
An information stealer called VoidStealer uses a new approach to bypass Chrome’s Application-Bound Encryption (ABE) and extract the master key for decrypting sensitive data stored in the browser.
The novel method is stealthier and relies on hardware breakpoints to extract the v20_master_key, used for both encryption and decryption, directly from the browser’s memory, without requiring privilege escalation or code injection.
A report from Gen Digital, the parent company behind the Norton, Avast, AVG, and Avira brands, notes that this is the first case of an infostealer observed in the wild to use such a mechanism.
Google introduced ABE in Chrome 127, released in June 2024, as a new protection mechanism for cookies and other sensitive browser data. It ensures that the master key remains encrypted on disk and cannot be recovered through normal user-level access.
Decrypting the key requires the Google Chrome Elevation Service, which runs as SYSTEM, to validate the requesting process.
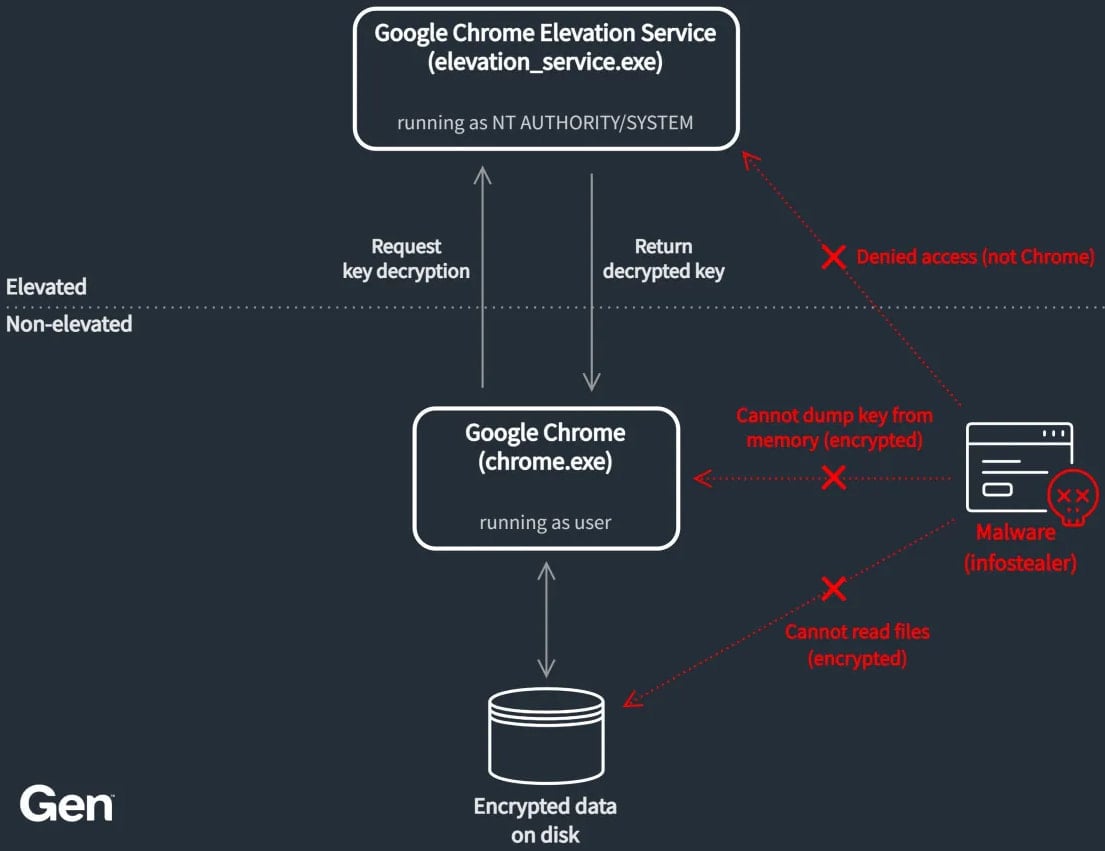
Source: Gen Digital
However, this system has been bypassed by multiple infostealer malware families and has even been demonstrated in open-source tools. Although Google implemented fixes and improvements to block these bypasses, new malware versions reportedly continued to succeed using other methods.
