
A SystemBC proxy malware botnet of more than 1,570 hosts, believed to be corporate victims, has been discovered following an investigation into a Gentlemen ransomware attack carried out by a gang affiliate.
The Gentlemen ransomware-as-a-service (RaaS) operation emerged around mid-2025 and provides a Go-based locker that can encrypt Windows, Linux, NAS, and BSD systems, and a C-based locker for ESXi hypervisors.
Last December, it compromised one of Romania’s largest energy providers, the Oltenia Energy Complex. Earlier this month, The Adaptavist Group disclosed a breach that Gentlemen ransomware listed on its data leak site.
Although the RaaS operation has publicly claimed around 320 victims, most of the attacks occurring this year, Check Point researchers discovered that the Gentlemen ransomware affiliates are expanding their attack toolkit and infrastructure.
During an incident response engagement, the researchers found that an affiliate for the ransomware operation tried to deploy the proxy malware for covert payload delivery.
“Check Point Research observed victim telemetry from the relevant SystemBC command‑and‑control server, revealing a botnet of over 1,570 victims, with the infection profile strongly suggesting a focus on corporate and organizational environments rather than opportunistic consumer targeting,” the researchers say in a report today.
SystemBC has been around since at least 2019 and is used for SOCKS5 tunneling. Due to its capability to deliver malicious payloads, it was quickly adopted and also to send malicious payloads. It capability to introduce payloads onto infected systems was quickly adopted by ransomware gangs.
Despite a law enforcement operation that affected it in 2024, the botnet remains active, and last year Black Lotus Labs reported that it was infecting 1,500 commercial virtual private servers (VPS) every day to funnel malicious traffic.
According to Check Point, most of the victims linked to Gentlemen’s deployment of SystemBC are located in the United States, the United Kingdom, Germany, Australia, and Romania.
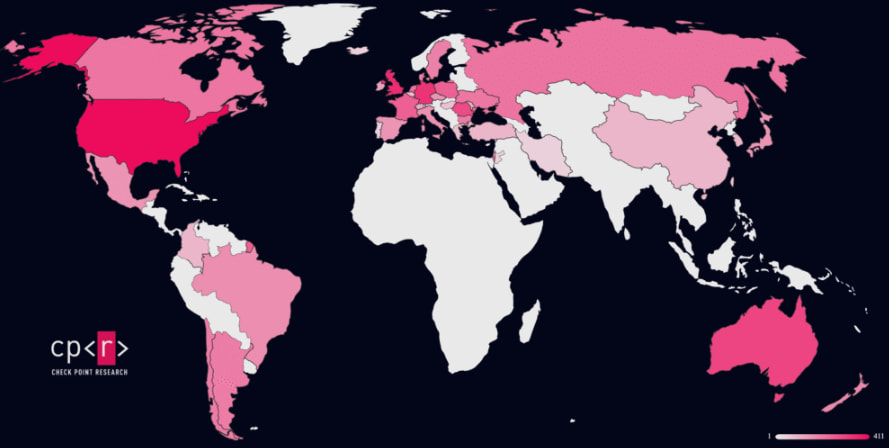
Source: Check Point
“The specific Command and Control server that was used for the communication had infected a large number of victims across the globe. It is likely that the majority of those victims are companies and organizations, given that SystemBC is typically deployed as part of human‑operated intrusion workflows rather than massive targeting,” Check Point says.
The researchers are unsure how SystemBC fits into Gentlemen ransomware’s ecosystem and could not determine if the malware was used by multiple affiliates.
Infection chain and encryption scheme
Although Check Point could not determine the initial access vector in the observed attacks, the researchers say that the Gentlemen threat actor operated from a Domain Controller with Domain Admin privileges.
From there, the attacker checked which credentials worked and conducted reconnaissance before deploying Cobalt Strike payloads to remote systems via RPC.
Lateral movement was supported by credential harvesting using Mimikatz and remote execution. The attackers staged the ransomware from an internal server and leveraged built-in propagation and Group Policy (GPO) to trigger near-simultaneous execution of the encryptor across domain-joined systems.
