CodeHunter is expanding its behavioral intent technology beyond traditional malware analysis to address supply chain risk and security decision-making across the software development lifecycle (SDLC).
According to a recent Gartner report, “software supply chains transcend organizational boundaries and consist of external entities in addition to internal systems.” Gartner also warns that “improper artifact integrity validation allows attackers to poison the software delivery pipeline and compromise the software being delivered”.
Originally built to overcome the limitations of signature-based malware detection, CodeHunter has focused from the outset on analyzing what software does, not just what it looks like. As automation, AI-generated malware, and complex software supply chains reshape attacker techniques, the company is aligning its platform to enable earlier, more reliable trust decisions across the complete software estate organizations build, acquire, and run.
“Malware has changed, but so has how software enters the enterprise, with organizations now moving enormous volumes of runnable artifacts through CI/CD pipelines at machine speed,” said Chris O’Ferrell, CEO of CodeHunter. “This next phase for CodeHunter is about extending behavioral intent analysis upstream, so teams can prevent malicious or policy-violating software from executing in the first place, not just detect it after a compromise.”
Establishing internal and external software trust
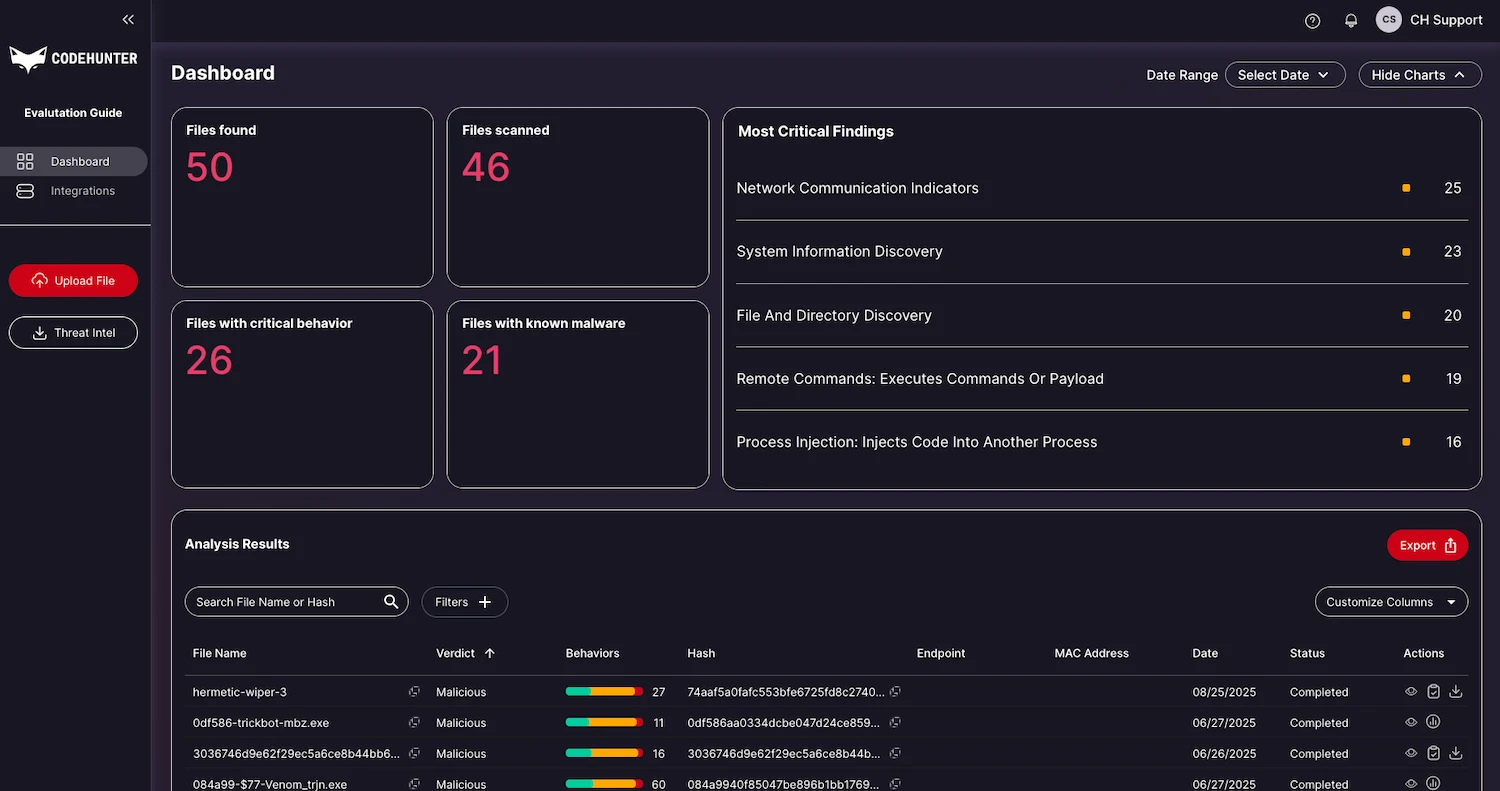
CodeHunter’s platform analyzes inbound, internally developed, and third-party software artifacts using proprietary control-flow and behavioral analysis, automating the reverse engineering of malware, combined with curated rule sets and dynamic sandbox observations. The result is a Behavioral Intent Profile (BIP), a deterministic, explainable record of how an artifact is expected to behave and whether that behavior introduces security, operational, or compliance risk.
Operationally, CodeHunter delivers a static verdict within minutes while running dynamic analysis in parallel, allowing teams to make fast decisions without relying solely on detonation windows or known-bad indicators.
For example, a signed binary produced during a build or obtained from a trusted source can be evaluated before promotion to identify unexpected network activity, privilege escalation, or system modifications that violate policy, despite the artifact appearing benign and properly signed.
CodeHunter’s BIPs can now be applied consistently across CI/CD pipelines, security operations, and production environments, enabling organizations to enforce policy decisions, such as allow, block, quarantine, or review, before software executes or propagates.
Rather than replacing existing security tools, CodeHunter operates as an out-of-band analysis layer, integrating through APIs, connectors, and artifact submission workflows. Verdicts and behavioral context are returned directly into the tools teams already use, including CI/CD systems, SIEMs, SOAR and EDR platforms.
Deterministic decisions for AI-driven threats
While AI assists with malware discovery and improves analyst efficiency, CodeHunter’s enforcement decisions are intentionally deterministic and explainable, providing the consistency and auditability required for enterprise governance, compliance, and risk management.
This approach addresses a growing challenge for security leaders: as AI-generated and mutating artifacts evade static indicators and sandboxing, organizations must assess behavior and intent earlier, before software is allowed to run.