Google announced on Wednesday that it has disrupted a significant China-linked cyberespionage campaign targeting telecoms and government organizations worldwide.
The threat actor, tracked by Google’s Threat Intelligence Group (GTIG) and Mandiant as UNC2814, has been active since at least 2017. It has been described as one of the most far-reaching and impactful campaigns encountered in recent years.
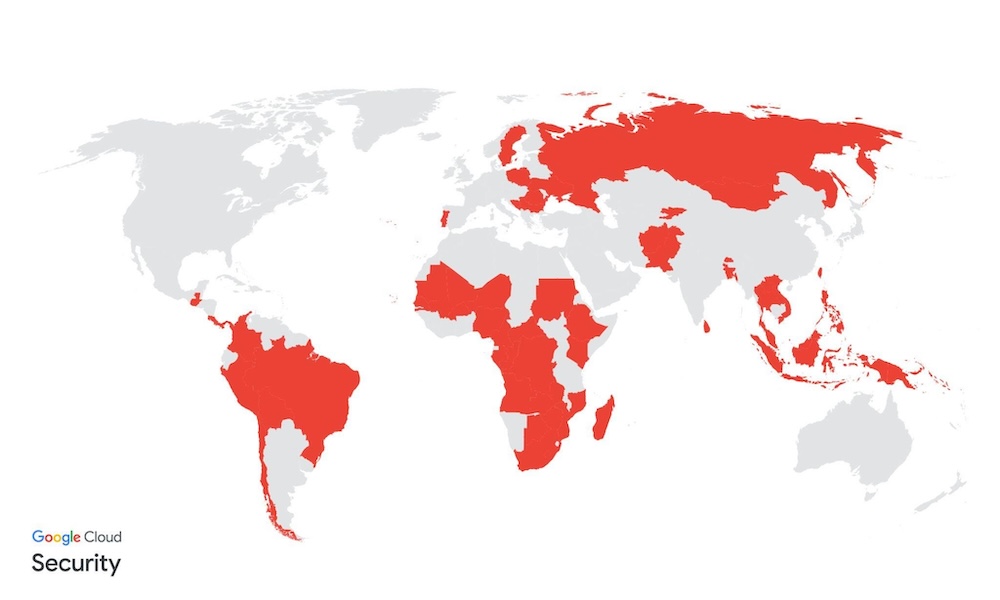
According to Google, this elusive threat actor has targeted at least 53 organizations across 42 countries in the Americas, Asia, and Africa. There is suspicion that the cyberspies may have targeted at least 20 other countries.
“The attacker was using API calls to communicate with SaaS apps as command-and-control (C2) infrastructure to disguise their malicious traffic as benign, a common tactic used by threat actors when attempting to improve the stealth of their intrusions,” the tech giant explained. “Rather than abusing a weakness or security flaw, attackers rely on cloud-hosted products to function correctly and make their malicious traffic seem legitimate.”
The threat actor has used a new backdoor named GridTide, which enables shell command execution, and file uploads and downloads.
“The backdoor leverages Google Sheets as a high-availability C2 platform, treating the spreadsheet not as a document, but as a communication channel to facilitate the transfer of raw data and shell commands,” Google explained.
The company’s researchers observed GridTide on an endpoint containing personal information such as names, dates of birth, phone numbers, voter IDs, and national IDs. The targeting of this type of data suggests that the hackers may have been trying to track and monitor individuals of interest.
“GTIG did not directly observe UNC2814 exfiltrate sensitive data during this campaign,” Google said. “However, historical PRC-nexus espionage intrusions against telecoms have resulted in the theft of call data records, unencrypted SMS messages, and the compromise and abuse of lawful intercept systems.”
While the targeting of telecoms companies by a Chinese threat actor is reminiscent of the group called Salt Typhoon, Google noted that it has found no overlaps between Salt Typhoon and UNC2814.
Disrupting the UNC2814 campaign
To disrupt UNC2814’s campaign, GTIG, Mandiant and their partners eliminated cloud resources used by the GridTide malware.
They also took down all the infrastructure associated with the cyberespionage operation. This included sinkholing current and historical domains to sever access to compromised environments.
In addition, they disabled accounts used by the hackers (including Google Cloud accounts used for C&C), and terminated access to the Google Sheets instances used by the malware.
Victims have been notified and assisted with incident response. Google has also released IoCs designed to help organizations detect GridTide and other UNC2814 activity.
Google expects this disruption to significantly set back UNC2814’s efforts to build out its global footprint.
Related: RedVDS Cybercrime Service Disrupted by Microsoft and Law Enforcement
Related: Google Says Chinese ‘Lighthouse’ Phishing Kit Disrupted Following Lawsuit
Related: RaccoonO365 Phishing Service Disrupted, Leader Identified

