Ransomware’s Real-World Impact Across Industries
In February 2026, the University of Mississippi Medical Center (UMMC) fell victim to a ransomware attack. The incident took the Epic electronic health record system offline across 35 clinics and more than 200 telehealth sites, forcing the cancellation of chemotherapy appointments and the postponement of non-emergency surgeries. Medical staff were required to revert to paper-based workflows, leaving countless patients to bear the consequences.
UMMC is far from an isolated case. According to recent data, 93% of U.S. healthcare organizations experienced at least one cyberattack in 2025, and 72% of respondents reported that at least one incident directly disrupted patient care.
The manufacturing and financial sectors are equally exposed. In February 2026, payment processing network BridgePay suffered a ransomware attack that took its APIs, virtual terminals, and payment pages completely offline. Across all industries, publicly disclosed ransomware attacks surged 49% year-over-year in 2025, reaching 1,174 confirmed incidents.
As hospitals halt treatments, financial institutions freeze transactions, and manufacturers shut down production lines, ransomware has firmly established itself as a direct business risk with tangible operational consequences.
The Evolution of Ransomware: Double Extortion
Early ransomware operated on a straightforward premise: infiltrate a system, encrypt files, and demand payment in exchange for the decryption key. As organizations began countering this tactic by restoring from backups rather than paying ransoms, threat actors responded by developing a more lucrative model — double extortion.
In a double extortion attack, adversaries first exfiltrate sensitive files — such as patient records and billing data — before encrypting the target system. Victims are then pressured on two fronts: pay to receive the decryption key, or face public exposure of the stolen data.
Backups alone are insufficient against this model. Since attackers already possess the data, refusing to pay the ransom can result in the public release of sensitive files, exposing organizations to significant business losses and regulatory consequences.
The threat landscape has continued to escalate, with triple extortion cases on the rise — a tactic in which attackers directly contact a victim organization’s customers or partners to apply additional pressure.
As of 2025, 124 active ransomware groups have been identified, 73 of which are newly emerged.
The proliferation of AI-powered tools has lowered the barrier to entry for cybercrime, making ransomware capabilities increasingly accessible to less sophisticated actors.
D.AMO makes stolen data unreadable.
See how D.AMO defends against every stage of a ransomware attack.
A Defense Architecture for Multi-Extortion Threats
