
The underground market for stolen credit card data has long operated as a volatile and highly deceptive ecosystem, where even experienced actors routinely fall victim to scams, exit schemes, and compromised services.
In recent years, this environment has become even more unstable, driven by increased law enforcement pressure, internal distrust among criminals, and the rapid turnover of marketplaces. As a result, threat actors are increasingly forced to adopt more structured approaches to identifying reliable suppliers and minimizing risk within their own illicit operations.
A guide found on an underground forum by Flare analysts sheds light on how threat actors themselves navigate the volatile world of credit card (CC) marketplaces.
The document, titled “The Underground Guide to Legit CC Shops: Cutting Through the Bullshit”—provides a structured look at how actors attempt to reduce risk in an ecosystem plagued by scams, law enforcement infiltration, and short‑lived operations.
Analysis of the guide reveals more than just practical advice. It outlines a methodology for vetting carding shops, operational security practices, and sourcing strategies, effectively documenting how today’s fraud actors think about trust, reliability, and survivability.
While parts of the guide appear to promote specific services, suggesting a possible vested interest from its author, it still offers a valuable glimpse into the inner workings of the carding economy, and the evolving standards actors use to operate within it.
From Opportunistic Fraud to Supplier Vetting Discipline
One of the most striking aspects of the guide is how it reframes carding from opportunistic fraud into a process‑driven discipline. Rather than focusing on how to use stolen cards, the document emphasizes how to evaluate suppliers.
This shift reflects a broader evolution within underground markets, where the primary risk is no longer just operational failure, but being defrauded by other criminals or interacting with compromised infrastructure.
The author repeatedly stresses that legitimacy is not defined by branding or visibility, but by survivability. In other words, a “real” shop is one that continues operating over time despite law enforcement operations, scams, and internal instability.
This aligns with observed trends in underground economies, where the lifespan of marketplaces has become increasingly unpredictable, forcing actors to adopt continuous verification practices.
The guide makes it clear that what separates a “legitimate” shop from the rest isn’t branding or uptime, it’s the quality of the stolen data it delivers. References to “fresh bins” (BIN = Bank Identifiable Number) and low decline rates point directly to the sources behind the data, whether from infostealer infections, phishing campaigns, or point-of-sale breaches. In this ecosystem, reputation isn’t built on promises but on consistently providing cards that actually work.
Shops that fail to maintain reliable data sources are quickly exposed, while those with steady access to fresh compromises rise to the top.
Carding actors are adopting disciplined workflows to source and test stolen financial data.
Flare continuously monitors underground forums and marketplaces, giving your team early visibility into exposed credentials, compromised cards, and emerging fraud infrastructure.
Building Trust in a Trustless Market
Transparency is another recurring theme. The guide highlights the importance of clear pricing models, real‑time inventory, and functional support systems, including ticketing and escrow services. These characteristics closely mirror legitimate e‑commerce platforms, underscoring how leading carding shops have adopted business practices designed to build user confidence and reduce friction.
Equally important is the role of community validation. The guide dismisses on‑site testimonials as unreliable, instead directing users toward discussions in closed or invite‑only forums. This reflects a broader fragmentation of the underground landscape, where trust is increasingly tied to controlled environments and long‑standing reputations.
Actors are encouraged to look for sustained discussion threads and historical presence, rather than isolated positive feedback.
The document also reveals a strong awareness of adversarial pressures. The emphasis on security‑first infrastructure, such as mirror domains, DDoS protection, and the absence of tracking mechanisms, suggests that operators are actively defending against both law enforcement monitoring and competing criminal groups.
In effect, these marketplaces function not only as distribution platforms, but as hardened environments designed to ensure operational continuity.
The Technical Checklist
Beyond high‑level principles, the guide introduces a step‑by‑step vetting protocol that provides insight into how threat actors conduct due diligence. Technical checks such as domain age, WHOIS privacy, and SSL configuration are presented as baseline requirements.
While these checks are relatively simple, they demonstrate an effort to apply structured analysis to what has historically been a trust‑based decision process.
The guide also highlights the importance of identifying mirror infrastructure and backup access points, noting that established operations rarely rely on a single domain. This reflects a practical understanding of the instability of underground services, where takedowns and disruptions are common. The presence of multiple access points is framed as an indicator of operational maturity and resilience.
Social intelligence gathering plays an equally significant role. Rather than relying on direct interactions with vendors, users are encouraged to analyze forum discussions, track vendor histories, and identify patterns of behavior over time.
Particular attention is given to detecting coordinated endorsement campaigns, such as multiple positive reviews originating from newly created accounts, a tactic frequently associated with scams.
Operational Security
Another critical component of the guide is its focus on operational security. The recommendations provided, while framed in the context of carding, closely mirror practices observed across a wide range of cybercriminal activities. Users are advised to avoid direct connections, utilize proxy services aligned with target geographies, and compartmentalize their environments through dedicated systems or virtual machines.
