A surge in LummaStealer infections has been observed, driven by social engineering campaigns leveraging the ClickFix technique to deliver the CastleLoader malware.
LummaStealer, also known as LummaC2, is an infostealer operation running as a malware-as-a-service (MaaS) platform that was disrupted in May 2025 when multiple tech firms and law enforcement authorities seized 2,300 domains and the central command structure supporting the malicious service.
Infostealing malware targets various sensitive data that can range from credentials and cookies stored in web browsers, cryptocurrency wallet details, and documents to session cookies, authentication tokens, VPN configurations, and account data.
Although the law enforcement operation severely disrupted the LummaStealer activity, the MaaS operation started to resume in July 2025.
A new report from cybersecurity company Bitdefender warns that LummaStealer operations have scaled significantly between December 2025 and January 2026, now being delivered through a malware loader called CastleLoader, and increasingly relying on ClickFix techniques.
“At the core of many of these campaigns is CastleLoader, which plays a central role in helping LummaStealer spread through delivery chains. Its modular, in-memory execution model, extensive obfuscation, and flexible command-and-control communication make it well-suited to malware distribution of this scale,” Bitdefender researchers say.
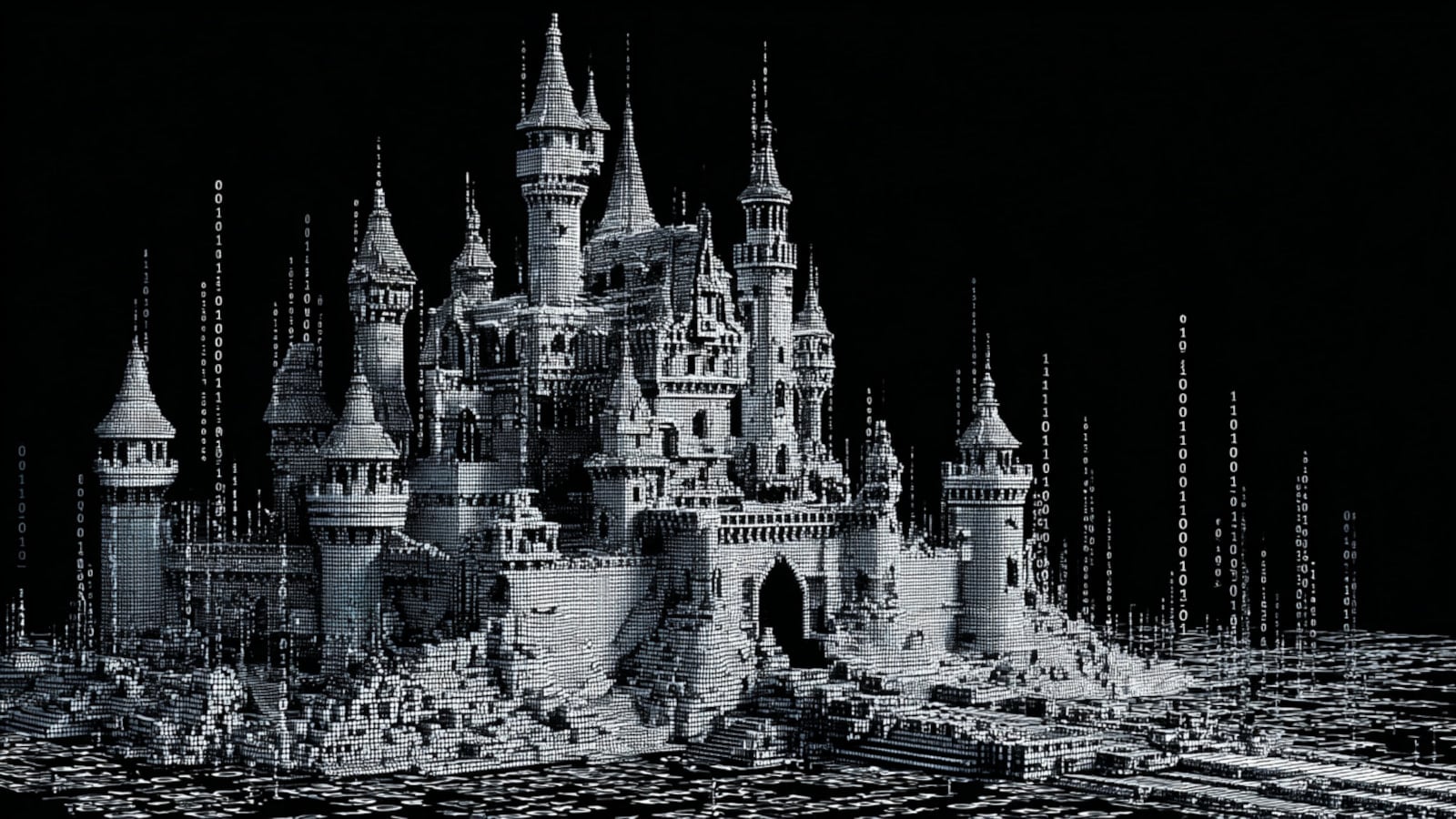
CastleLoader emerged in early 2025 and has been distributing multiple families of infostealers and remote access trojans (Stealc, RedLine, Rhadamanthys, MonsterV2, CastleRAT, SectopRAT, NetSupport RAT, WarmCookie) through various methods, including ClickFix.
