North Korea’s BlueNoroff state-sponsored hacking group is targeting cryptocurrency executives in an audacious, financially motivated campaign that uses fake Zoom meetings populated with AI-generated avatars and stolen video footage of real people to trick victims into installing malware on their systems.
What makes the campaign particularly insidious, according to a new report from Arctic Wolf, is how the threat actor steals webcam footage from each victim and then uses those videos to populate even more convincing fake Zoom meetings to target new victims.
Insidious Campaign
Arctic Wolf found stolen images and videos of at least 100 individuals — nearly half of them CEOs or co-founders of their organizations — that the threat actor appears to have used as bait in the campaign.
Eight out of 10 of the identified victims operated either in the cryptocurrency/blockchain and associated finance sectors. “This concentration underscores BlueNoroff’s singular operational focus: individuals with access to cryptocurrency assets, wallet infrastructure, exchange platforms, or investment decision-making authority,” Arctic Labs said in a report this week.
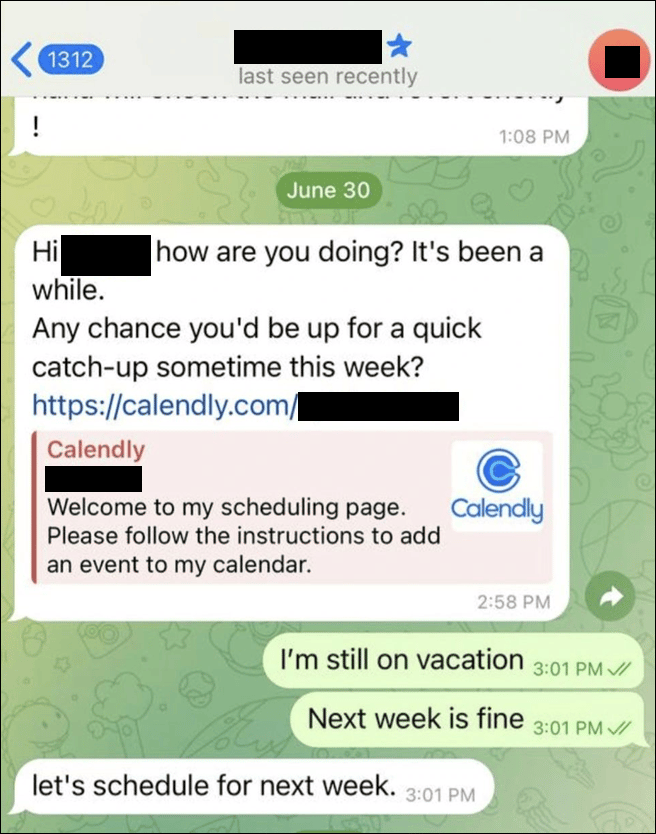
One incident that Arctic Wolf investigated involved a senior executive at a US-based Web3 cryptocurrency company. The attack chain began with a BlueNoroff actor posing as the head of legal at an international consulting and law firm in the fintech and crypto sector, sending a Calendly invite to the target. The purported “catch-up” meeting was scheduled late last summer for five months in the future (January 2026). When the victim confirmed the meeting, a Google Meet calendar invite was generated, which the threat actor then covertly modified and replaced with a typo-squatted Zoom URL.
“From the target’s perspective, the attack begins as a legitimate business interaction, often through a compromised Telegram account, Calendly invite, or calendar workflow impersonating a trusted contact such as a legal executive, VC partner, or industry peer,” says Ismael Valenzuela, VP of labs, threat research and intelligence at Arctic Wolf. “The pretext is a routine meeting.”
When the victim in Arctic Wolf’s investigation clicked the link this past January, they were directed to a HTML page that convincingly mimicked a Zoom conference lobby, complete with fabricated participant avatars and pre-recorded clips mimicking a live meeting. When the victim granted microphone and camera access to join the fake meeting, the threat actor covertly began siphoning the webcam feed in real time, for use in future attacks.
“[The victim sees] a realistic meeting interface populated with recognizable participants, which may include stolen webcam footage from prior victims, scraped images, or AI-generated headshots tailored to their network,” Valenzuela says. “The meeting appears active, with moving participant tiles and shifting speaker indicators, but there is no real conversation, and audio often appears not to function,” Valenzuela explains.
From Initial Click to Total Compromise in Minutes
Seconds into the “meeting,” and seemingly to fix the errant audio issue, the victim received a ClickFix prompt about their Zoom SDK needing an update. When the victim acted on the prompt instructions it triggered a sequence of actions in the background that ended with multiple malicious payloads being installed on their systems, including those for persistence, command-and-control, credential harvesting, stealing from crypto currency wallets, and Telegram session theft. Arctic Wolf found the entire post-exploitation sequence, from initial click to full system compromise, including credential theft and persistent access, happening in less than five minutes. In the incident that the security vendor investigated, BlueNoroff maintained persistence on the victim environment for 66 days.
One of the most alarming aspects of the campaign is how the attackers have established a “self-reinforcing deepfake production pipeline” that combined exfiltrated webcam footage from prior victims with AI-generated images to produce new fake meeting content, according to Arctic Wolf. The vendor analyzed more than 950 files from the attacker’s media hosting server, which showed the threat actor using three types of fake meeting participants in its campaign: stolen footage of prior victims, AI-generated still images, and deepfake composite videos that combined AI-generated faces with actual human body motion.
“The attacker’s infrastructure is extensive and operationally active,” Arctic Wolf added. For example, BlueNoroff had more than 80 typo-squatted Zoom and Teams domains registered with just one hosting provider, with new ones being added on a continuous basis. “The volume of distinct payload delivery URLs observed on VirusTotal confirms this is not an isolated operation, but a sustained campaign targeting multiple organizations simultaneously,” the security vendor said.
For organizations, the most important takeaway is that this is a coordinated social engineering campaign designed to scale through compromised identities, Valenzuela says. “Employees should verify meeting requests through a secondary channel, inspect calendar links for manipulation and avoid executing commands during a call,” he advises. “Security teams should restrict webcam and microphone access to trusted domains and monitor for clipboard abuse, PowerShell activity, and unauthorized access to browser-stored credentials.”

