Written by Ran Geva, CEO at Webz.io & Lunarcyber.com
In 2026, stolen credentials are a top-tier security priority. They are also a paradox: even though they are considered a significant risk, enterprises still opt for checkbox solutions and generic tools to mitigate the problem.
According to a recent survey commissioned by Lunar, a dark-web monitoring platform powered by Webz.io, 85% of organizations rank stolen credentials as a high or very high risk, with 62% saying they are in their top-three security priorities.
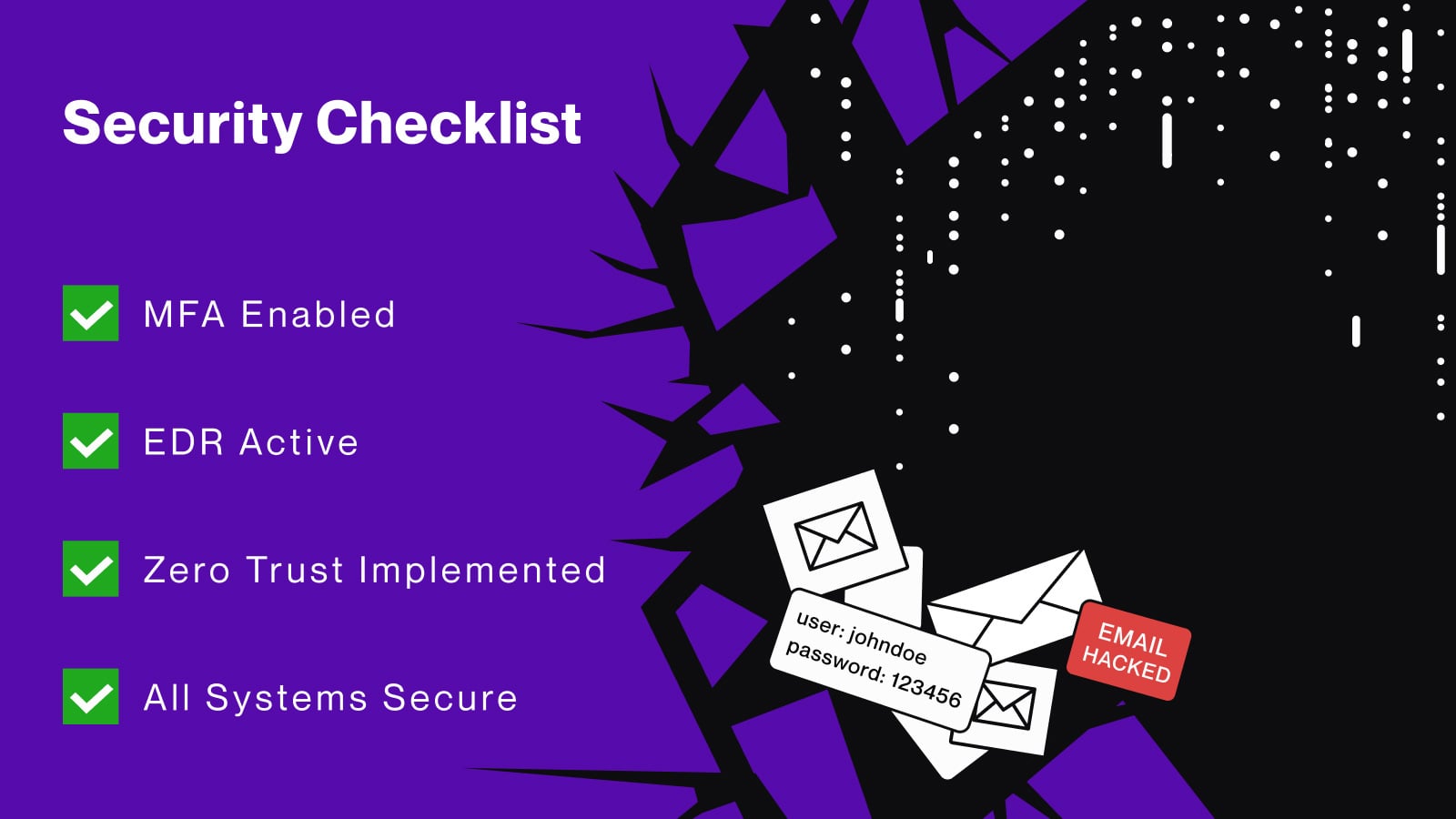
At the same time, I’ve spoken with dozens of organizations using Lunar’s community platform, who have told me things like, “we have MFA everywhere, so we’re covered”, and “our EDR and zero-trust stack already protects our employees.”