The malware loader is a heavily obfuscated script-based (AutoIT or Python) malware loader that decrypts, loads, and executes the LummaStealer payload entirely in memory.
It employs multiple obfuscation layers, including dictionary-based renaming of variables and functions, encoded strings decoded at runtime, large amounts of junk code and dead branches, and arithmetic and logic operations that resolve to trivial results.
Source: Bitdefender
Before executing LummaStealer, CastleLoader performs environment and sandbox checks to determine if it’s being analyzed, and adjusts file paths and persistence locations depending on which security products are detected on the host.
Persistence is achieved by copying the malicious AutoIT script to a persistence path, copying the interpreter to a separate location, and creating an internet shortcut file on Startup that launches the interpreter with the script as an argument.
Bitdefender found that CastleLoader deliberately initiates a failed DNS lookup for a non-existent domain, resulting in a DNS failure. The cybersecurity company says that artifacts from this network behavior can be used to detect CastleLoader activity.
In a report in November, researchers at Recorded Future’s Insikt Group noted that a domain on CastleLoader’s infrastructure acted as a command-and-control (C2) server for LummaStealer, indicating an early connection between the two operations.
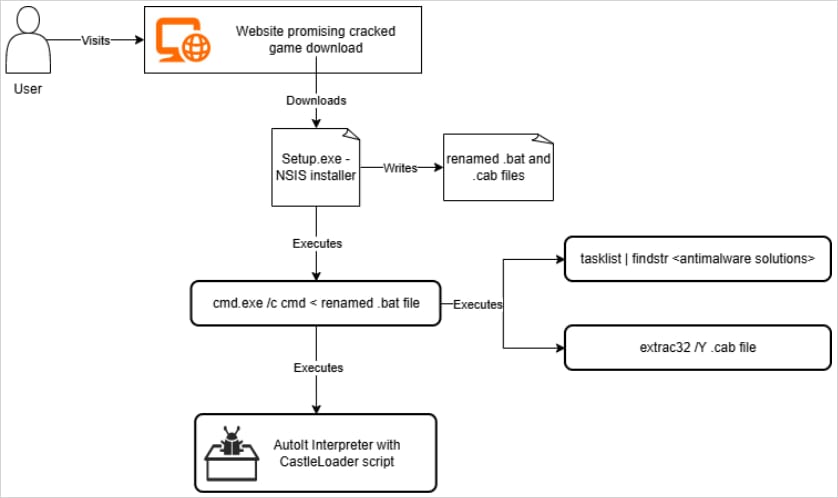
Currently, LummaStealer is distributed via multiple channels, including trojanized software installers, pirated software downloaded from fake sites or torrents, and fake media or game archives in campaigns targeting countries all over the world.
Source: Bitdefender
According to the researchers, ClickFix is a “highly effective infection vector in LummaStealer campaigns.” Users are served fake CAPTCHA or verification pages with detailed instructions to execute a malicious PowerShell command that had already been added to the clipboard.
The command ultimately retrieves a malicious script from the attacker’s server and executes it on the local machine. The payload delivered this way was CastleLoader, which, in some cases, fetched and executed the LummaStealer info-stealing malware.
To defend against this threat, Bitdefender researchers recommend users avoid downloading and executing software or media (especially if the file has a .EXE extension) from untrusted or unofficial sources.
Also, executing commands you don’t understand in PowerShell or command-line utilities as part of a website’s verification process is a red flag for malicious activity.
The general advice is to steer clear of pirated software (e.g., cracks, “unlocked” tools) and hide promoted results on Google Search by using an ad blocker.