Code keeps moving through pipelines, and credentials continue to surface alongside it. GitGuardian’s State of Secrets Sprawl 2026 puts the count at 28.65 million new hardcoded secrets in public GitHub commits in 2025, extending a multi-year rise in exposed access keys, tokens, and passwords.
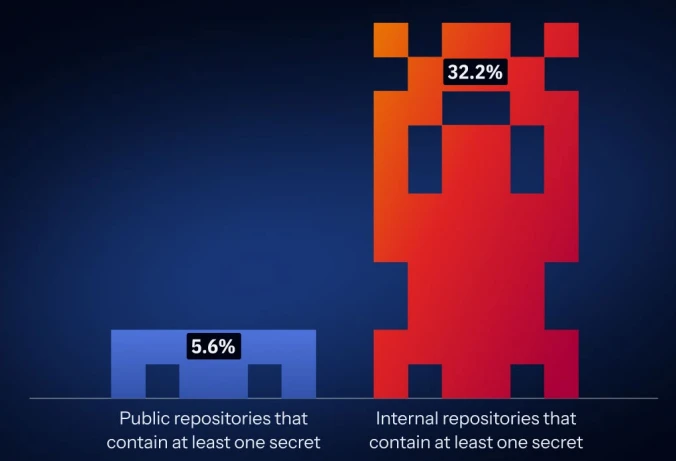
Public and internal repositories that contain at least one secret (Source: GitGuardian)
Exposure is spreading beyond code
The problem no longer exists only in public repositories, since internal environments carry a larger share of leaked credentials, often tied directly to production systems and operational access. Internal repositories show a much higher likelihood of containing hardcoded secrets, which places sensitive access closer to core infrastructure.
A significant share of incidents also comes from tools outside source control, where collaboration platforms such as Slack, Jira, and Confluence become part of everyday workflows. These environments often include credentials shared during troubleshooting or routine coordination, and those entries can grant immediate access to systems.
Self-hosted infrastructure adds another dimension, with GitLab instances and Docker registries exposed on the internet containing large volumes of credentials that can remain usable after discovery. These systems tend to operate outside standard scanning processes, which allows sensitive data to build up over time.
AI development is adding more credentials to track
The growth of AI tooling has introduced new sources of credentials across development workflows, where projects now connect to model providers, orchestration layers, retrieval systems, and agent frameworks, each requiring its own authentication and adding to the overall volume of secrets in circulation.
Many of the fastest-growing categories of leaked secrets tie directly to these AI services. These credentials appear across code, configuration files, and supporting infrastructure. AI-assisted coding contributes to the pattern, with generated or co-authored changes showing a higher rate of exposed secrets than the broader baseline.
“AI makes it easier and faster to build, integrate, and ship. But every new tool, API, workflow, agent, and service account also creates new credentials to manage and more surface area for attackers to target. When organizations scale creation faster than governance, secrets begin to spread everywhere,” the company wrote in a blog.
This shows a shift in development environments, where teams connect more services and rely on automation to build and deploy software. Each connection adds another credential that must be stored, shared, and maintained, increasing the number of places where exposure can occur.
Leaked credentials are staying valid for years
One of the more persistent issues is how long exposed credentials remain active, with secrets leaked several years ago continuing to work and extending risk far beyond the initial exposure.
Replacing a credential often involves changes across multiple systems, including codebases, deployment pipelines, and shared configurations. Those dependencies slow down remediation and allow exposed access to remain in place.
The report also identifies gaps in how teams prioritize fixes. Prioritization methods that rely only on validation status leave part of the risk unaddressed. Some sensitive credentials do not match known patterns or cannot be automatically verified, and still provide meaningful access.
A wider operational problem
This shows how credentials now move through software systems. They appear across repositories, internal platforms, collaboration tools, and infrastructure services. This distribution makes it harder to track ownership, usage, and exposure.
AI-related services add another layer, with credentials showing up in configuration files tied to emerging standards such as MCP. These files often remain close to application logic and can be committed alongside code.
The result is a larger and more fragmented environment where exposure spans multiple systems with different controls and timelines. Credentials created in one part of the workflow can surface in another, and they can remain active long after they are first exposed.
Secrets sprawl reflects the way software is built and maintained across teams and tools. The number of exposed credentials continues to rise, and many remain usable for extended periods. Internal systems, collaboration platforms, and AI-driven workflows each contribute to that pattern, expanding both the reach and duration of risk tied to leaked access.