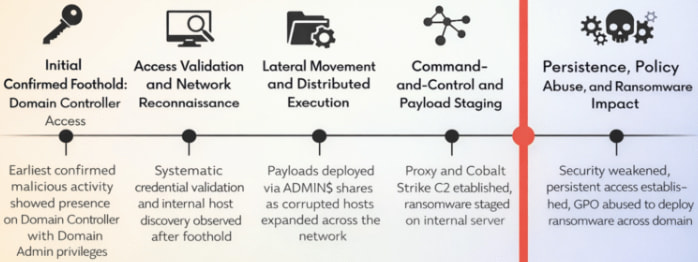
Source: Check Point
According to the researchers, the malware uses a hybrid scheme based on X25519 (Diffie–Hellman) and XChaCha20, with a random ephemeral key pair generated for each file.
Files under 1 MB are fully encrypted, while with larger files only chunks of data of about 9%, 3%, or 1% were encrypted.
Before encryption, Gentlemen ransomware terminates databases, backup software, and virtualization processes, and deletes Shadow copies and logs. The ESXi variant also shuts down VMs to ensure the disks can be encrypted.
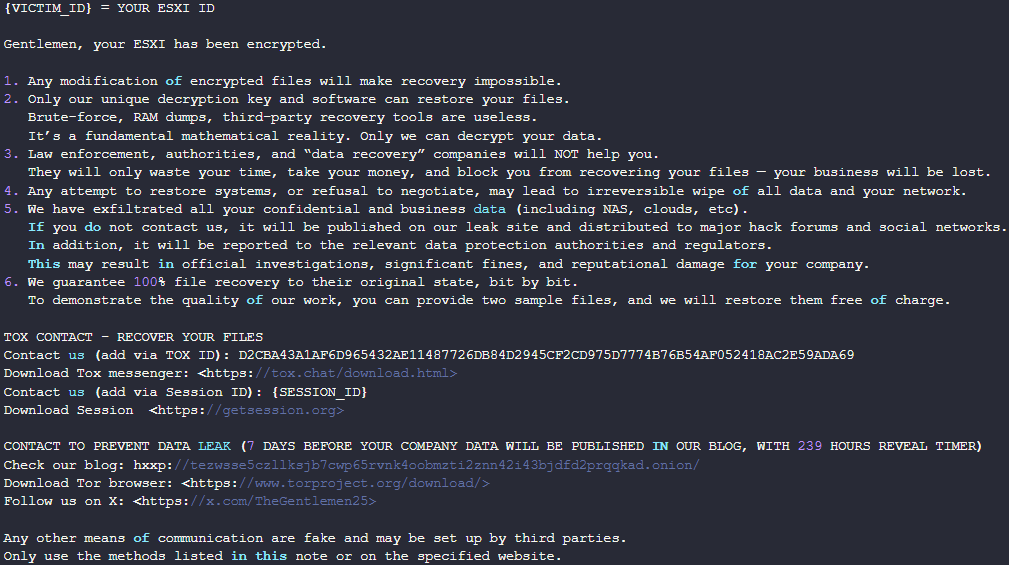
Source: Check Point
The Gentlemen ransomware doesn’t make headlines often but Check Point warns that the RaaS is quickly growing, advertising to recruit new ransomware affiliates via underground forums.
The researchers believe that using SystemBC with Cobalt Strike and the botnet of 1,570 hosts may indicate that the Gentlemen ransomware gang is now operating at a higher level, “actively integrating into a broader toolchain of mature, post‑exploitation frameworks and proxy infrastructure.”
Apart from indicators of compromise (IoCs) collected from the investigated incident, Check Point also provides signature-based detection in the form of a YARA rule to help defenders protect against such attacks.
AI chained four zero-days into one exploit that bypassed both renderer and OS sandboxes. A wave of new exploits is coming.
At the Autonomous Validation Summit (May 12 & 14), see how autonomous, context-rich validation finds what’s exploitable, proves controls hold, and closes the remediation loop.



