Apple’s AirTag is designed to help users track lost items by relying on a vast network of nearby Apple devices. New research shows that this same system can be manipulated to display locations where an AirTag has never been.
Relaying an AirTag’s BLE advertisments over the Internet injects false location reports into the Find My system
How the attack works
The Find My network depends on Bluetooth Low Energy (BLE) signals broadcast by AirTags. When an iPhone or other Apple device detects one of these signals, it sends an encrypted location report to Apple. The owner then sees that location in the Find My app. The encryption protects identities but also prevents the system from checking whether the reported location is genuine.
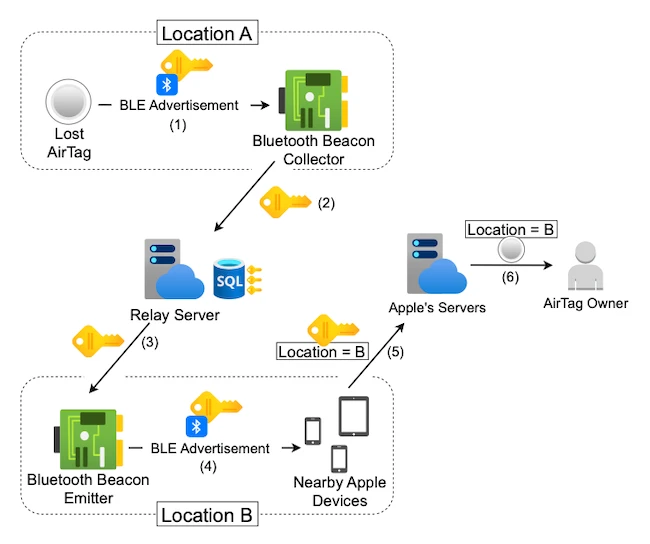
Researchers demonstrated a relay attack that takes advantage of this limitation. They captured Bluetooth signals from a test AirTag using Android devices, Linux systems, and small embedded hardware. After recording the signals, they removed the battery from the original AirTag and replayed the captured data from a different location using custom transmitters.
Apple devices near the replayed signal treated it as if it came from the original AirTag. These devices generated location reports based on the new location, and the Find My app displayed that position. The same approach worked across long distances by sending the captured data over the internet and replaying it in another country.
Handling conflicting signals in Find My
When both the original AirTag and the replayed signal are active, the app can switch between two locations. The position shown may jump from the true location to the injected one, depending on which reports are processed.
The system handles reports in two ways. Cloud reports are accepted only if they use the current encryption key, which changes about every 24 hours. Older keys stop working after rotation. Local Bluetooth signals take priority when the owner’s device is nearby, which can override cloud data and influence what is shown.
Captured signals remain usable for a limited time. If key rotation is paused, for example by removing the AirTag’s battery, replayed signals can continue to produce location reports for up to seven days before the system marks them as outdated.
To support their testing, the researchers built a relay server that stored captured signals, tracked when they were first seen, and controlled when they were replayed. This setup allowed repeated tests of how long spoofed locations could persist.
“Our results demonstrate that the design of Apple’s Find My protocol is vulnerable to practical relay attacks. Beyond highlighting this attack vector to the security community, future work will examine whether relaying could be repurposed as an active countermeasure against stalking by obfuscating or disrupting unwanted tracking,” researchers wrote.