“VoidStealer is the first infostealer observed in the wild adopting a novel debugger-based Application-Bound Encryption (ABE) bypass technique that leverages hardware breakpoints to extract the v20_master_key directly from browser memory,” says Vojtěch Krejsa, threat researcher at Gen Digital.
VoidStealer is a malware-as-a-service (MaaS) platform advertised on dark web forums since at least mid-December 2025. The malware introduced the new ABE bypass mechanism in version 2.0.
.webp)
Source: Gen Digital
Stealing the master key
VoidStealer’s trick to extract the master key is to target a short moment when Chrome’s v20_master_key is briefly present in memory in plaintext state during decryption operations.
Specifically, VoidStealer starts a suspended and hidden browser process, attaches it as a debugger, and waits for the target browser DLL (chrome.dll or msedge.dll) to load.
When loaded, it scans the DLL for a specific string and the LEA instruction that references it, using that instruction’s address as the hardware breakpoint target.
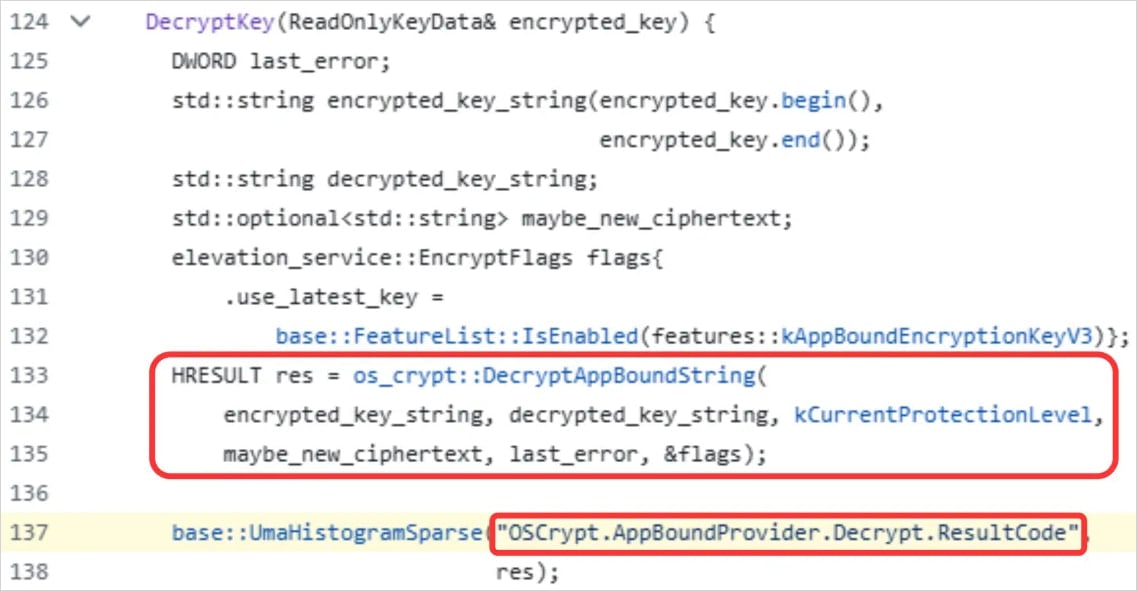
Source: Gen Digital
Next, it sets that breakpoint across existing and newly created browser threads, waits for it to trigger during startup while the browser is decrypting protected data, then reads the register holding a pointer to the plaintext v20_master_key and extracts it with ‘ReadProcessMemory.’
Gen Digital explains that the ideal time for the malware to do this is during browser startup, when the application loads ABE-protected cookies early, forcing the decryption of the master key.
The researchers explained that VoidStealer likely did not invent this technique but rather adopted it from the open-source project ‘ElevationKatz,’ part of the ChromeKatz cookie-dumping toolset that demonstrates weaknesses in Chrome.
Although there are some differences in the code, the implementation appears to be based on ElevationKatz, which has been available for more than a year.
BleepingComputer has contacted Google with a request for a comment on this bypass method being used by threat actors, but a reply was not available by publishing time.


