Vorlon has unveiled AI Agent Flight Recorder and AI Agent Action Center, adding forensics and coordinated response to secure enterprise agentic ecosystems and close a key security gap.
The agentic ecosystem contains SaaS applications, AI agents, API integrations, non-human identities, and the sensitive data flows connecting them. It’s become the fastest-growing attack surface in the enterprise, moves at machine speed, and most organizations lack adequate supervision.
The Agentic Ecosystem Security Gap: 2026 CISO Report, a Vorlon survey of 500 U.S. security leaders, documents the scale of the problem: 99.4% of organizations experienced at least one SaaS or AI ecosystem security incident in 2025.
Security teams have built real capability in detection. What often remains out of reach is understanding exactly what happened and mobilizing the right people to act on it. Only 38.2% claim comprehensive incident response coverage for their SaaS and AI ecosystem. 86.8% of security teams cannot see what data AI tools are exchanging with SaaS applications. Between 83% and 87% of CISOs report limitations across every capability required to address the threat. This is a structural gap, not a vendor quality issue.
AI Agent Flight Recorder: A forensic record across the entire ecosystem
When an AI agent behaves unexpectedly, whether through compromise, misconfiguration, or an unanticipated chain of autonomous actions, security teams need a complete record of what happened. Today that record rarely exists. Agent activity spans SaaS applications, cloud environments, and API integrations, and reconstructing a full picture from fragmented, platform-specific logs is often impossible.
The AI Agent Flight Recorder closes that gap. Built on Vorlon’s patented DataMatrix intelligent simulation technology, it captures a continuous, cross-app audit trail of every agent action. That means every identity, every SaaS application, every API endpoint, every data classification, every downstream system touched. The record is immutable, queryable, and available in minutes.
Here is what that looks like in practice. A customer support agent begins querying financial records outside its normal scope, at unusual hours, at volumes far beyond its baseline. The Flight Recorder captures every step. For example, which identity triggered the action, which SaaS systems were touched, which customer records containing PII and payment data were accessed, and which downstream integrations were involved. What would have taken days to reconstruct is available in minutes, with blast radius calculated in real time so security teams can answer board-level questions before the next morning.
When a plane crashes, investigators have a flight recorder. When an AI agent is compromised, most security teams have nothing. Vorlon changes that.
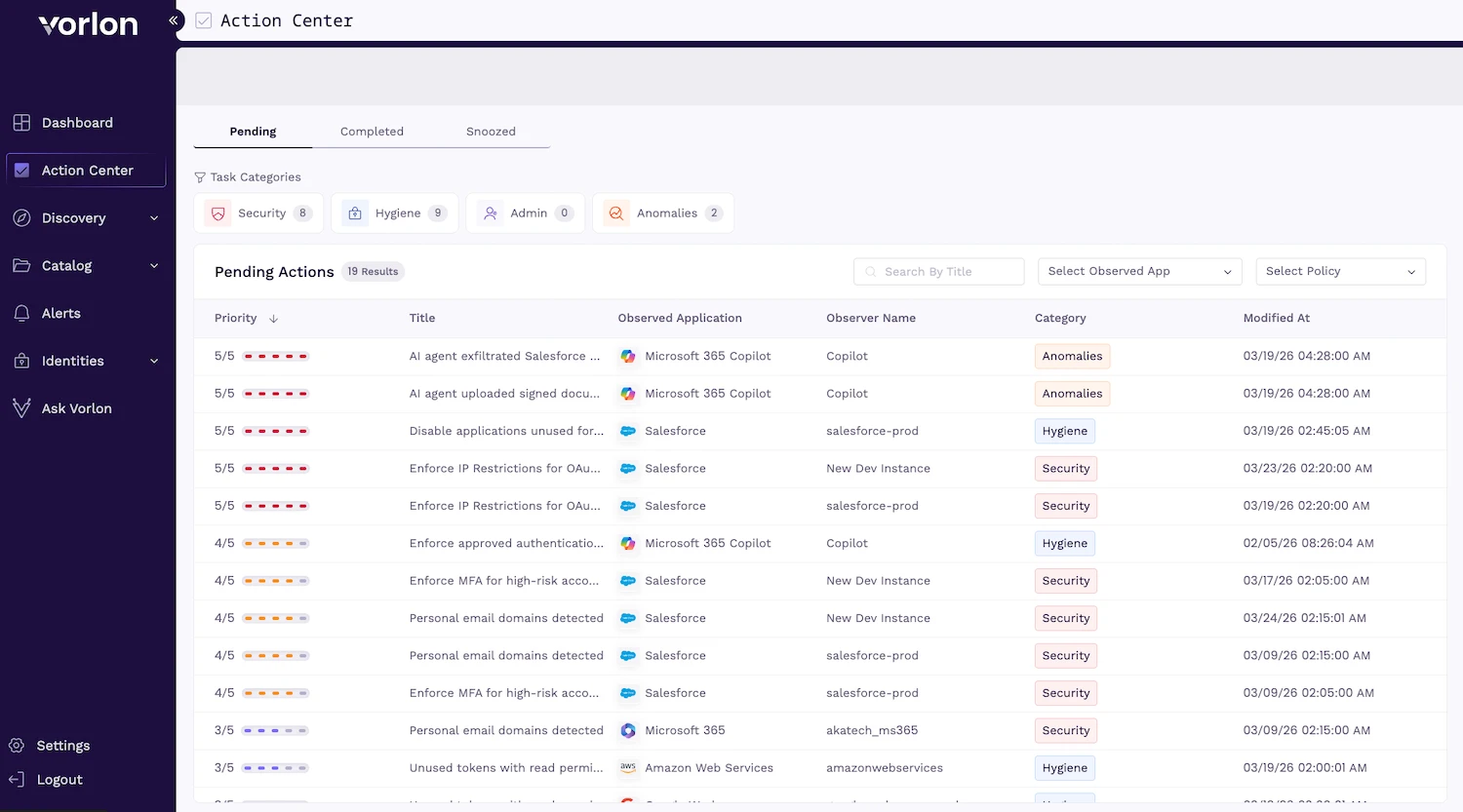
AI Agent Action Center: From finding to fix, across the teams that matter
