
Hackers are exploiting a critical vulnerability in Marimo reactive Python notebook to deploy a new variant of NKAbuse malware hosted on Hugging Face Spaces.
Attacks leveraging the remote code execution flaw (CVE-2026-39987) started last week for credential theft, less than 10 hours after technical details were disclosed publicly, according to data from cloud-security company Sysdig.
Sysdig researchers continued to monitor activity related to the security issue identified additional attacks, including a campaign that started on April 12 that abuses the Hugging Face Spaces platform for showcasing AI applications.
Hugging Face serves as an AI development and machine learning-focused platform, acting as a hub for AI assets such as models, datasets, code, and tools, shared among the community.
Hugging Face Spaces lets users deploy and share interactive web apps directly from a Git repository, typically for demos, tools, or experiments around AI.
In the attacks that Sysdig observed, the attacker created a Space named vsccode-modetx (an intentional typosquat for VS Code) that hosts a dropper script (install-linux.sh) and a malware binary with the name kagent, also an attempt to mimic a legitimate Kubernetes AI agent tool.
After exploiting the Marimo RCE, the threat actor ran a curl command to download the script from Hugging Face and execute it. Because Hugging Face Spaces is a legitimate HTTPS endpoint with a clean reputation, it is less likely to trigger alerts.
The dropper script downloads the kagent binary, installs it locally, and sets up persistence via systemd, cron, or macOS LaunchAgent.
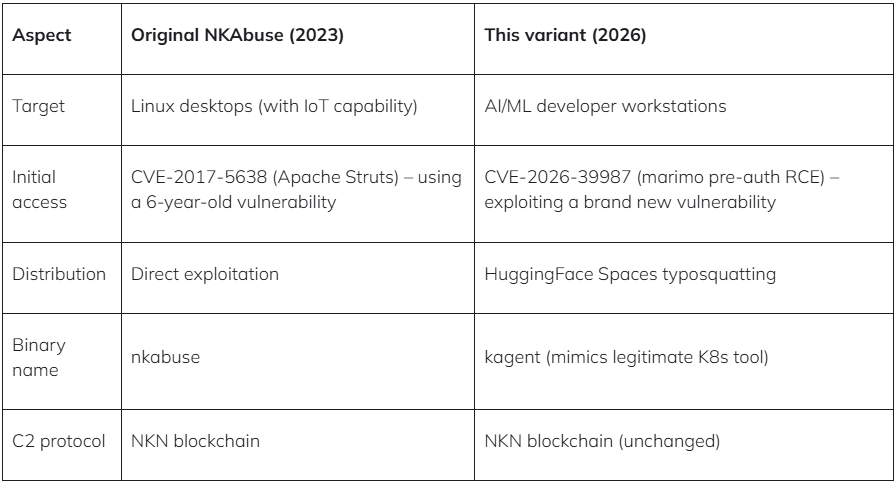
According to the researchers, the payload is a previously undocumented variant of the DDoS-focused malware NKAbuse. Kaspersky researchers reported the malware in late 2023 and highlighted its novel abuse of the NKN (New Kind of Network) decentralized peer-to-peer network technology for data exchange.
Sysdig says that the new variant functions as a remote access trojan that can execute shell commands on the infected system and send the output back to the operator.
“The binary references NKN Client Protocol, WebRTC/ICE/STUN for NAT traversal, proxy management, and structured command handling – matching the NKAbuse family initially documented by Kaspersky in December 2023,” mentions Sysdig in the report.
Sysdig also spotted other notable attacks exploiting CVE-2026-39987, including a Germany-based operator who attempted 15 reverse-shell techniques across multiple ports.
They then pivoted to lateral movement by extracting database credentials from environment variables and connecting to PostgreSQL, where they rapidly enumerated schemas, tables, and configuration data.
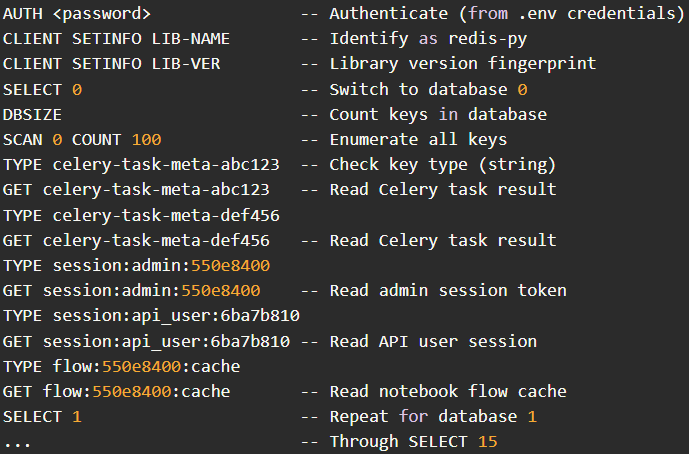
Another actor from Hong Kong used stolen .env credentials to target a Redis server, systematically scanning all 16 databases and dumping stored data, including session tokens and application cache entries.
The overall takeaway is that exploitation of CVE-2026-39987 in the wild has increased in volume and tactics, and it’s crucial that users upgrade to version 0.23.0 or later immediately.
If upgrading is not possible, it is recommended to block external access to the ‘/terminal/ws’ endpoint via a firewall, or block it entirely.



