With practical quantum computers predicted to arrive in the next decade or so, technologists worry about the risks to encrypted data traveling over current Web protocols, but a new infrastructure proposed by an Internet standards group could future-proof against quantum attacks.
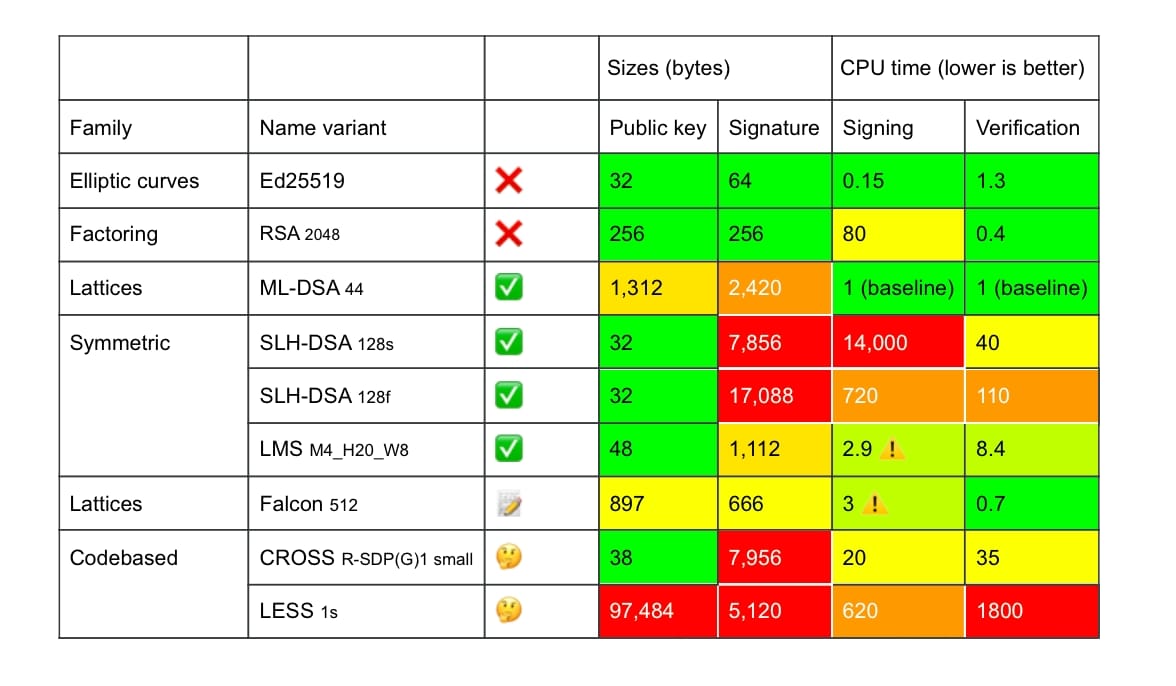
Cryptographically relevant quantum computers (CRQCs) could allow the decryption of secure traffic using HTTPS and the spoofing of secure servers. Shoring up the security of the Internet with the structures used today requires adopting post-quantum algorithms that come with significant trade-offs.
Browser makers have already adopted additions to the current Transport Layer Security (TLS) standard for securing communications against the most significant present-day quantum concern: “store now, decrypt later” (SNDL) threats, where an adversary steals data to exploit when quantum computing is available. Yet the technology does not solve other future security problems that will arise.
Typical quantum-resistant encryption algorithms, such as Module-Lattice-Based Digital Signature Algorithm (ML-DSA), result in significant increases in bandwidth and cause moderate slowdowns in establishing sessions. Worse, “middle boxes” — such as Web application gateways, load balancers, and intrusion-detection appliances — often fail with the larger certificate chains, Cloudflare found.
Enter Merkle tree certificates (MTCs), a draft specification for using efficient hash-based certificates designed to efficiently secure against post-quantum attacks. While stronger, quantum-safe encryption typically requires larger keys and more calculations, MTCs provide a very efficient way to distribute keys, requiring keys less than 10% the size of best alternative quantum-safe methods of cryptography.
Created by the Internet Engineering Task Force (IETF), the draft specification is already being tested by major Internet infrastructure providers, such as Google and Cloudflare, said Luke Valenta, senior research engineer at Cloudflare.
“MTCs work … and they are used to secure real traffic today,” he told the audience earlier this month at the Real World Crypto Symposium 2026 in Taipei, Taiwan. “They are faster than even classical signature chains … so even without quantum computers on the horizon, this would be justification to deploy them.”
Protection Before Q-Day
No one knows when practical quantum computers will arrive. Technologists have perennially predicted the necessary advances will be here in a decade or three, but that time has shortened in recent years with some breakthroughs and investment. Bill Gates argues that a quantum computer could arrive in the next three to five years, while analysts at Forrester Research predict practical business quantum computers could be here by 2030.