The discussion of cryptocurrency usage is particularly notable. The guide strongly discourages direct transactions from regulated platforms, instead advocating for intermediary wallets and privacy‑focused assets such as Monero. This reflects a growing awareness among threat actors of blockchain analysis capabilities and the risks associated with traceable financial flows.
Taken together, these OPSEC recommendations highlight an important shift: actors are no longer relying solely on tools to evade detection, but are adopting layered strategies designed to reduce exposure across the entire operational chain. This level of discipline suggests that even mid‑tier actors are increasingly adopting practices once associated with more advanced threat groups.
Scale vs. Exclusivity
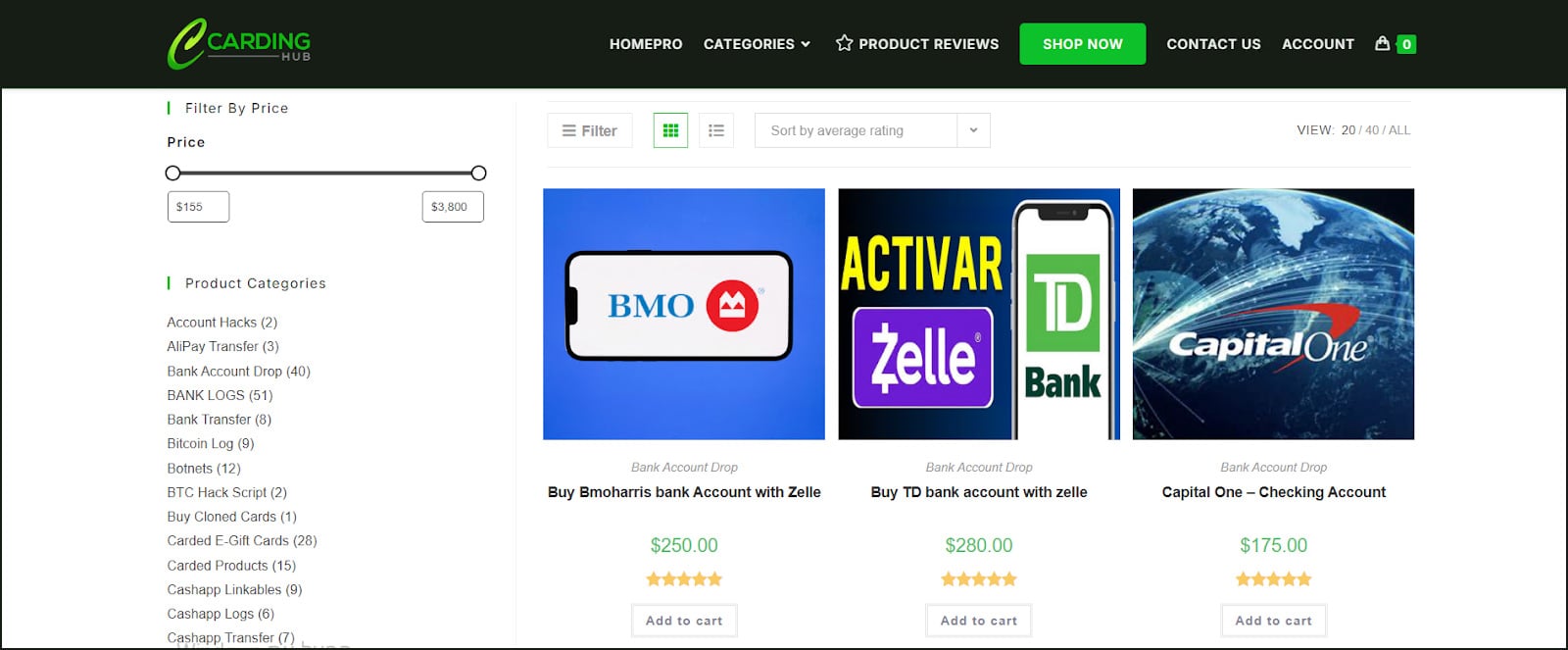
The guide further categorizes carding shops into distinct operational models, including large automated platforms and smaller, curated vendor groups. This segmentation reflects the diversification of the underground economy, where different actors prioritize scale, accessibility, or quality depending on their objectives.
