
A new Android malware campaign is using the Hugging Face platform as a repository for thousands of variations of an APK payload that collects credentials for popular financial and payment services.
Hugging Face is a popular platform that hosts and distributes artificial intelligence (AI), natural language processing (NLP), and machine learning (ML) models, datasets, and applications.
It is considered a trusted platform unlikely to trigger security warnings, but bad actors have abused it in the past to host malicious AI models.
The recent campaign discovered by researchers at Romanian cybersecurity company Bitdefender leverages the platform to distribute Android malware.
The attack begins with victims being lured to install a dropper app called TrustBastion, which uses scareware-style ads claiming that the target’s device is infected. The malicious app is disguised as a security tool, claiming to detect threats such as scams, fraudulent SMS messages, phishing attempts, and malware.
Immediately after installation, TrustBastion shows a mandatory update alert with visual elements that mimic Google Play.
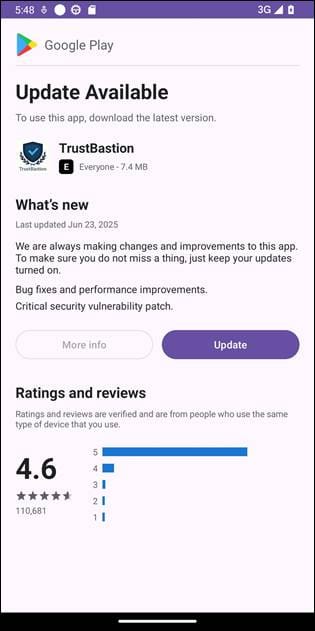
Source: Bitdefender
Instead of directly serving malware, the dropper contacts a server linked to trustbastion[.]com, which returns a redirect to a Hugging Face dataset repository hosting the malicious APK. The final payload is downloaded from Hugging Face infrastructure and delivered via its content distribution network (CDN).
To evade detection, the threat actor uses server-side polymorphism that generates new payload variants every 15 minutes, Bitdefender says.
“At the time of investigation, the repository was approximately 29 days old and had accumulated more than 6,000 commits.”
During analysis, the payload-serving repository was taken down, but the operation resurfaced under a new name, ‘Premium Club,’ which used new icons while retaining the same malicious code.
The main payload, which lacks a name, is a remote access tool that aggressively exploits Android’s Accessibility Services, presenting the request as necessary for security reasons.
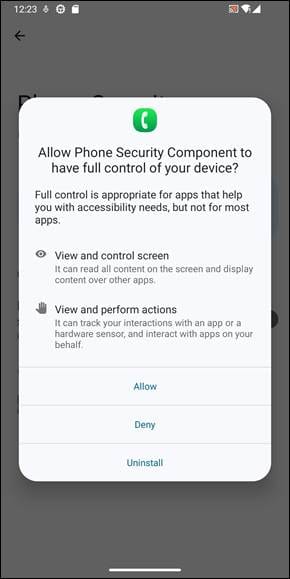
Source: Bitdefender
This gives the malware the ability to serve screen overlays, capture the user’s screen, perform swipes, block uninstallation attempts, and more.
In this case, Bitdefender says the malware monitors user activity and captures screenshots, exfiltrating everything to its operators. The malware also displays fake login interfaces impersonating financial services such as Alipay and WeChat to steal credentials, and also attempts to steal the lock screen code.
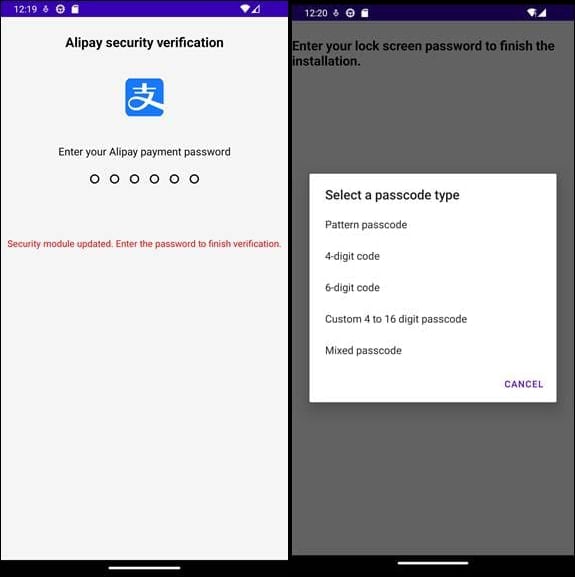
Source: Bitdefender
The malware remains connected at all times to the command-and-control (C2) server, which receives the stolen data, sends command execution instructions, configuration updates, and also pushes fake in-app content to make TrustBastion appear legitimate.
Bitdefender informed Hugging Face about the threat actor’s repository, and the service removed the datasets containing the malware. Researchers also published a set of indicators of compromise for the dropper, the network, and malicious packages.
Android users should avoid downloading apps from third-party app stores or installing them manually. They should also review the permissions an app requests and ensure all of them are necessary for the app’s intended functionality.
It’s budget season! Over 300 CISOs and security leaders have shared how they’re planning, spending, and prioritizing for the year ahead. This report compiles their insights, allowing readers to benchmark strategies, identify emerging trends, and compare their priorities as they head into 2026.
Learn how top leaders are turning investment into measurable impact.



