
IPIDEA, one of the largest residential proxy networks used by threat actors, was disrupted earlier this week by Google Threat Intelligence Group (GTIG) in collaboration with industry partners.
The action included taking down domains associated with IPIDEA services, infected device management, proxy traffic routing. Additionally, intelligence has been shared on the IPIDEA software development kits (SDK) that distributed the proxying tool.
The operators of IPIDEA advertised it as a VPN service that “encrypts your online traffic and hides your real IP address,” used by 6.7 million users worldwide.
Residential proxy networks use home user or small business IP addresses to route traffic after compromising devices on the network. Typically, the infection occurs through trojanized apps and software posing as useful utilities.
In a court letter, Google explains that threat actors use residential proxies in various malicious activities, such as account takeovers, fake account creation, credential theft, and sensitive information exfiltration.
“By routing traffic through an array of consumer devices all over the world, attackers can mask their malicious activity by hijacking these IP addresses. This generates significant challenges for network defenders to detect and block malicious activities,” Google says in a report today.
In the case of IPIDEA, GTIG observed a range of malicious activity, with more than 550 distinct threat groups using its exit nodes in a single week, including actors from China, Iran, Russia, and North Korea.
The observed activities included access to victim SaaS platforms, password spraying, botnet control, and infrastructure obfuscation. Previously, Cisco Talos linked IPIDEA to large-scale brute-forcing attacks targeting VPN and SSH services.
IPIDEA infrastructure also supported record-breaking DDoS botnets such as Aisuru and Kimwolf.
Google says IPIDEA enrolled devices using at least 600 trojanized Android apps that embedded proxying SDKs (Packet SDK, Castar SDK, Hex SDK, Earn SDK), and over 3,000 trojanized Windows binaries posing as OneDriveSync or Windows Update.
Source: Google
IPIDEA promoted several VPN and proxying apps to Android users that secretly turned their devices into proxy exit nodes without their knowledge or consent.
According to Google, IPIDEA operators ran at least 19 residential proxy businesses that pretended to be legitimate services and sold access to devices compromised with the BadBox 2.0 malware. Some of the associate brands are listed below:
-
360 Proxy (360proxy\.com)
-
922 Proxy (922proxy\.com)
-
ABC Proxy (abcproxy\.com)
-
Cherry Proxy (cherryproxy\.com)
-
Door VPN (doorvpn\.com)
-
Galleon VPN (galleonvpn\.com)
-
IP 2 World (ip2world\.com)
-
Ipidea (ipidea\.io)
-
Luna Proxy (lunaproxy\.com)
-
PIA S5 Proxy (piaproxy\.com)
-
PY Proxy (pyproxy\.com)
-
Radish VPN (radishvpn\.com)
-
Tab Proxy (tabproxy\.com)
- Aman VPN (defunct)
Despite the multiple brands, all services are connected to a centralized infrastructure under the single control of IPIDEA operators, who remain unidentified.
Google Play Protect now automatically detects and blocks on up-to-date, certified Android devices the applications that include IPIDEA-related SDKs.
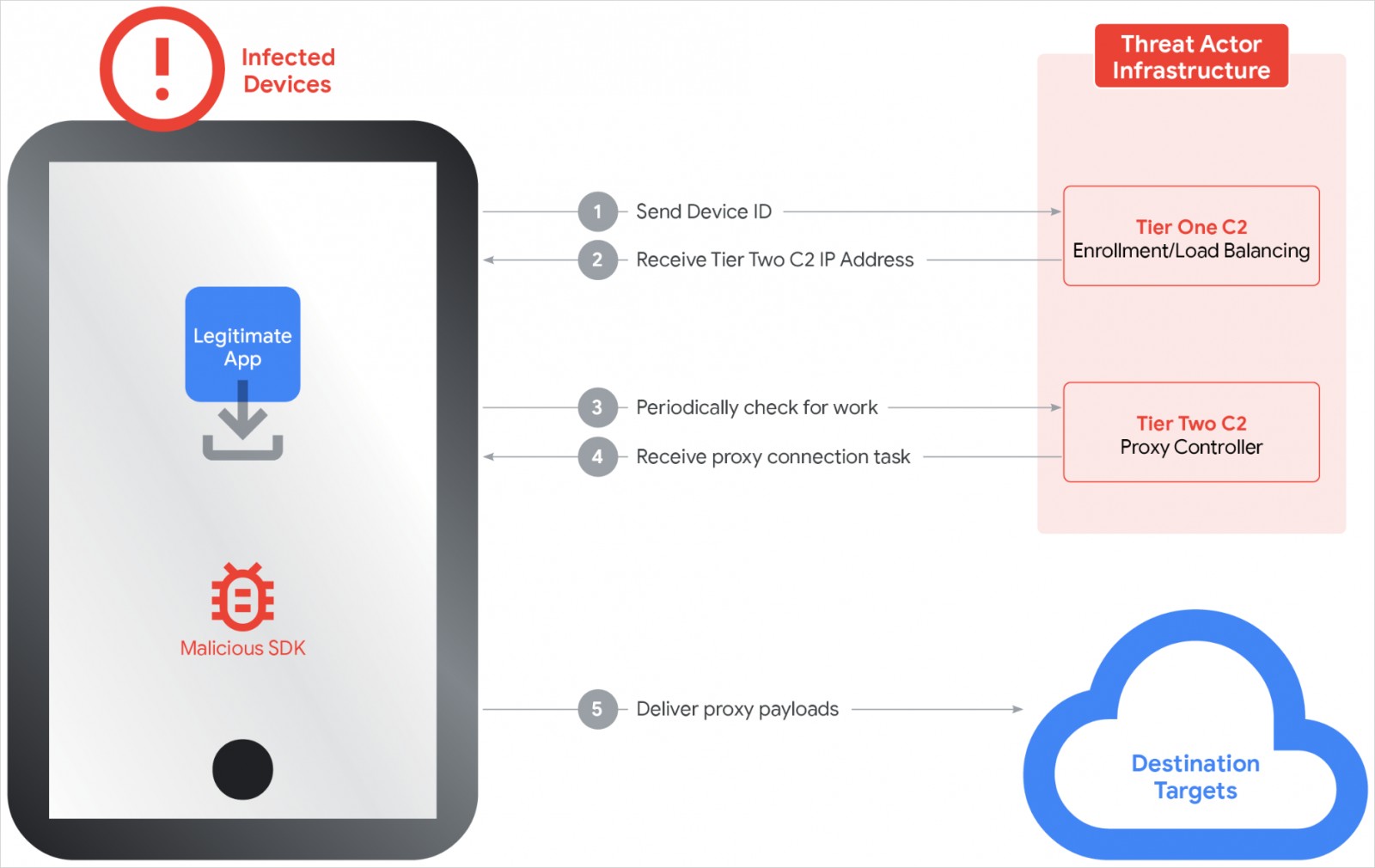
Regarding its structure, Google explains that IPIDEA operated on a two-tier command-and-control (C2) system. The first tier provides configuration and timing, and the node lists for the second tier.
According to the researchers, the second tier comprised roughly 7,400 servers that assigned proxying tasks and relayed traffic.
Source: Google
Google researchers note that the operators of the networks also offered free VPN services through apps that provided the advertised fucntionality. However, the devices were added to the IPIDEA network, acting as an exit node.
Although GTIG and partners’ action likely had a significant impact on IPIDEA’s operations, the threat actor may try to rebuild its infrastructure. Currently, there are no arrests or indictments announced.
Users should remain cautious about apps that offer payment in exchange for bandwidth, as well as free VPN and proxy apps from non-reputable publishers.