The rise of multi-extortion ransomware fundamentally changes the assumptions underlying traditional defense strategies. Perimeter-based prevention alone is no longer sufficient.
Organizations need a security posture that protects data from being weaponized after a breach — rendering exfiltrated data unreadable, blocking ransomware from accessing files in the first place, and enabling rapid recovery even when an attack succeeds.
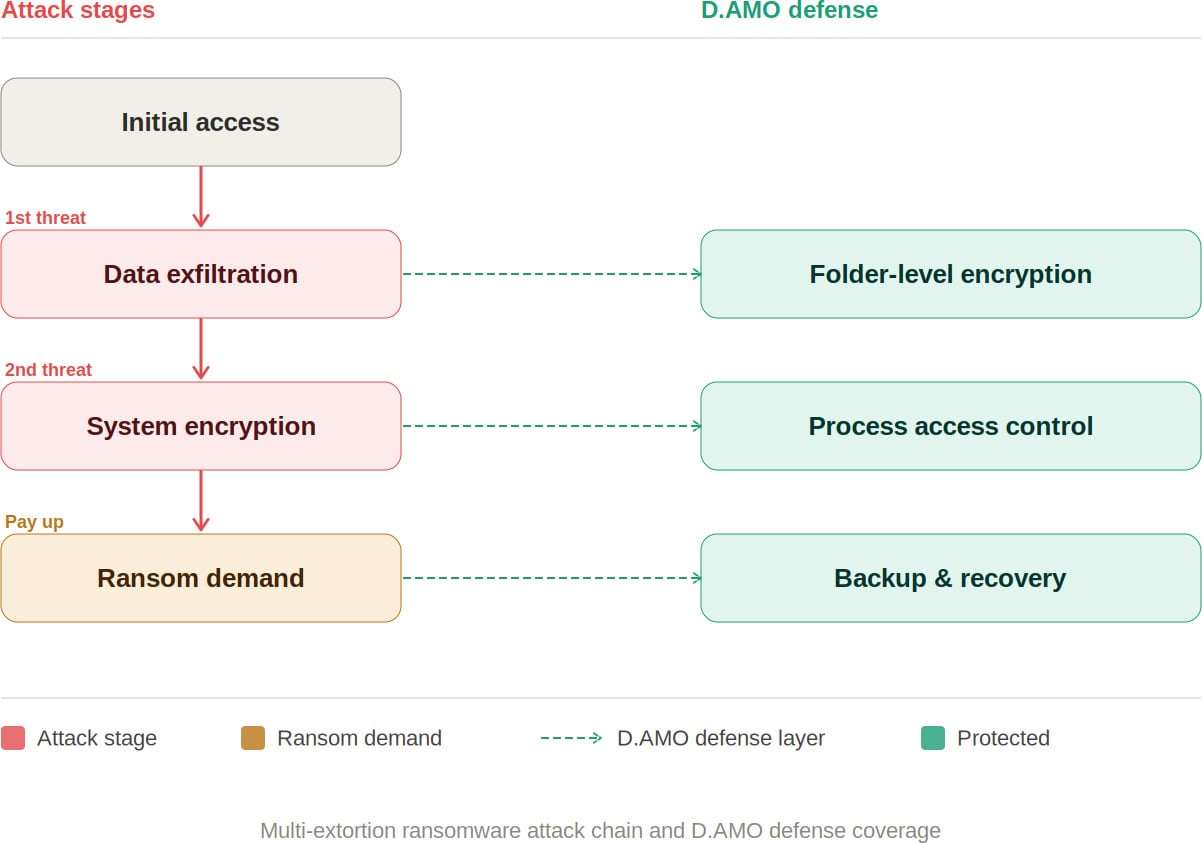
D.AMO: Blocking Every Stage of a Ransomware Attack
D.AMO, developed by Penta Security, is an encryption-based data protection platform designed to address every phase of a multi-extortion ransomware attack. It delivers integrated encryption, access control, and backup recovery across on-premises and cloud environments.
By applying file encryption and process-based access control technologies, D.AMO protects critical data stored on servers and PCs — safeguarding sensitive information against malicious programs through robust access enforcement. D.AMO’s key capabilities are as follows:
Folder-Level File Encryption
D.AMO KE encrypts all files within administrator-designated folders at the OS level. Deployable via an installer without source code modification, it operates using kernel-level encryption technology, enabling fast and secure encryption on existing systems with no disruption to the user experience.
Encryption policies are applied at the folder level, ensuring consistent protection with minimal operational overhead. Critically, even if an attacker exfiltrates sensitive data, the files remain encrypted — neutralizing the data exposure threat that is central to double extortion.
Access Control
D.AMO KE enforces strict access control over processes and OS users, permitting only explicitly authorized access. Ransomware and other malicious applications are automatically blocked from accessing encrypted folders, preventing unauthorized file manipulation.
All blocked activity is recorded through an audit log function and can be reviewed centrally via D.AMO Control Center.
Backup and Recovery
Even in the event of a successful attack, organizations can resume operations through an independently managed recovery system. With D.AMO in place, the ability to restore from backup significantly reduces dependence on decryption key negotiations with threat actors.
As multi-extortion tactics become the norm, neutralizing the data attackers seek to exploit has become a strategic priority. Organizations need the ability to render exfiltrated data unreadable, prevent ransomware from accessing files, and recover rapidly when incidents occur.
D.AMO addresses each stage of a ransomware attack within a single integrated platform — combining encryption, process-based access control, and backup recovery into a unified line of defense.
Want to learn more? Download the D.AMO Data Sheet.
Sponsored and written by Penta Security.