Threat actors are exploiting the recent Claude Code source code leak by using fake GitHub repositories to deliver Vidar information-stealing malware.
Claude Code is a terminal-based AI agent from Anthropic, designed to execute coding tasks directly in the terminal and act as an autonomous agent, capable of direct system interaction, LLM API call handling, MCP integration, and persistent memory.
On March 31, Anthropic accidentally exposed the full client-side source code of the new tool via a 59.8 MB JavaScript source map included by accident in the published npm package.
The leak contained 513,000 lines of unobfuscated TypeScript across 1,906 files, revealing the agent’s orchestration logic, permissions, and execution systems, hidden features, build details, and security-related internals.
The exposed code was rapidly downloaded by a large number of users and published on GitHub, where it was forked thousands of times.
According to a report from cloud security company Zscaler, the leak created an opportunity for threat actors to deliver the Vidar infostealer to users looking for the Claude Code leak.
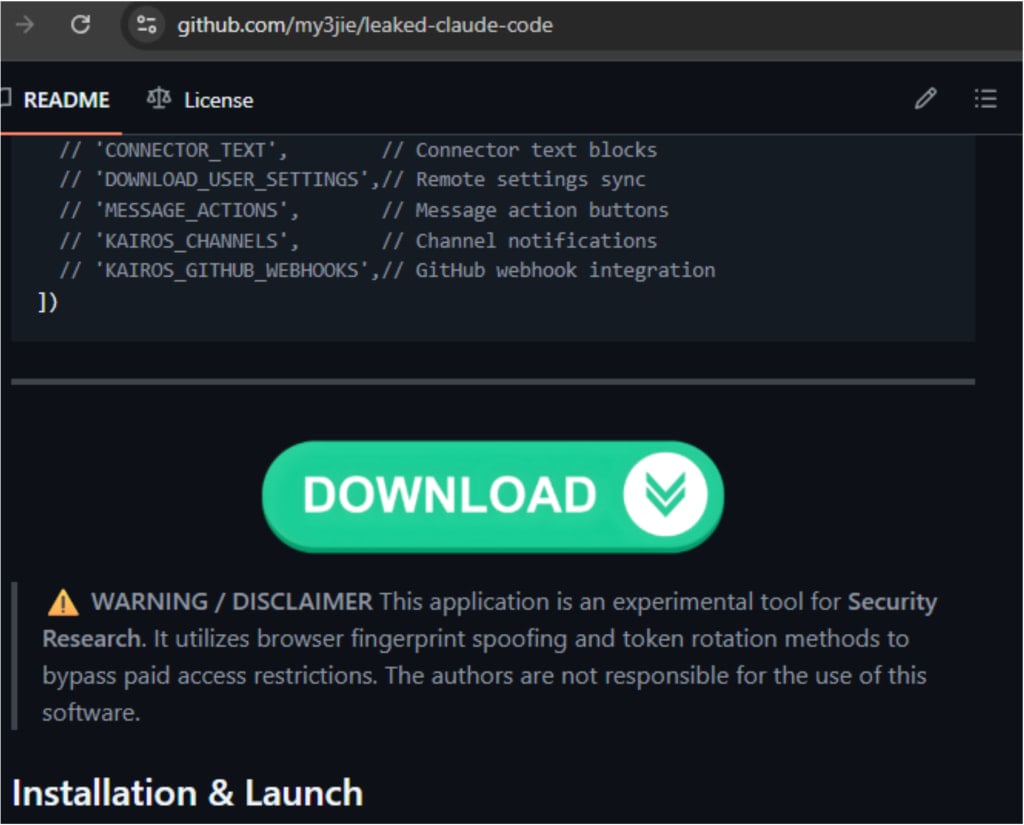
The researchers found that a malicious GitHub repository published by user “idbzoomh” posted a fake leak and advertised it as having “unlocked enterprise features” and no usage restrictions.
