A high-severity security flaw in LMDeploy, an open-source toolkit for compressing, deploying, and serving LLMs, has come under active exploitation in the wild less than 13 hours after its public disclosure.
The vulnerability, tracked as CVE-2026-33626 (CVSS score: 7.5), relates to a Server-Side Request Forgery (SSRF) vulnerability that could be exploited to access sensitive data.
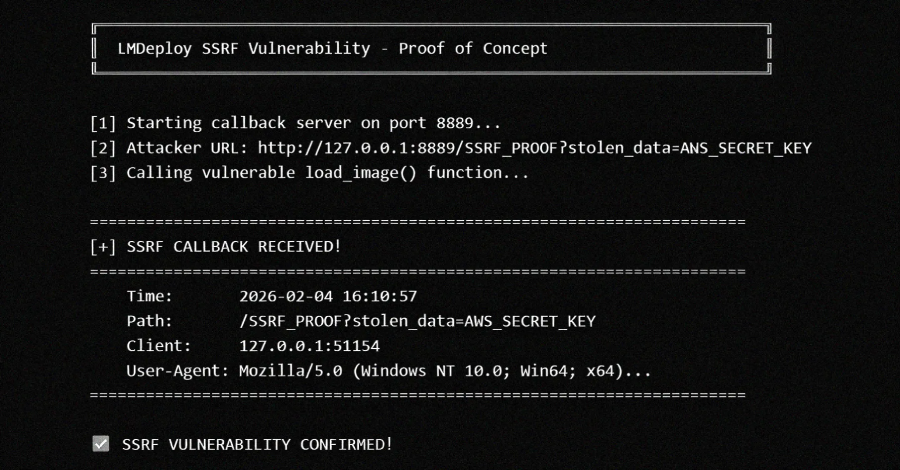
“A server-side request forgery (SSRF) vulnerability exists in LMDeploy’s vision-language module,” according to an advisory published by the project maintainers last week. “The load_image() function in lmdeploy/vl/utils.py fetches arbitrary URLs without validating internal/private IP addresses, allowing attackers to access cloud metadata services, internal networks, and sensitive resources.”
The shortcoming affects all versions of the toolkit (0.12.0 and prior) with vision language support. Orca Security researcher Igor Stepansky has been credited with discovering and reporting the bug.
Successful exploitation of the vulnerability could permit an attacker to steal cloud credentials, reach internal services that aren’t exposed to the internet, port scan internal networks, and create lateral movement opportunities.
Cloud security firm Sysdig, in an analysis published this week, said it detected the first LMDeploy exploitation attempt against its honeypot systems within 12 hours and 31 minutes of the vulnerability being published on GitHub. The exploitation attempt originates from the IP address 103.116.72[.]119.
“The attacker did not simply validate the bug and move on. Instead, over a single eight-minute session, they used the vision-language image loader as a generic HTTP SSRF primitive to port-scan the internal network behind the model server: AWS Instance Metadata Service (IMDS), Redis, MySQL, a secondary HTTP administrative interface, and an out-of-band (OOB) DNS exfiltration endpoint,” it said.
The actions undertaken by the adversary, detected on Apr 22, 2026, at 03:35 a.m. UTC, unfolded over 10 distinct requests across three phases, with the requests switching between vision language models (VLMs) such as internlm-xcomposer2 and OpenGVLab/InternVL2-8B to likely avoid raising any suspicion –
- Target AWS IMDS and Redis instances on the server.
- Test egress with an out-of-band (OOB) DNS callback to requestrepo[.]com to confirm the SSRF vulnerability can reach arbitrary external hosts, followed by enumerating the API surface.
- Port scan the loopback interface (“127.0.0[.]1”)
The findings are yet another reminder of how threat actors are closely watching new vulnerability disclosures and exploiting them before downstream users can apply the fixes, even in cases where no proof-of-concept (PoC) exploits exist at the time of the attack.
“CVE-2026-33626 fits a pattern that we have observed repeatedly in the AI-infrastructure space over the past six months: critical vulnerabilities in inference servers, model gateways, and agent orchestration tools are being weaponized within hours of advisory publication, regardless of the size or extent of their install base,” Sysdig said.
“Generative AI (GenAI) is accelerating this collapse. An advisory as specific as GHSA-6w67-hwm5-92mq, which includes the affected file, parameter name, root-cause explanation, and sample vulnerable code, is effectively an input prompt for any commercial LLM to generate a potential exploit.”
WordPress Plugins and Internet-Exposed Modbus Devices Targeted
The disclosure comes as threat actors have also been spotted exploiting vulnerabilities in two WordPress plugins – Ninja Forms – File Upload (CVE-2026-0740, CVSS score: 9.8) and Breeze Cache (CVE-2026-3844, CVSS score: 9.8) – to upload arbitrary files to susceptible sites, which result in arbitrary code execution and complete takeover.
Unknown attackers have also been linked to a global campaign targeting internet-exposed, Modbus-enabled programmable logic controllers (PLCs) from September to November 2025 that spanned 70 countries and 14,426 distinct targeted IPs, most of which are located in the U.S., France, Japan, Canada, and India. A subset of these requests has been found to emanate from sources geolocated to China.
“The activity blended large-scale automated probing with more selective patterns that suggest deeper device fingerprinting, disruption attempts, and potential manipulation paths when PLCs are reachable from the public internet,” Cato Networks researchers said. “Many source IPs had low or zero public reputation scores, consistent with fresh or rotating scanning hosts.”