Law enforcement agencies across 28 countries have spent the past year building cases against a loosely organized collective known as The Com, a decentralized network of mostly teenagers and young adults linked to high-profile ransomware attacks, financial extortion, and the coercion of vulnerable children.
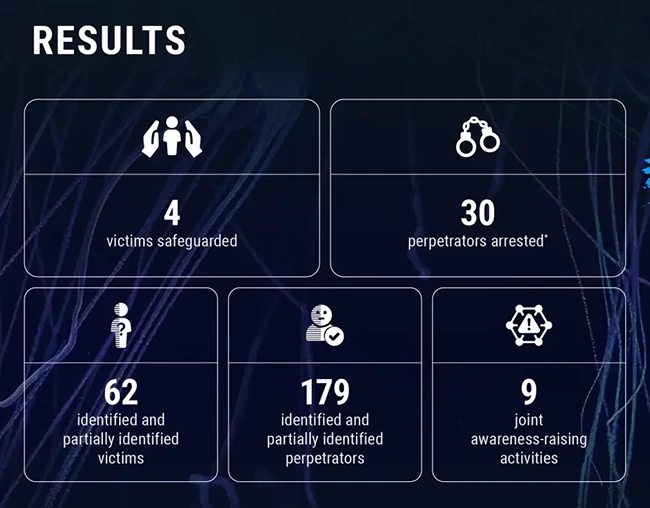
Europol announced the first operational results of Project Compass, reporting 30 arrests and the full or partial identification of 179 perpetrators since the initiative launched in January 2025. Investigators have also identified up to 62 victims and safeguarded four of them.
What The Com is and how it operates
The Com operates across social media platforms, messaging applications, online gaming environments, and music streaming services, using these spaces to recruit, radicalize, and exploit young people. Europol describes its decentralized structure as making it particularly difficult to disrupt.
Over time, The Com has developed connections to violent extremist groups and Russian cybercriminal gangs. Some offshoots have refined extortion tactics by running sextortion campaigns targeting other teenagers before escalating to attacks on corporations.
How Project Compass works
Project Compass is coordinated by Europol’s European Counter Terrorism Centre and brings together EU member states along with the Five Eyes nations (the United States, United Kingdom, Canada, Australia, and New Zealand), Norway, and Switzerland. U.S. participants include the FBI and Homeland Security Investigations; UK participants include Counter Terrorism Policing and the National Crime Agency.
The operation is built around a shared intelligence network that allows partner nations to contribute to investigations through specialized units. Countries are also exchanging preventative guidance and running data sprints to consolidate intelligence on active cases.
“Project Compass allows us to intervene earlier, safeguard victims and disrupt those who exploit vulnerability for extremist purposes,” said Anna Sjöberg, head of Europol’s European Counter Terrorism Centre. “No country can address this threat alone, and through this cooperation, we are closing the gaps they try to hide in.”

