
Home security giant ADT has confirmed a data breach after the ShinyHunters extortion group threatened to leak stolen data unless a ransom is paid.
In a statement shared today, the company said it detected unauthorized access to customer and prospective customer data on April 20, after which it terminated the intrusion and launched an investigation.
This investigation determined that personal information was stolen during the breach.
“The investigation confirmed that the information involved was limited to names, phone numbers, and addresses,” ADT told BleepingComputer.
“In a small percentage of cases, dates of birth and the last four digits of Social Security numbers or Tax IDs were included. Critically, no payment information — including bank accounts or credit cards — was accessed, and customer security systems were not affected or compromised in any way.”
ADT says the intrusion was limited and that it has contacted all affected individuals.
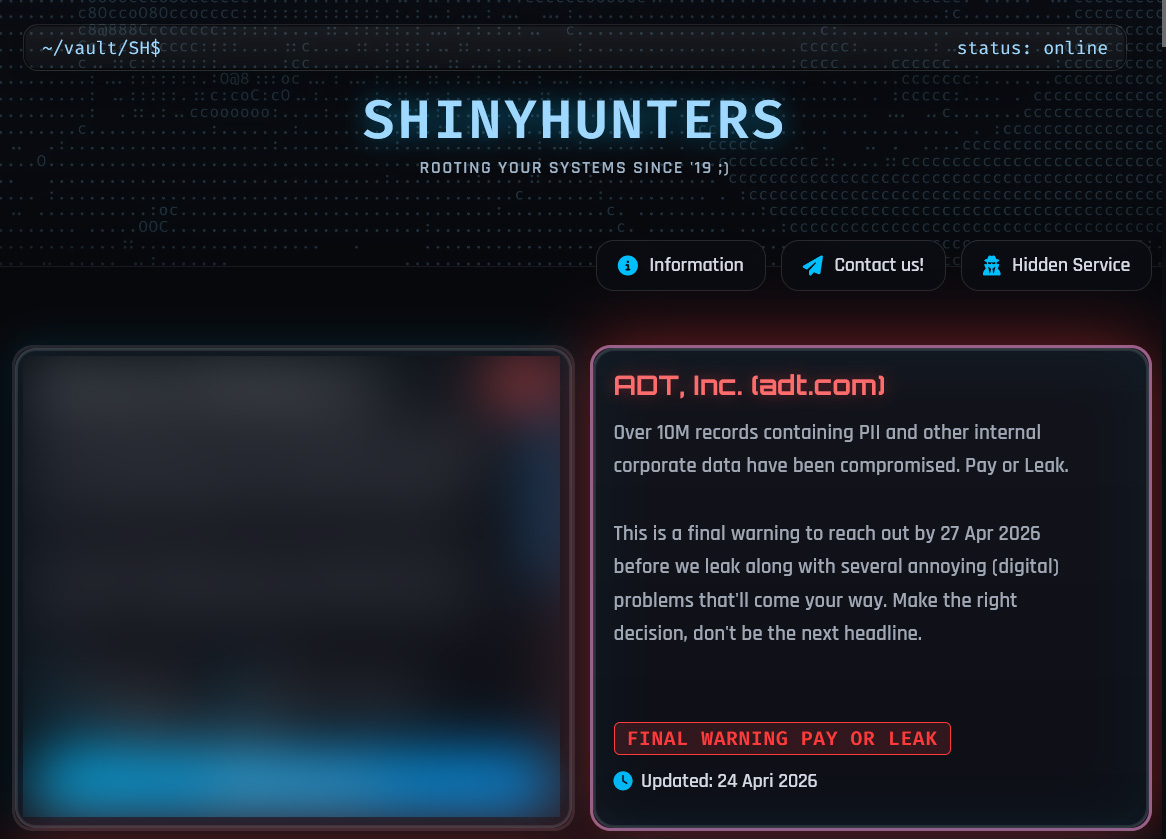
ShinyHunters leak site listing
This statement follows ADT’s listing on the ShinyHunters data leak site, where attackers claimed to have stolen 10 million records containing customers’ personal information.
“Over 10M records containing PII and other internal corporate data have been compromised. Pay or Leak,” reads the data leak site.
“This is a final warning to reach out by 27 Apr 2026 before we leak along with several annoying (digital) problems that’ll come your way.”
ADT did not confirm the volume of data theft claimed by the attackers.
ShinyHunters told BleepingComputer they allegedly breached ADT through a voice phishing (vishing) attack that compromised an employee’s Okta single sign-on (SSO) account. Using this account, the threat actors claimed they accessed and stole data from the company’s Salesforce instance.
Since last year, the extortion group has been conducting widespread vishing campaigns that target employees and BPO agents’ Microsoft Entra, Okta, and Google SSO accounts.
After gaining access to a corporate SSO account, the threat actors steal data from connected SaaS applications such as Salesforce, Microsoft 365, Google Workspace, SAP, Slack, Adobe, Atlassian, Zendesk, Dropbox, and many others.
This stolen data is then used to extort the company into paying a ransom, or the data will be leaked.
ADT has previously disclosed data breaches in August and October 2024 that exposed customer and employee information.
AI chained four zero-days into one exploit that bypassed both renderer and OS sandboxes. A wave of new exploits is coming.
At the Autonomous Validation Summit (May 12 & 14), see how autonomous, context-rich validation finds what’s exploitable, proves controls hold, and closes the remediation loop.



