
A technical look at the first 24 hours: how quickly attackers enumerate and target newly exposed assets
Written by Topher Lyons – Sprocket Security
The moment a new asset gets a public IP address, a clock starts. Not a slow one. A relentless, automated one. The gap between “this just went live” and “this is being actively probed” is minutes, not days.
That’s not theoretical. With the help of our ASM Community Edition, it’s what Sprocket Security sees continuously across customer environments, and it’s exactly what attackers count on: your team won’t know something is exposed until it’s already too late.
The First 24 Hours: A Technical Timeline
T+0: The asset goes live.
A developer pushes a new cloud instance. A misconfigured firewall rule opens a port. A vendor portal spins up on a subdomain nobody flagged. Whatever the cause, a new internet-routable endpoint now exists, and security doesn’t get a notification.
T+5 to T+60 minutes: The scanners find it.
Automated scanning infrastructure sweeps the entire public internet, constantly. Shodan, Censys, ShadowServer, and others index new hosts on a rolling basis (Censys alone covers tens of thousands of ports).
Within an hour, your asset has its open ports catalogued, banner info grabbed (web server version, TLS cert, SSH fingerprint), and response signatures compared against known vulnerability databases.
T+1 to T+6 hours: Enumeration begins.
By now your asset shows up in Shodan and Censys queries. Automated attack tooling starts its own recon pass: looking for service versions, open management ports (RDP on 3389, SSH on 22, admin panels on 8080/8443), and TLS certs that pivot to related domains and subdomains.
If your new asset has a cert, attackers can learn a lot about your broader infrastructure without ever touching something you were watching.
T+6 to T+12 hours: Active probing.
Passive discovery flips to active targeting. GreyNoise data shows scanner activity spikes in this window. Credential stuffing kicks off against SSH and RDP. Web services start getting hit with directory brute-forcing. Databases like Elasticsearch and Redis get probed for unauthenticated access. Frameworks get tested against known CVEs.
None of this needs a human to kick it off. Botnets handle it at scale, around the clock.
T+12 to T+24 hours: Compromise.
Unit 42 researchers deployed 320 honeypots across cloud providers (RDP, SSH, SMB, Postgres) to see what would happen. 80% were compromised within 24 hours.
For anything running with exploitable vulnerabilities, misconfigs, or default credentials, that’s all it takes to go from “this just went live” to “this is already owned.”
Sprocket Security ASM Community Edition finds what attackers are looking for (hidden APIs, forgotten subdomains, misconfigured services) before they find it first.
Get continuous external attack surface visibility, free.
Real-World Example: The Hidden API Nobody Knew Existed
The timeline above assumes you know what’s exposed. Some of the most dangerous exposures are assets your own team has no idea are public, and the path to finding them is exactly what attackers use.
With a recent finding, ASM flagged a public-facing logistics web app and, as part of URL enumeration, pulled down and analyzed the compiled JavaScript bundle being served to browsers.
Buried in that JS file was a reference to a backend API. Not in any asset inventory. Not something anyone explicitly exposed. But live, public, and completely open.
Human testers ran the same request an attacker would:
curl -s 'https://logisticsapi.[redacted].com/Logistics/api/customernotes/2631' | jq
The server responded. No token, no credentials.
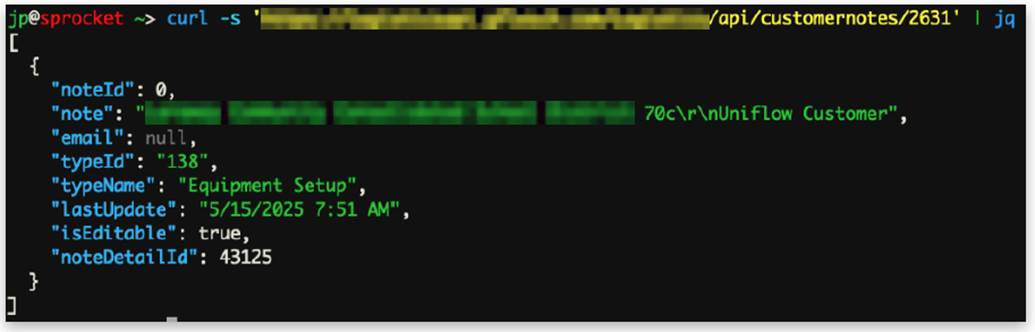
By iterating through endpoint IDs, testers pulled:
- Customer names, email addresses, and account notes
- Cleartext credentials for customer accounts
- Default device usernames and passwords
- Internal network information for deployed devices
- Employee names and email addresses
The full chain from public website to JS analysis to hidden API to unauthenticated data dump mirrors exactly what attacker tooling does during enumeration. The difference here was that Sprocket Security got there first.
The Compounding Problem: You Don’t Know What You Have
Unit 42’s attack surface research found that the average organization’s external attack surface changes by more than 300 new services every month. More than 20% of externally accessible cloud services turn over on a monthly basis.
Security teams aren’t keeping up. The root cause in most breach investigations comes back to a variation of the same statement: “We didn’t know that was on the internet.”
An asset you don’t know about is one you can’t patch, monitor, or pull offline when things go sideways. And as the example above shows, it’s often not something someone deliberately deployed.
It’s a backend service that got referenced in a JavaScript file nobody thought to look at.
From Discovered to Validated: The ASM-to-Pentesting Path
Finding the hidden API is step one. Figuring out what’s actually exploitable and what the real business impact is takes human eyes.
That’s the path Sprocket Security is built around. ASM Community Edition continuously enumerates your external attack surface: discovering assets, pulling JavaScript bundles, mapping subdomains, surfacing what’s actually visible from outside your network.
When something unexpected shows up (an API that shouldn’t be public, an admin panel nobody flagged, an unusual cert), that feeds directly into human-led testing.
That’s exactly how the example finding played out. ASM’s enumeration surfaced the JavaScript reference. Human testers validated the unauthenticated access, mapped the exposed endpoints, and documented real data exposure with clear remediation steps. Not a scanner alert. An actual finding.
Continuous ASM discovery feeding into targeted human testing is what closes the gap between “we think our attack surface is X” and “here’s what an attacker actually sees.”
Find Your Assets Before Attackers Do
The first-24-hours problem isn’t solved by faster patching. It’s solved by knowing what you have before attackers find it.
Sprocket ASM Community Edition gives you continuous, attacker-perspective visibility into your external attack surface, free.
See what’s exposed, discover what you didn’t know was public, and prioritize what actually matters.
The clock is already running.
Sponsored and written by Sprocket Security.