Detection has a second act. Once a finding surfaces, either from the Flight Recorder, Vorlon’s detection engine, or an integrated security tool, then the real work begins. This includes determining the right response, routing the action to the right person or system, and confirming the loop was closed.
The AI Agent Action Center is where that work happens. It surfaces prioritized findings and routes to the appropriate team member or system. In some cases, that means step-by-by remediation guidance to a busy app owner or the person best positioned to act. Rather than generating alerts that land in a single queue, Action Center coordinates response across SecOps, application owners, IT administrators, and compliance teams, connecting to existing workflows through native integrations with SIEM, SOAR, ITSM, identity providers, and threat intelligence feeds, and tracking every ticket through to resolution.
Responding to agentic AI risk is not a single-team problem. As Gartner notes, “Enabling effective incident response is often the last step when implementing an agentic AI cybersecurity program, which puts it at risk of negligence from key stakeholders, or delayed implementation. In a technology landscape combining high-speed development cycles and low maturity of controls, this can lead to serious security gaps, including the inability to track the root cause of breaches.”
The action center finds security gaps in your agentic ecosystem, prioritizes them for you, and provides fast paths to remediation.
Security gaps typically fall into one of three categories:
- Universal – these are things that should never happen, regardless of your environment. For example, an AI agent provisioned with full admin-level permissions to sensitive customer records, far beyond what its function requires.
- Behavioral – these are anomalous behaviors linked to your agent usage and traffic. For example, when a new MCP server connects an existing agent to an application holding sensitive data.
- Dynamic – these are custom rules security teams write and enforce to close the gaps AI vendors leave open. For example, not all versions of OpenAI and Claude support IP-based access restrictions. Vorlon lets you enforce boundaries without waiting on vendor release cycles.
Each stakeholder, from CISO to application owner to compliance officer, sees the findings, and workflows most relevant to their role.
“Security architecture built to monitor the front door has no native framework for tracking what an AI agent does after access is granted. That’s the engine room. The runtime layer where agents move sensitive data between systems, where OAuth tokens grant persistent cross-platform access, where a single compromised integration cascades across the supply chain. DataMatrix maps every agent action to the data it touched and the identity behind it, across the entire agentic ecosystem, not app by app but end to end,” said Amir Khayat, CEO of Vorlon.
“The Flight Recorder and Action Center give security teams what they have always had for every other incident: a complete record of what happened, where it went, what is at risk, and a clear path to resolution,” Khayat concluded.