
Threat actors using a previously undocumented phishing-as-a-service (PhaaS) platform called “VENOM” are targeting credentials of C-suite executives across multiple industries.
The operation has been active since at least last November and appears to target specific individuals who serve as CEOs, CFOs, or VPs at their companies.
VENOM also seems to be closed access, as it has not been promoted on public channels and underground forums, thus reducing its exposure to researchers.
The VENOM attack chain
The phishing emails, observed by researchers at cybersecurity company Abnormal, impersonated Microsoft SharePoint document-sharing notifications as part of internal communication.
The messages are highly personalized and include random HTML noise such as fake CSS classes and comments. The attacker also injects fake email threads tailored to the target, increasing credibility.
A QR code rendered in Unicode is provided for the victim to scan for access. The trick is designed to bypass scanning tools and shift the attack to mobile devices.
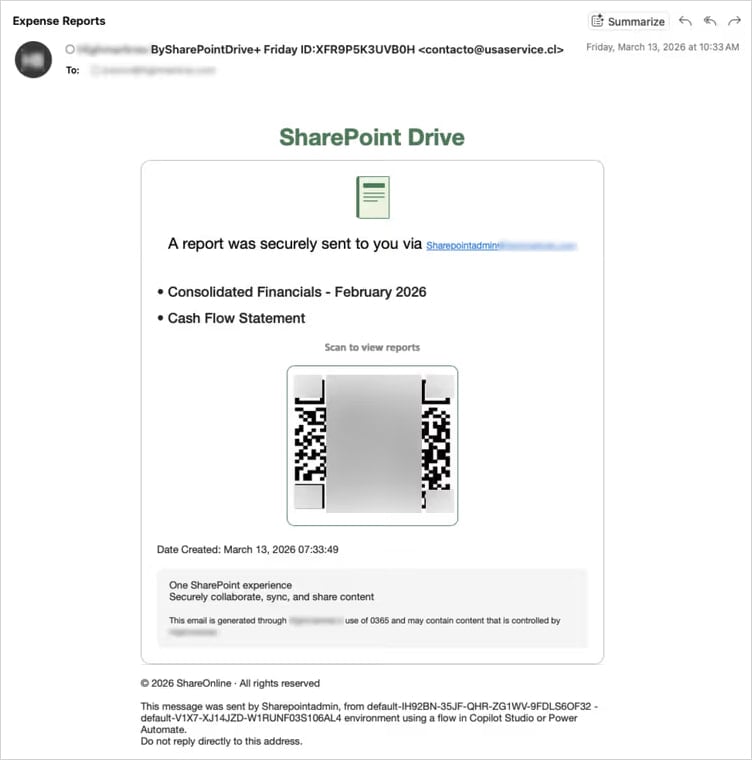
Source: Abnormal
“The target’s email address is double Base64-encoded in the URL fragment—the portion after the # character,” Abnormal researchers explain.
“Fragments are never transmitted in HTTP requests, making the target’s email invisible to server-side logs and URL reputation feeds.”
When the victim scans the QR code, they are taken to a landing page that serves as a filter for security researchers and sandboxed environments, ensuring that only real targets are redirected to the phishing platform. Users outside the threat actor’s interest are redirected to legitimate websites to reduce suspicion.
Those who pass the tests are taken to a credential-harvesting page that proxies a Microsoft login flow in real time, relaying credentials and multi-factor authentication (MFA) codes to Microsoft APIs and capturing the session token.
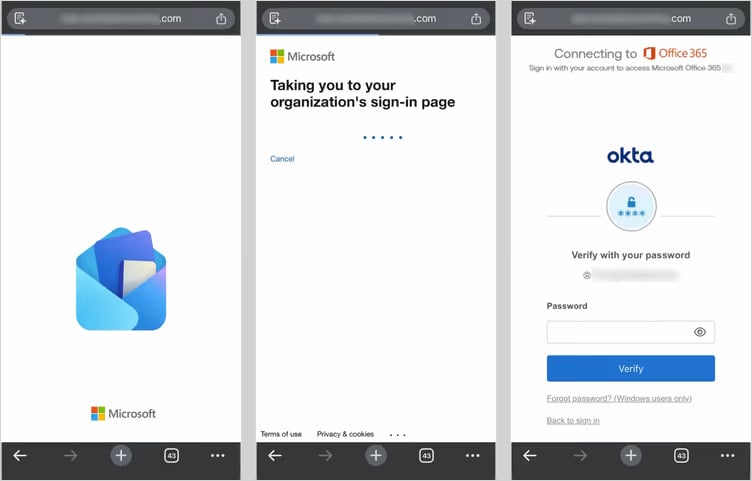
Source: Abnormal
Apart from the adversary-in-the-middle (AiTM) method, Abnormal has also observed a device-code phishing tactic in which the victim is tricked into approving access to their Microsoft account for a rogue device.
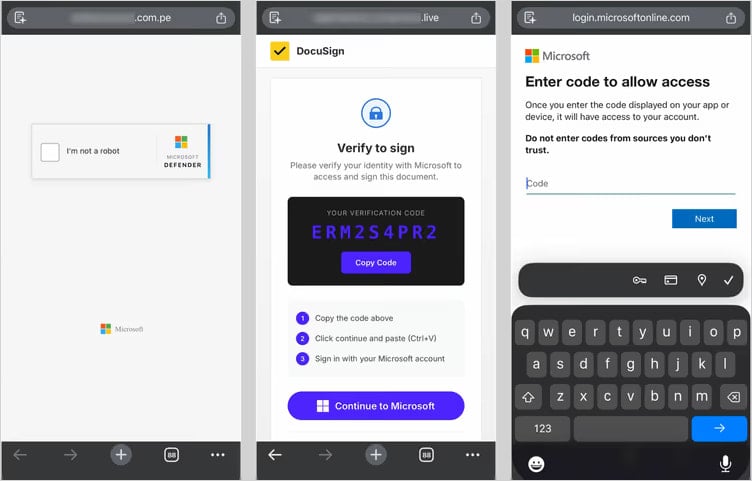
Source: Abnormal
This method has become very popular over the past year due to its effectiveness and resistance to password resets, with at least 11 phishing kits currently offering it as an option.
In both methods, VENOM quickly establishes persistent access during the authentication process. In the AiTM flow, it registers a new device on the victim’s account. In the device code flow, it obtains a token that also provides access to the account.
The researchers note that MFA is no longer sufficient as a defense. C-suite executives should use FIDO2 authentication, disable the device code flow when not needed, and block token abuse by implementing stricter conditional access policies.



