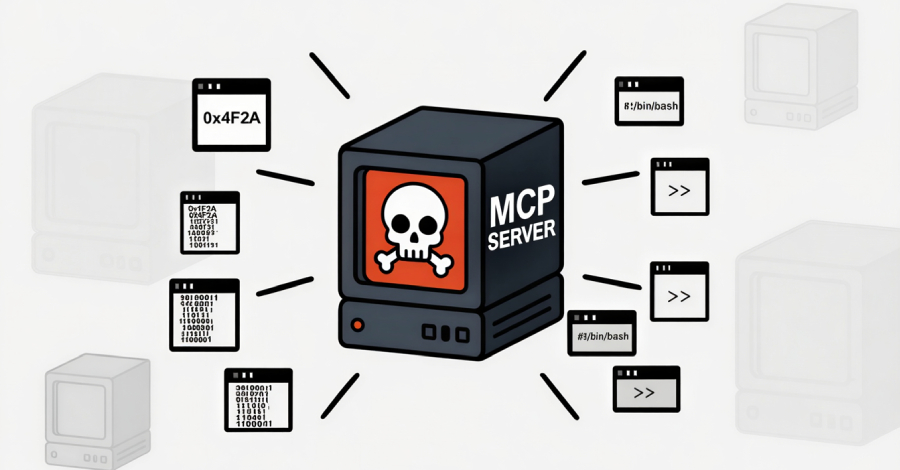
Cybersecurity researchers have disclosed details of a new SmartLoader campaign that involves distributing a trojanized version of a Model Context Protocol (MCP) server associated with Oura Health to deliver an information stealer known as StealC.
“The threat actors cloned a legitimate Oura MCP Server – a tool that connects AI assistants to Oura Ring health data – and built a deceptive infrastructure of fake forks and contributors to manufacture credibility,” Straiker’s AI Research (STAR) Labs team said in a report shared with The Hacker News.
The end game is to leverage the trojanized version of the Oura MCP server to deliver the StealC infostealer, allowing the threat actors to steal credentials, browser passwords, and data from cryptocurrency wallets.
SmartLoader, first highlighted by OALABS Research in early 2024, is a malware loader that’s known to be distributed via fake GitHub repositories containing artificial intelligence (AI)-generated lures to give the impression that they are legitimate.
In an analysis published in March 2025, Trend Micro revealed that these repositories are disguised as game cheats, cracked software, and cryptocurrency utilities, typically coaxing victims with promises of free or unauthorized functionality to make them download ZIP archives that deploy SmartLoader.
The latest findings from Straiker highlight a new AI twist, with threat actors creating a network of bogus GitHub accounts and repositories to serve trojanized MCP servers and submitting them to legitimate MCP registries like MCP Market. The MCP server is still listed on the MCP directory.
By poisoning MCP registries and weaponizing platforms like GitHub, the idea is to leverage the trust and reputation associated with services to lure unsuspecting users into downloading malware.
“Unlike opportunistic malware campaigns that prioritize speed and volume, SmartLoader invested months building credibility before deploying their payload,” the company said. “This patient, methodical approach demonstrates the threat actor’s understanding that developer trust requires time to manufacture, and their willingness to invest that time for access to high-value targets.”
The attack essentially unfolded over four stages –
- Created at least 5 fake GitHub accounts (YuzeHao2023, punkpeye, dvlan26, halamji, and yzhao112) to build a collection of seemingly legitimate repository forks of Oura MCP server.
- Created another Oura MCP server repository with the malicious payload under a new account “SiddhiBagul”
- Added the newly created fake accounts as “contributors” to lend a veneer of credibility, while deliberately excluding the original author from contributor lists
- Submitted the trojanized server to the MCP Market
This also means that users who end up searching for the Oura MCP server on the registry would end up finding the rogue server listed among other benign alternatives. Once launched via a ZIP archive, it results in the execution of an obfuscated Lua script that’s responsible for dropping SmartLoader, which then proceeds to deploy StealC.
The evolution of the SmartLoader campaign indicates a shift from attacking users looking for pirated software to developers, whose systems have become high-value targets, given that they tend to contain sensitive data such as API keys, cloud credentials, cryptocurrency wallets, and access to production systems. The stolen data could then be abused to fuel follow-on intrusions.
As mitigations to combat the threat, organizations are recommended to inventory installed MCP servers, establish a formal security review before installation, verify the origin of MCP servers, and monitor for suspicious egress traffic and persistence mechanisms.
“This campaign exposes fundamental weaknesses in how organizations evaluate AI tooling,” Straiker said. “SmartLoader’s success depends on security teams and developers applying outdated trust heuristics to a new attack surface.”