
A financially motivated threat actor tracked as Storm-2755 is stealing Canadian employees’ salary payments after hijacking their accounts in payroll redirection (also known as payroll pirate) attacks.
The attackers used malicious Microsoft 365 sign-in pages to steal victims’ authentication tokens and session cookies by redirecting them to domains (e.g., bluegraintours[.]com) hosting malicious web pages (pushed to the top of search engine results through malvertising or SEO poisoning) that masqueraded as Microsoft 365 sign-in forms.
This allowed Storm-2755 to bypass multifactor authentication (MFA) in adversary‑in‑the‑middle (AiTM) attacks by replaying stolen session tokens rather than re-authenticating.
“Rather than harvesting only usernames and passwords, AiTM frameworks proxy the entire authentication flow in real time, enabling the capture session cookies and OAuth access tokens issued upon successful authentication,” Microsoft explained.
“Due to these tokens representing a fully authenticated session, threat actors can reuse them to gain access to Microsoft services without being prompted for credentials or MFA, effectively bypassing legacy MFA protections not designed to be phishing-resistant.”
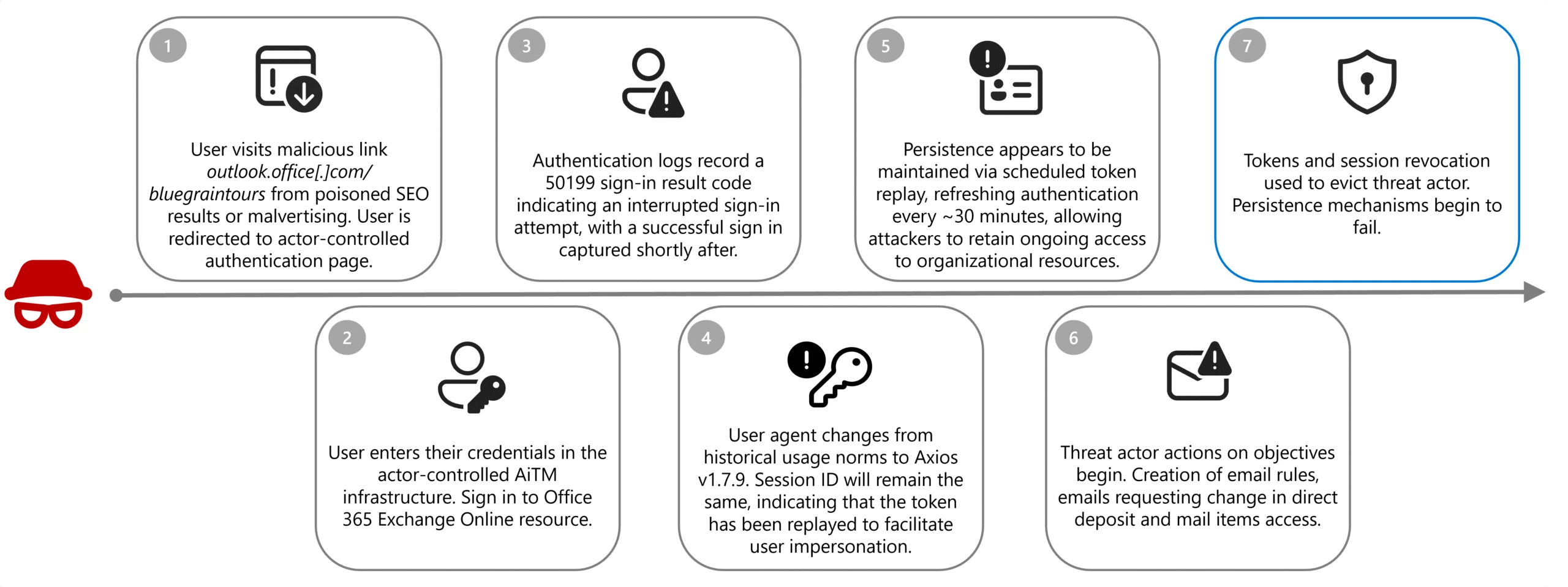
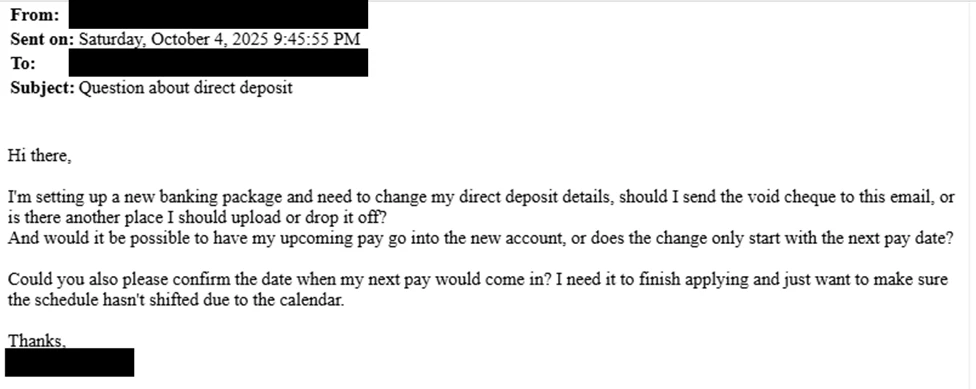
After gaining access to an employee’s account, the attacker created inbox rules that automatically moved messages from human resources staff containing the words “direct deposit” or “bank” to hidden folders, preventing the victim from seeing the correspondence.
In the next stage, they searched for “payroll,” “HR,” “direct deposit,” and “finance,” then sent emails to human resources staff with the subject line “Question about direct deposit” to trick staff into updating banking information.
Where social engineering failed, the attacker logged directly into HR software platforms such as Workday, using the stolen session to manually update direct deposit details.
To harden defenses against AiTM and payroll pirate attacks, Microsoft advises defenders to block legacy authentication protocols and implement phishing-resistant MFA.
If any signs of compromise are detected, they should also revoke compromised tokens and sessions immediately, remove malicious inbox rules, and reset MFA methods and credentials for all affected accounts.
In October, Microsoft disrupted another pirate payroll campaign targeting Workday accounts since March 2025, in which a cybercrime gang tracked as Storm-2657 targeted university employees across the United States to hijack their salary payments.
In these attacks, Storm-2657 breached the targets’ accounts via phishing emails and stole MFA codes using AITM tactics, which allowed the threat actors to compromise the victims’ Exchange Online accounts.
Payroll pirate attacks are a variant of business email compromise (BEC) scams that target businesses and individuals who regularly make wire transfers. Last year, the FBI’s Internet Crime Complaint Center (IC3) recorded over 24,000 BEC fraud complaints, resulting in losses exceeding $3 billion, making it the second most lucrative crime type behind investment scams.



