoft’s legitimate email platforms, they pass SPF, DKIM, and DMARC email security checks, making them appear more trustworthy.
Authentication-Results: relay.mimecast.com;
dkim=pass header.d=microsoft.com header.s=s1024-meo header.b=CKfQ8iOB;
arc=pass ("microsoft.com:s=arcselector10001:i=1");
dmarc=pass (policy=reject) header.from=microsoft.com;
spf=pass (relay.mimecast.com: domain of azure-noreply@microsoft.com designates 40.107.200.103 as permitted sender) smtp.mailfrom=azure-noreply@microsoft.com
The threat actors are conducting this campaign by creating alerts in Azure Monitor for easily triggered conditions, such as new orders, payments, generated invoices, and other billing events.
When creating alerts, you can enter any message you want in the description field, which the attackers use to put their callback phishing message.
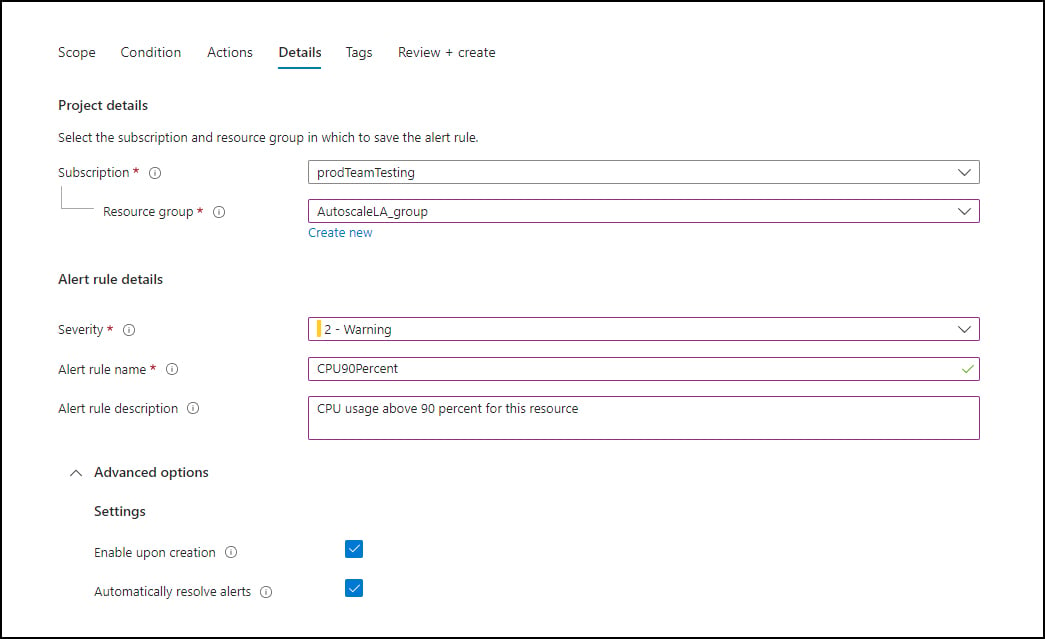
Source: Microsoft
These alerts are then configured to send emails to what is believed to be a mailing list under the attacker’s control, which forwards the email to all the targeted people in the attack.
This also preserves the original Microsoft headers and authentication results, helping the emails bypass spam filters and user suspicion.
BleepingComputer has seen multiple alert categories used in this campaign, mostly using invoice and payment-themed rules designed to resemble automated billing notifications:
- Azure monitor alert rule order-22455340 was resolved for invoice22455340
- Azure monitor alert rule Invoice Paid INV-d39f76ef94 was resolved for invd39f76ef94
- Azure monitor alert rule Payment Reference INV-22073494 was resolved for purchase22073494
- Azure monitor alert rule Funds Successfully Received-ec5c7acb41 was triggered for subec5c7acb41
- Azure monitor alert rule MemorySpike-9242403-A4 was triggered
- Azure monitor alert rule DiskFull-3426456-A6 was triggered for locker3426456
The campaign relies on creating a sense of urgency, which in this case is the unusual $389 Windows Defender charge, to trick the users into calling the listed phone number.
While BleepingComputer did not call the number in this scam, previous callback phishing campaigns led to credential theft, payment fraud, or the installation of remote access software.
As these emails use a more enterprise or corporate theme, they may be intended to gain initial access to corporate networks for follow-on attacks.
Users should treat any Azure or Microsoft alert that includes a phone number or urgent request to resolve billing issues with suspicion.


