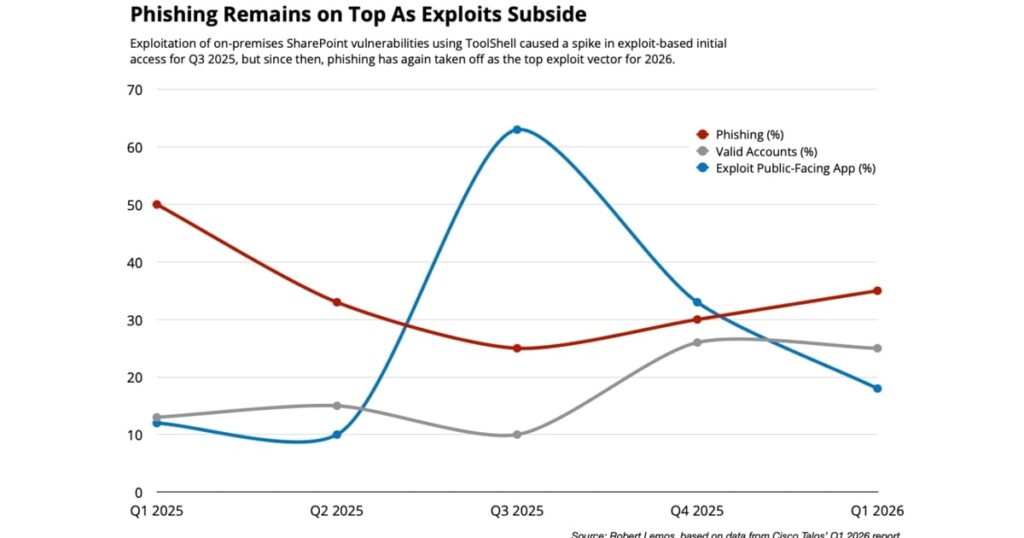
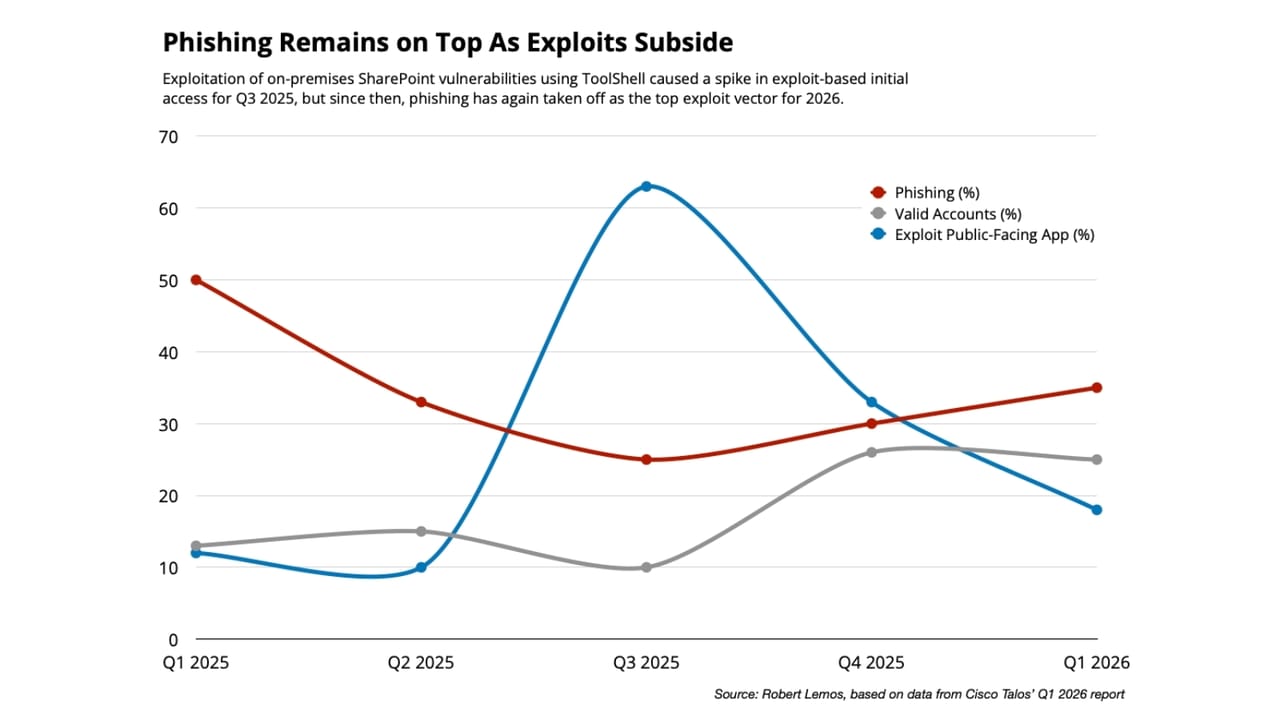
Powered by attackers’ AI usage, phishing attacks have surged back to become the top vector for initial access in incident-response engagements during the first quarter of the year, overtaking exploitation of external vulnerabilities as the top method of compromise.
