For a long time, I assumed my online accounts were secure enough. I was not using weak passwords, and I had a system that felt reasonably safe. It was not perfect, but it did not feel like something I needed to worry about.
That changed when I started paying attention to how most account breaches actually happen. It is rarely about someone “hacking” their way in. More often, it’s leaked passwords or reused logins that slip through.
The fix turned out to be simple: I enabled two-factor authentication (2FA). That one extra step made my accounts much harder to break into.

7 things you should immediately double-check in your Google security settings
Secure your Google account right now
The moment I realized passwords are not enough
The turning point for me was not getting hacked, but it was close enough to make me rethink everything.
I got a security alert about a suspicious login attempt on my old Facebook account. Nothing happened in the end, but it was enough to make me pause.
Out of curiosity, I looked into it a bit more. Most attacks do not involve someone manually trying to break into your account. They rely on reused credentials or leaked passwords, and use automated systems to try those combinations across multiple sites.
Even if my password is strong, the account can be compromised if it was exposed elsewhere. A more significant realization is that after someone has your password, nothing prevents malicious actors from accessing your account.
The simple step that changed everything
Two-factor authentication or 2FA is the additional step where, after entering your password, you must confirm your identity using a code. That code usually comes from your phone as a text message or through an authenticator app.
At first, it feels like an inconvenience. However, that extra step completely changes your account’s security.
With 2FA enabled, logging in requires your password and your phone or authenticator app. So even if your password is leaked, reused, or guessed, it is no longer enough on its own.
It does not make your account impossible to break into, but it blocks the most common and easiest attack paths almost immediately.
Instead of being an easy target, your account becomes much harder to access without that second factor.
Setting it up was easier than I expected
Setting up two-factor authentication only took a few minutes.