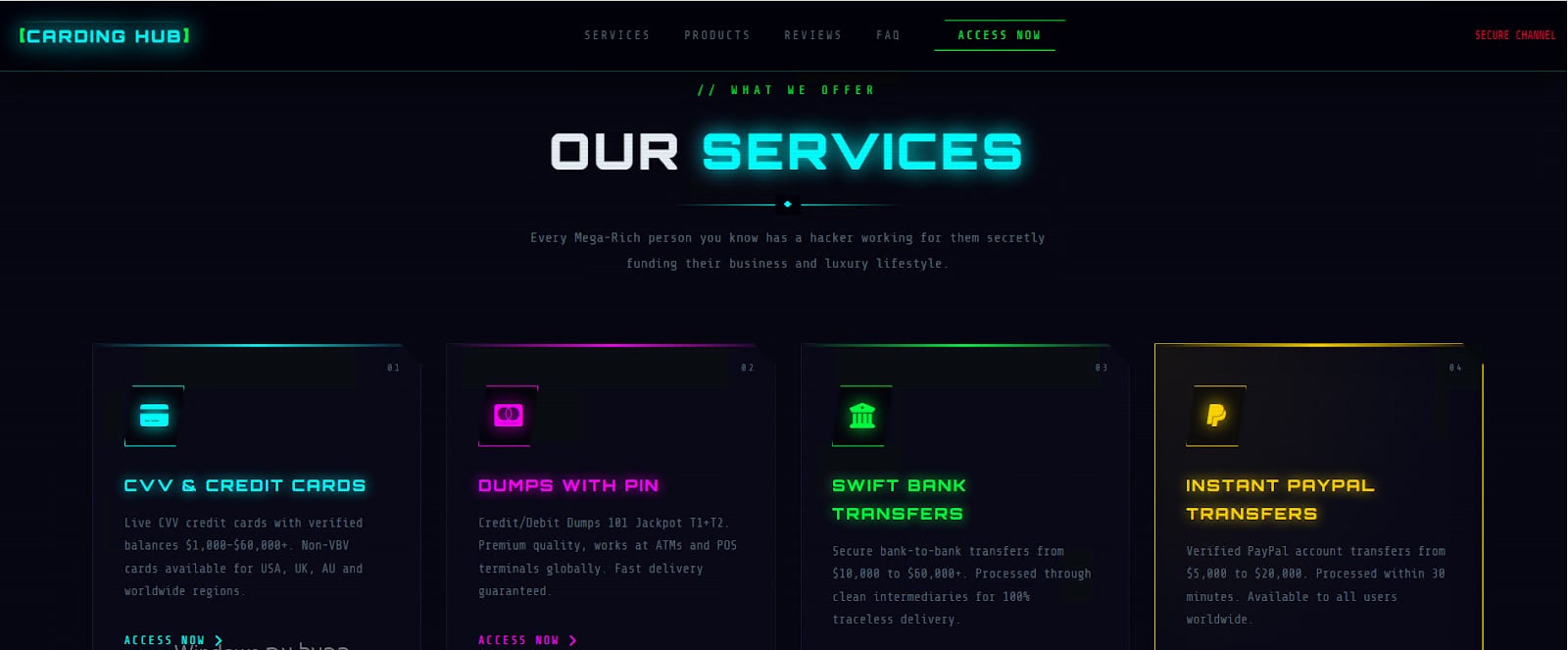
Automated platforms are described as highly efficient environments, often featuring integrated tools and instant purchasing capabilities. These operations resemble legitimate online marketplaces in both structure and functionality, enabling users to quickly acquire and test data at scale.
In contrast, boutique vendor groups emphasize exclusivity, higher quality, and controlled access, often relying on invitation‑based systems and long‑term relationships.
Commercial Interests and Operational Reality
Despite its structured approach, the guide is not without bias. The inclusion of a direct endorsement for a specific platform suggests that the author may have a vested interest in promoting certain services. This is a common pattern in underground communities, where informational content is often used as a vehicle for subtle advertising or affiliate activity.
Such endorsements should be viewed with caution. However, they do not necessarily invalidate the broader insights provided by the guide. Instead, they highlight the complex interplay between information sharing and commercial interests within cybercriminal ecosystems.
From a defensive perspective, the guide offers valuable intelligence into how threat actors assess risk and make operational decisions. The emphasis on verification, community validation, and layered security reflects a level of maturity that complicates traditional disruption efforts. Rather than relying on single points of failure, actors are increasingly building redundancy and adaptability into their workflows.
Ultimately, the document serves as both a playbook and a signal. It demonstrates that the carding ecosystem became more structured, more cautious, and more resilient. For defenders, understanding these dynamics is critical to anticipating how these markets will continue to evolve, and where opportunities for disruption may still exist.
How Flare Can Help
Flare helps organizations stay ahead of fraud by continuously monitoring underground forums and marketplaces, revealing how threat actors source, vet, and use stolen credit card data. This provides early insight into attacker behavior, including how they optimize success rates, build trust, and adapt to defenses.
By turning this intelligence into actionable insights, Flare enables security teams to detect exposures, anticipate fraud campaigns, and disrupt attacker workflows-shifting from reactive response to proactive, intelligence-driven defense.
Learn more by signing up for our free trial.
Sponsored and written by Flare.

