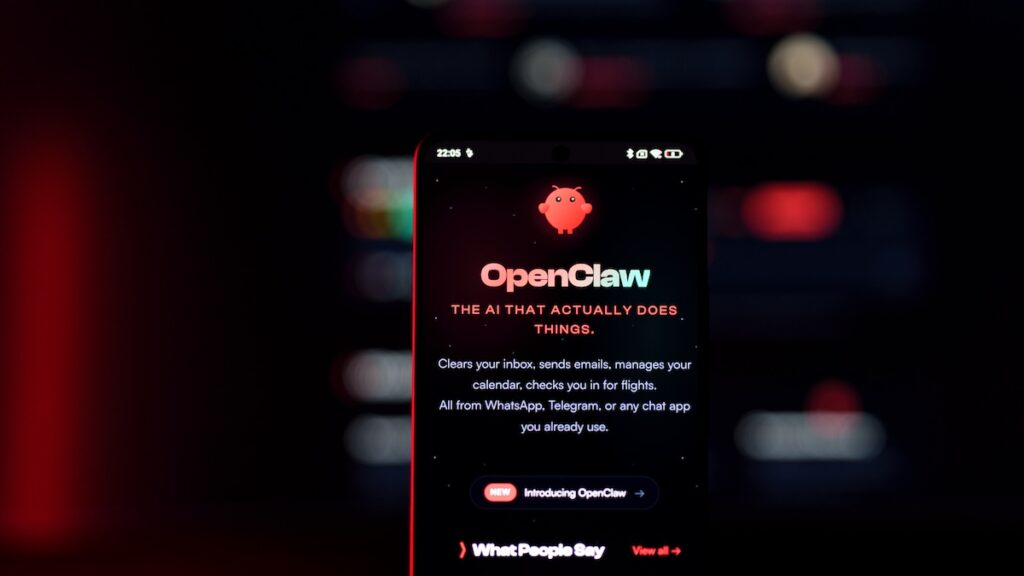
A vulnerability in the OpenClaw AI assistant could have allowed attackers to hijack agents by luring victims to malicious websites, Oasis Security reports.
Successful exploitation of the bug did not require the installation of malicious extensions or user interaction, instead relying on functionality within OpenClaw.
A self-hosted AI agent, OpenClaw runs a local WebSocket server, which acts as a gateway that handles authentication, orchestrates the agent, manages chat sessions, and stores configurations.
Applications and devices connect to the gateway as nodes to expose functionality, run commands, and access capabilities, while authentication is handled via tokens or passwords.
“The gateway binds to localhost by default, based on the assumption that local access is inherently trusted. That assumption is where things break down,” Oasis explains.
The cybersecurity firm discovered that AI agents with the gateway bound to localhost and protected by passwords could be hijacked if developers visited malicious websites.
Because WebSocket connections to localhost were not blocked by the browser’s cross-origin policies, Oasis explains, JavaScript code on a malicious website could open such a connection using the agent’s port.
It could then brute-force the password, because localhost connections were not covered by the gateway’s rate limiter, and then register as a trusted device, as device pairings from localhost were automatically approved with no user prompt.
“The gateway’s rate limiter completely exempts loopback connections—failed attempts are not counted, not throttled, and not logged. In our lab testing, we achieved a sustained rate of hundreds of password guesses per second from browser JavaScript alone. At that speed, a list of common passwords is exhausted in under a second, and a large dictionary would take only minutes,” Oasis notes.
With a guessed password, the attacker gains an authenticated session with administrator privileges, gaining full control of OpenClaw. This enables the attacker to interact with the agent, extract configurations, enumerate nodes, and read logs.
“In practice, this means an attacker could instruct the agent to search the developer’s Slack history for API keys, read private messages, exfiltrate files from connected devices, or execute arbitrary shell commands on any paired node. For a developer with typical OpenClaw integrations, this is equivalent to full workstation compromise, initiated from a browser tab,” Oasis says.
The OpenClaw security team addressed the vulnerability within 24 hours of receiving Oasis’s report and classified it as a high-severity issue. Users are advised to update to OpenClaw version 2026.2.25 or later.
Related: Claude Code Flaws Exposed Developer Devices to Silent Hacking
Related: OpenClaw Security Issues Continue as SecureClaw Open Source Tool Debuts
Related: Hackers Weaponize Claude Code in Mexican Government Cyberattack
Related: The Blast Radius Problem: Stolen Credentials Are Weaponizing Agentic AI