Because of the need to protect against SNDL attacks, government agencies and companies are already preparing by rolling out quantum-resistant algorithms. Currently, all modern browsers support Module-Lattice-Based Key-Encapsulation Mechanism (ML-KEM), adopted by the US National Institute of Standards and Technology (NIST) as FIPS 203, one of its post-quantum encryption standards. Currently, two-thirds of non-bot traffic processed by Cloudflare already uses TLS with post-quantum encryption, up from 38% a year ago, according to Cloudflare Radar.

In the past six months, Cloudflare has seen non-bot usage of post-quantum encryption rise to two-thirds of requests, up from 40%. Source: Cloudflare Radar
Yet post-quantum encryption key exchange using ML-KEM only protects against SNDL attacks. Following the creation of a CRQC, the system could still be used to impersonate websites, making a different type of protection necessary before such computers become viable.
Foiling such attacks is the promise of Merkle tree certificates. Merkle trees, or hash trees, are an efficient way of organizing verification data. Data is divided up into blocks, with the hash of each data block stored in a leaf node. The non-leaf nodes of the tree hold the hash of its child nodes. Using the data structure, the tree can quickly determine whether data was changed and, if so, in which data block.
Merkle tree certificates use this same approach. Not only do MTCs reduce the size of post-quantum certificates, but they also decrease latency and have transparency as a feature, not an added-on requirement. Trying to use other post-quantum alternatives, such as ML-DSA, allows servers to be authenticated, but results in a significant increase in overhead.
At present, loading the certificate from a page view on a site requires 3.1 KB per connection, but ML-DSA would cause that to blow up to 14.7 KB per connection, says Brian Trzupek, senior vice president of product at certificate authority DigiCert. MTCs only require approximately 840 bytes per page load, more efficient than even prequantum certificates. Because most sites acquire assets and resources from other domains — 21 different TLS domains for Dark Reading, for example — that quickly results in significant overhead, he says.
“It’s this huge increase of data that’s going on,” Trzupek says. “So that’s slowing things down, that’s making pages load slower, congesting networks, all [that] kind of stuff.”
For those reasons, Google announced its intent to support MTCs in the Chrome browser, saying the company has begun to work with Cloudflare on a feasibility study.
Bonus: Better Web Performance
A typical TLS handshake transmits two public keys and five signatures. With classical encryption methods, that requires about 1.2 kilobytes to be transferred. With ML-DSA-44, which is the best option for post-quantum Web encryption today, that grows to about 14.7 kilobytes. The Chrome security teams concluded that adding more than 7 kilobytes to Web communications will overburden the Web and cause problems for users and Internet infrastructure, Cloudflare’s Valenta said in his RWC presentation.
There are two types of Merkle tree certificates: landmark certificates and standalone certificates. Landmark certificates require preloading of information on the chain of hashes for each certificate authority that provides an inclusion proof for CA’s Merkle tree root. If the browser does not have up-to-date landmarks, then it will download a standalone certificate, which requires more data.
Google is currently in Phase 1 of its effort to test MTCs using conventional cryptography, a worst-case scenario compared to post-quantum encryption, Google researchers say.
“Despite this, experimental MTCs are still consistently faster and require fewer bytes transferred than their conventional counterparts, and we expect this lead will grow significantly when using PQ signature algorithms in Phases 2 and 3,” they stated in comments to Dark Reading.
In the initial pilots, the landmark certificate files include 168 landmarks, each one consisting of a few hashes, making the client-side storage certainly greater but not too much greater, Valenta said at RWC.
“There is definitely a trade-off with more storage on the client side, and there are lots of parameters — currently, in the experiment, we have landmarks being generated every hour, and that might be closer to a day,” he says. “On the Chrome side, they are very sensitive to this issue.”
Trade-Offs in the Background
Not everything is easier with Merkle tree certificates. While certificate transparency — which requires assiduous logging under the current infrastructure — will essentially be free because it is part of the issuance process, Internet infrastructure companies must manage the indices of millions of certificates, making sure that the system does not reuse secret keys.
That said, key hashes are smaller, reducing those logs by two orders of magnitude. In addition, older entries can be discarded once they have expired without invalidating the logs, according to the IETF draft specification.
For Internet infrastructure providers, the transition will likely require updates to software and rigorous testing to ensure that the Internet’s “middle boxes” do not block MTCs. For browser users, however, the transition should be invisible. Website managers should need to do little, aside from adopting the latest version of their preferred Web server, Google researchers told Dark Reading.
“Our deployment strategy ensures that the adoption of MTCs will not cause breakage for websites, even if they don’t take active steps to adopt MTCs,” they said in emailed comments. But major server software providers will likely update to support MTCs, “which will allow a smooth transition for sites.”