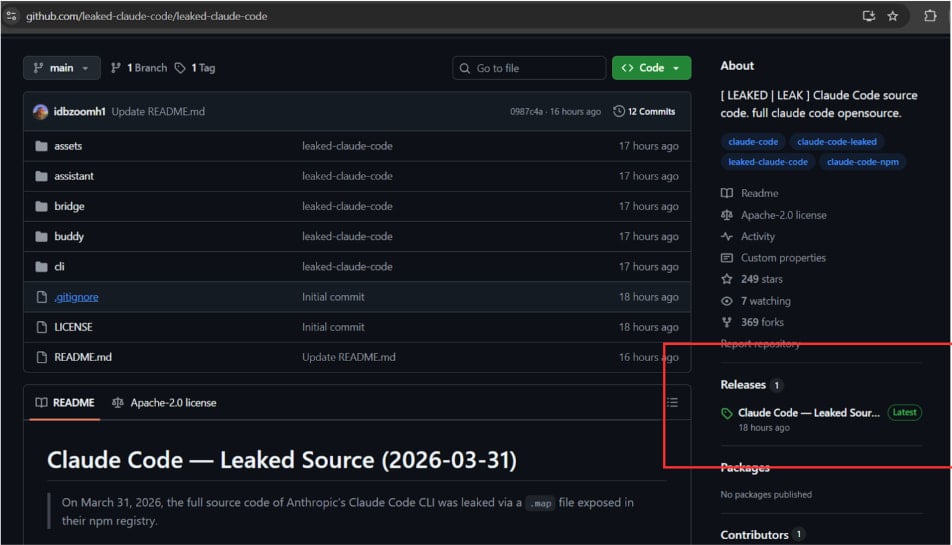
Source: Zscaler
To drive as much traffic to the bogus leak, the repository is optimized for search engines and is shown among the first results on Google Search for queries like “leaked Claude Code.”
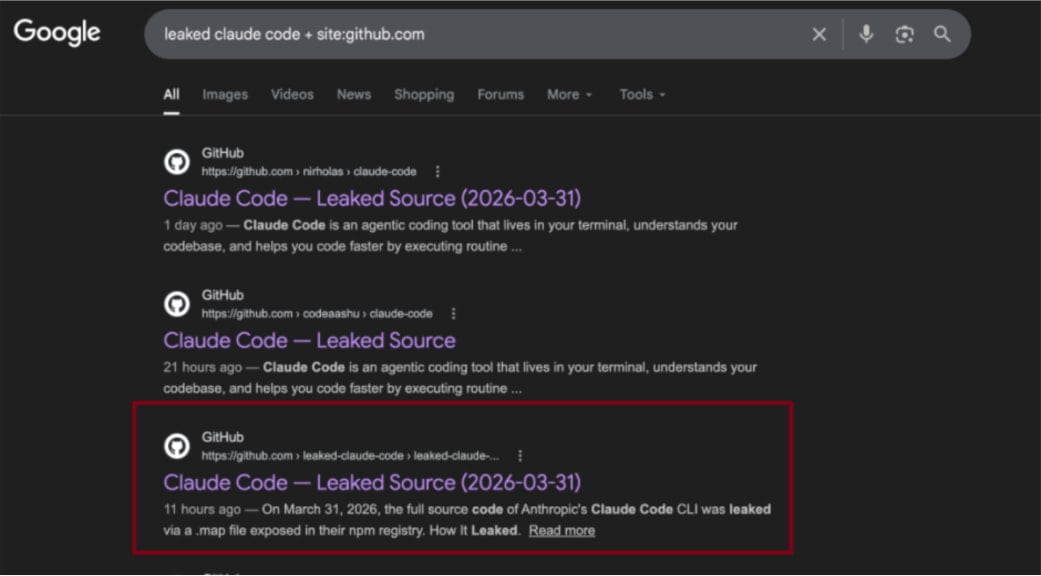
Source: Zscaler
According to the researchers, curious users download a 7-Zip archive that contains a Rust-based executable named ClaudeCode_x64.exe. When launched, the dropper deploys Vidar, a commodity information stealer, along with the GhostSocks network traffic proxying tool.
Zscaler discovered that the malicious archive is updated frequently, so other payloads may be added in future iterations.
The researchers also spotted a second GitHub repository with identical code, but it instead shows a ‘Download ZIP’ button that wasn’t functional at the time of analysis. Zscaler estimates it is operated by the same threat actor who likely experiments with delivery strategies.
Source: Zscaler
Despite the platform’s defenses, GitHub has often been used to distribute malicious payloads disguised in various ways.
In campaigns in late 2025, threat actors targeted inexperienced researchers or cybercriminals with repositories claiming to host proof-of-concept (PoC) exploits for recently disclosed vulnerabilities.
Historically, attackers were quick to capitalize on widely publicized events in the hope of opportunistic compromises.