That’s according to Cisco Talos’ IR Trends Q1 2026 report published this week, which found that overall, more than a third of compromises (35%) the team investigated last quarter started as a successful phishing attack. Attackers used valid accounts in 24% of cases and exploited public-facing applications in another 18%, according to data from the report.
The data highlights the effectiveness of email lures written, and usually personalized, by AI systems, says Nick Biasini, senior technical leader at Cisco Talos.
“We gave everyone the ability to write very convincing phishing emails all of a sudden, and not just very convincing emails, but very convincing emails in a wide variety of languages,” he explains. “That is really starting to show up in a lot of our data.”
Cisco is not the only company to see the surge in AI-powered phishing attacks. In December 2025, human-risk management platform Hoxhunt saw the AI-generated share of phishing attacks jump from 4% to 56% during the holiday season, dropping only slightly to 40% in January, according to a report published by the firm.
AI has resulted in more native sounding email lures, greater personalization, and cleaner formatting, making both filtering and human detection more difficult, says Mika Aalto, co-founder and CEO at the Helsinki-based firm.
“No question, the threat landscape has shifted,” he says.
More Signs of AI Tooling in Cyberattack Infection Flows
Incident responders have also seen more diversity in phishing lures. A year ago, cyberattackers would send the same email to 10 different people before switching it up and changing the content of the email — and usually, those changes were only slight. Now, that number is down to 1.8 emails per campaign, according to Erich Kron, CISO advisor at human-risk management firm KnowBe4. Rapidly changing emails, known as polymorphic phishing, has become turbo-charged as attackers increasingly adopt AI tools, he says.
“We’re attributing this absolutely to AI,” he says. “Nobody’s sitting back at their keyboard [manually] changing payloads on every single message they’re sending out.”
Microsoft data meanwhile also shows that AI has led to more convincing phishing attacks. The company has seen clickthrough rates for AI-assisted phishing reach 54%, up from an average of 12%.
Often, the targets of a phishing attack are the legitimate credentials of privileged users: both Cisco Talos and KnowBe4 have seen an increase in phishing messages that specifically target privileged users, such as system administrators, executives, and accounting teams.
“Identity is a huge, huge target,” Biasini says. “As an adversary, I don’t want to use an exploit. I would much rather compromise your email account or compromise your credentials, get into your environment and be able to operate in a much more covert manner, to hopefully inflict some financial gain.”
Google Mandiant’s investigations, for example, found that 83% of initial-access vectors exploited identity in some way, including a third of attacks using phishing techniques.
Cyberattacker Crosshairs on Vulnerable Infrastructure
The abuse of legitimate services — from Gmail accounts to Docusign, from Outlook to Salesforce — has also made phishing harder to discern from legitimate email. Usually, phishing emails come from domains that have implemented email authentication technology, such as Domain-based Message Authentication, Reporting and Conformance (DMARC), giving the message a veneer of legitimacy. Thus, attackers bypass the initial defenses, says Hoxhunt’s Aalto.
“Hiding malicious links and messages in notifications from legitimate platforms is getting increasingly popular because it’s effective and harder to detect,” he says. “When phishing links lead to trusted cloud tools, collaboration platforms, or no-code services, the activity looks normal on the surface. That makes detection harder because users are no longer looking for red flags in grammar and mismatched URLs.”
While multifactor authentication (MFA) is a critical component of protecting workers’ online identities and access, companies should not rely on it exclusively. More than a third of attacks (35%) investigated by Cisco Talos involved MFA weaknesses, the company stated in its report.
To help improve defenses, companies should experiment with and invest in deploying AI wherever it makes sense, Cisco’s Biasini says.
“If your attackers are going to be leaning heavily on AI, you need to probably do the same,” he says. “Start looking for those weaknesses, leverage your own AI capabilities to start fixing the problems that potentially could be there, because if one AI agent can find it, then multiple AI agents theoretically could find it as well.”