
The Russian state-sponsored APT28 threat group is using a custom variant of the open-source Covenant post-exploitation framework for long-term espionage operations.
Also tracked as Fancy Bear, Forest Blizzard, Strontium, and Sednit, the APT28 hacker group is known for developing high-end implants and breaching notable entities, such as the German Parliament, multiple French organizations, government networks in Poland, and European NATO member countries.
Researchers at cybersecurity company ESET noticed that since April 2024, the Russian group has started using in attacks two implants named BeardShell and Covenant.
“This dual-implant approach enabled long-term surveillance of Ukrainian military personnel,” ESET notes in a report today.
The two pieces of malware have been used recently to target central executive bodies of Ukraine in attacks that exploited the CVE-2026-21509 vulnerability in Microsoft Office via malicious DOC files.
The researchers uncovered these malware families after discovering SlimAgent, a keylogging implant deployed in a Ukrainian government system capable of keystroke capture, clipboard collection, and screenshot capture.
BeardShell is a modern implant that leverages the legitimate cloud storage service Icedrive for command-and-control (C2) communication. It can execute PowerShell commands in a .NET runtime environment and was used together with SlimAgent, according to a report from CERT-UA in June 2025.
ESET found that BeardShell also uses a unique obfuscation technique previously seen in Xtunnel, a network-pivoting tool that APT28 used in the 2010s.
In the recent attacks, the Russian threat group paired BeardShell with a heavily modified version of the open-source Covenant .NET post-exploitation framework.
The changes they introduced include deterministic implant identifiers tied to host characteristics, modified execution flow to evade behavioral detection, and new cloud-based communication protocols.
Since July 2025, the threat actor has used the Filen cloud provider with Covenant. Previously, the attacker used Koofr and pCloud services.
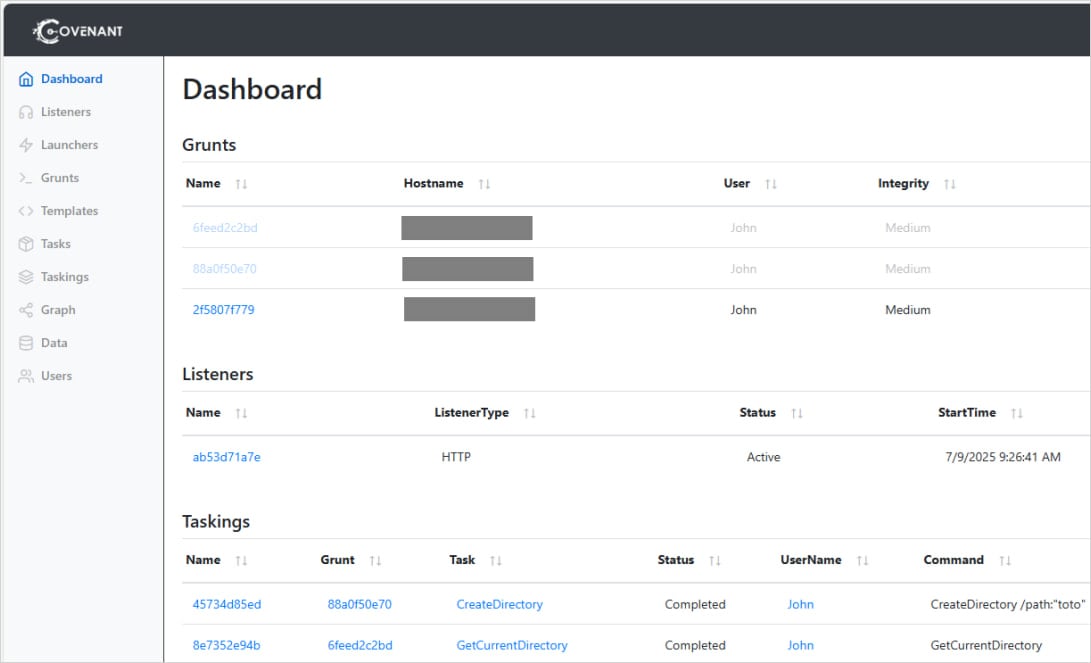
Source: ESET
ESET says Covenant is used as the primary implant, and BearShell serves as the fallback tool.
“Since 2023, Sednit developers have made a number of modifications and experiments with Covenant to establish it as their primary espionage implant, keeping BeardShell mainly as a fallback in case Covenant encounters operational issues, such as the takedown of its cloud-based infrastructure.” – ESET
ESET believes that APT28’s advanced malware development team returned to activity in 2024, giving the threat group new long-term espionage capabilities. The technical similarities with 2010-era malware indicate continuity in the threat group’s development team.


