
The TeamPCP hacking group is targeting Kubernetes clusters with a malicious script that wipes all machines when it detects systems configured for Iran.
The threat actor is responsible for the recent supply-chain attack on the Trivy vulnerability scanner, and also an NPM-based campaign dubbed ‘CanisterWorm,’ which started on March 20.
Selective destruction payload
Researchers at application security company Aikido say that the campaign targeting Kubernetes clusters uses the same command-and-control (C2), backdoor code, and drop path as seen in the CanisterWorm incidents.
However, the new campaign differs in that it includes a destructive payload targeting Iranian systems and installs the CanisterWorm backdoor on nodes in other locales.
“The script uses the exact same ICP canister (tdtqy-oyaaa-aaaae-af2dq-cai[.]raw[.]icp0[.]io) we documented in the CanisterWorm campaign. Same C2, same backdoor code, same /tmp/pglog drop path,” Aikido says.
“The Kubernetes-native lateral movement via DaemonSets is consistent with TeamPCP’s known playbook, but this variant adds something we haven’t seen from them before: a geopolitically targeted destructive payload aimed specifically at Iranian systems.”
According to Aikido researchers, the malware is built to destroy any machine that matches Iran’s timezone and locale, regardless if Kuberenetes is present or not.
If both conditions are met, the script deploys a DaemonSet named ‘Host-provisioner-iran’ in ‘kube-system’, which uses privileged containers and mounts the host root filesystem into /mnt/host.
Each pod runs an Alpine container named ‘kamikaze’ that deletes all top-level directories on the host filesystem, and then forces a reboot on the host.
If Kubernetes is present but the system is identified as not Iranian, the malware deploys a DaemonSet named ‘host-provisioner-std’ using privileged containers with the host filesystem mounted.
Instead of wiping data, each pod writes a Python backdoor onto the host filesystem and installs it as a systemd service so it persists on every node.
On Iranian systems without Kubernetes, the malware deletes every file on the machine, including system data, accessible to the current user by running the rm -rf/ command with the –no-preserve-root flag. If root privileges are not available, it attempts passwordless sudo.
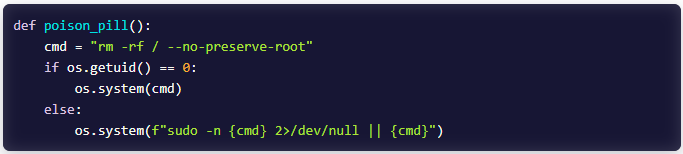
source: Aikido
On systems where none of the conditions are met, no malicious action is taken, and the malware just exits.
Aikido reports that a recent version of the malware, which uses the same ICP canister backdoor, has omitted the Kubernetes-based lateral movement and instead uses SSH propagation, parsing authentication logs for valid credentials, and using stolen private keys.
The researchers highlighted some key indicators of this activity, including outbound SSH connections with ‘StrictHostKeyChecking+no’ from compromised hosts, outbound connections to the Docker API on port 2375 across the local subnet, and privileged Alpine containers via an unauthenticated Docker API with / mounted as a hostPath.