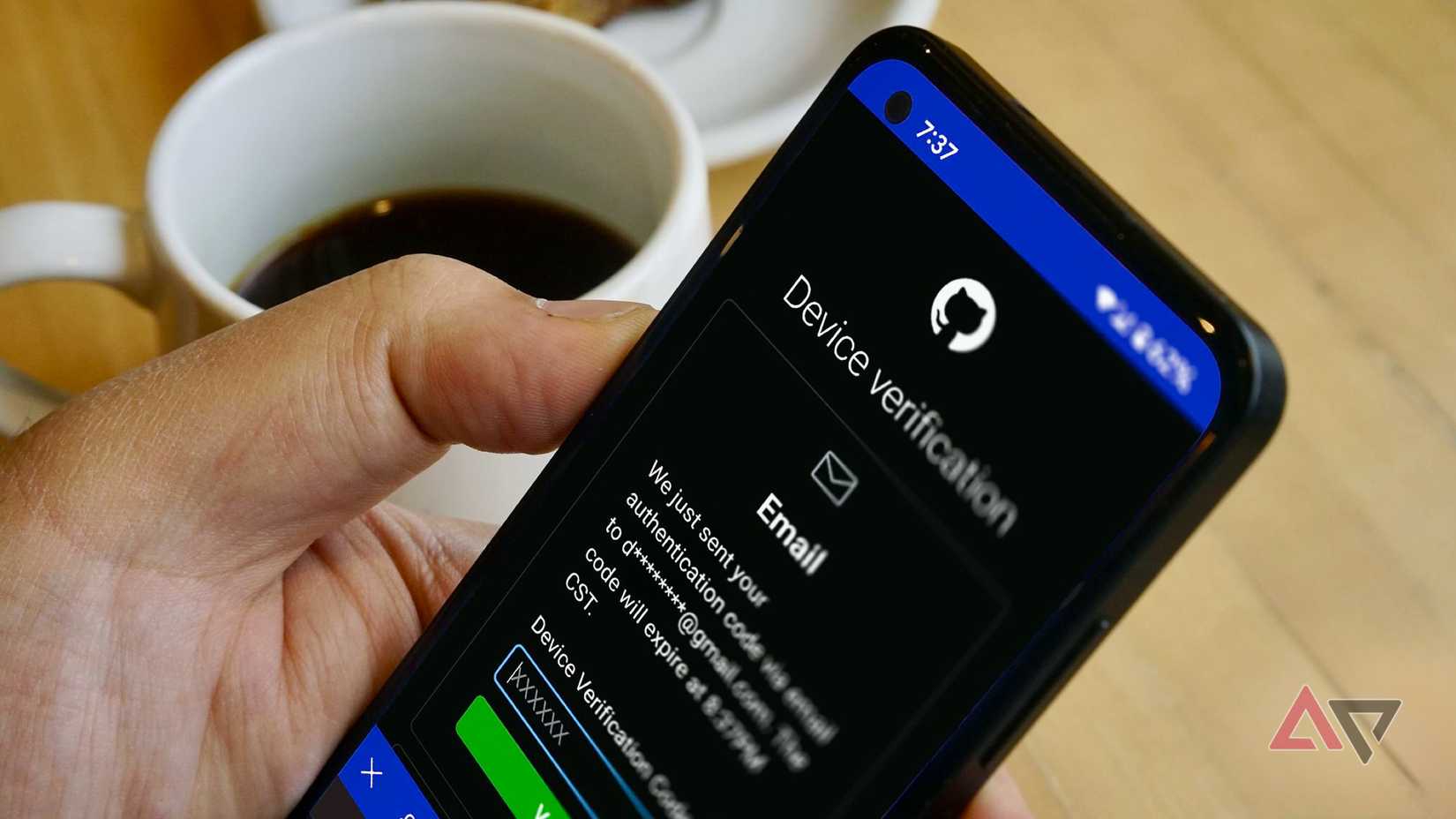
On most accounts, I went into the security settings, found the two-factor authentication option, and followed the prompts.
You choose how you want to receive your codes, either via SMS or through an authenticator app, and then confirm it with a quick verification.
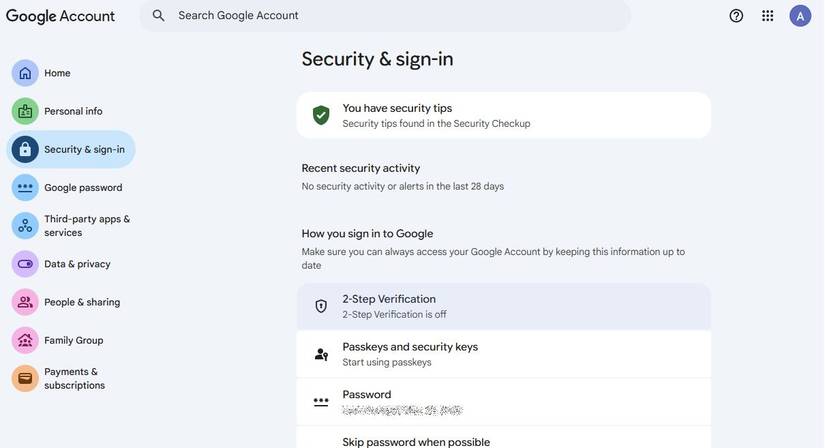
I started with my main Google account, since it is tied to everything from email to cloud storage. From there, I turned it on for a few other important services.
To enable it, go to your Google Account settings, click the Security & sign-in tab, and select the 2-Step Verification option.
From there, Google walks you through the process step by step. You start by confirming your password, then choose how you want to verify your logins.
Google also encourages you to set up backup options, like backup codes or a secondary method, in case you lose access to your phone. It is worth doing this right away so you are not locked out later.
Authenticator apps vs. SMS codes
At first, I used SMS-based codes because they are the easiest to set up. You log in, get a text message with a code, and enter it.
But after reading more about it, I switched to an authenticator app for better security. SIM swapping or delays in receiving messages can make SMS codes less reliable, especially if you depend on them regularly.
Apps like Google Authenticator, Authy, 2FAS, or Microsoft Authenticator generate time-based codes directly on your device, which means they do not rely on your mobile network or phone number.
That said, not every service gives you a choice. Many banks and credit unions still rely on SMS-based verification instead of supporting authenticator apps.
In those cases, you do not have much control over the method, but using SMS is still far better than having no second layer at all.

10 Android security settings you should change right now
Keep your phone safe by tweaking a few security settings
The small step that is worth it
For a long time, I thought having a strong password was enough. That changed after I understood how most account breaches actually happen, and how little a password alone can do if it is exposed.
Enabling two-factor authentication proved to be one of the simplest and most effective ways to protect myself online. It did not take long to set up, but it added a layer of security that makes a significant difference.