They fail to realize that EDR and zero-trust measures offer no protection when an employee logs into a critical SaaS service from an unmanaged home device.
The consequences of failing to detect stolen credentials in time can be catastrophic. According to IBM’s Cost of a Data Breach Report, a breach involving compromised credentials costs between $4.81-4.88 million.
Considering that Lunar observed 4.17 billion compromised credentials in 2025 alone, the potential global cost of these attacks is staggering. All of this means that simple breach monitoring is no longer enough.
An enterprise mindset shift is needed to create a programmatic defense strategy that tackles the ever-evolving threat of infostealers.
Checkbox Monitoring and The Dangers of Using Generic Solutions
When speaking with organizations, I always ask how they mitigated the infostealer threat before onboarding Lunar. The answers I get follow the same pattern: Exposed credentials are a serious problem and we dedicated resources to solutions to mitigate the threat.
What they didn’t realize is that those solutions were lacking and mainly consisted of:
-
A focus on data breaches instead of infostealers
-
ULPs and non-forensic infostealer data
-
High latency and stale data sources
-
No automation, integrations, or investigation capabilities
Our research lays out just how serious the problem is. Only 32% of enterprises that we surveyed use dedicated credential monitoring solutions, while 17% have no tooling at all.
Meanwhile, more than 60% of organizations check for exposed credentials monthly, rarely, or not at all.
We’ve seen firsthand how these solutions perform. When new organizations onboard Lunar, many are shocked to realize that while their previous tools told them that a breach had happened, they never got the tools to properly investigate how it happened.
The forensic details, including the accounts that were compromised, the devices infected, the SaaS apps that could be impacted, not to mention the session cookies that were stolen, were simply not there.
While the checkbox approach is better than no security at all, it rarely provides the forensic detail that enterprises need to successfully mitigate the infostealer threat. So, what’s holding them back from scaling their operations?
See where your company’s credentials and session cookies are already exposed.
Lunar continuously monitors breaches and infostealer logs for your domains and surfaces actionable exposures in a free, enterprise‑grade dashboard.
The Infostealer Threat is Much Bigger Than Enterprises Think
This is where the infostealer paradox enters into our conversations. While everyone knows about the dangers of exposed credentials, they either fail to prioritize budgets or simply don’t know what kinds of solutions successfully mitigate the problem.
Furthermore, they don’t always understand just how prevalent credential theft actually is, the environments they target, and the information they can access.
From the 4.17 billion compromised-credential records we collected in 2025, we analyzed infostealer logs, stealer-derived combolists, marketplaces, and Telegram channels. Infostealers like LummaC2, Rhadamanthys, Vidar, Acreed, and others consistently slipped past enterprise monitoring, even in environments that considered themselves mature.
And while many new Lunar users thought that the macOS was safer than Windows, they were shocked to hear about families like Atomic macOS Stealer (AMOS), Odyssey, MacSync, MioLab, and Atlas.
There is also an awareness problem regarding the data infostealers exfiltrate, which goes far beyond simple username/password pairs. With modern infostealers now sold as full-fledged products, with subscription tiers, dashboards, and documentation tuned to harvesting cookies, session tokens, and SaaS access at scale, organizations are now in a rush to catch up and protect their networks.
For threat actors, session cookies don’t just provide access. They effectively open the front door, letting them skip login pages entirely: no password prompt, no MFA challenge, and often no obvious trace in standard authentication logs.
That is the piece of the puzzle that many organizations are only now internalizing.
What Does a Typical Infostealer Attack Look Like?
When we talk about what an infostealer attack looks like, and why checkbox security is ineffective, we often break it down into the following process:
-
Target is infected: The victim’s device is compromised by an infostealer delivered through vectors such as zero-day exploits, ClickFix campaigns, rogue browser extensions, unverified or pirated software, game mods, or malicious open-source projects.
-
Credentials are exfiltrated: The infostealer extracts the browser for logins and cookies, including those from third-party portals, and sends them back to the malware operator.
-
Credentials are bundled and sold: The stolen credentials are bundled into logs and sold on underground markets and private channels.
-
Attackers access the enterprise network: The attacker who purchases the logs accesses the target network, including third-party portals, using a valid session token.
This entire chain of events can be completed in hours. Meanwhile, many of the organizations we speak with run credential checks once a month or rely on outdated data.
By the time anything shows up in their legacy monitoring tools, attackers have had plenty of time to explore and exfiltrate whatever data they want.
Developing a Mature Breach Monitoring Program
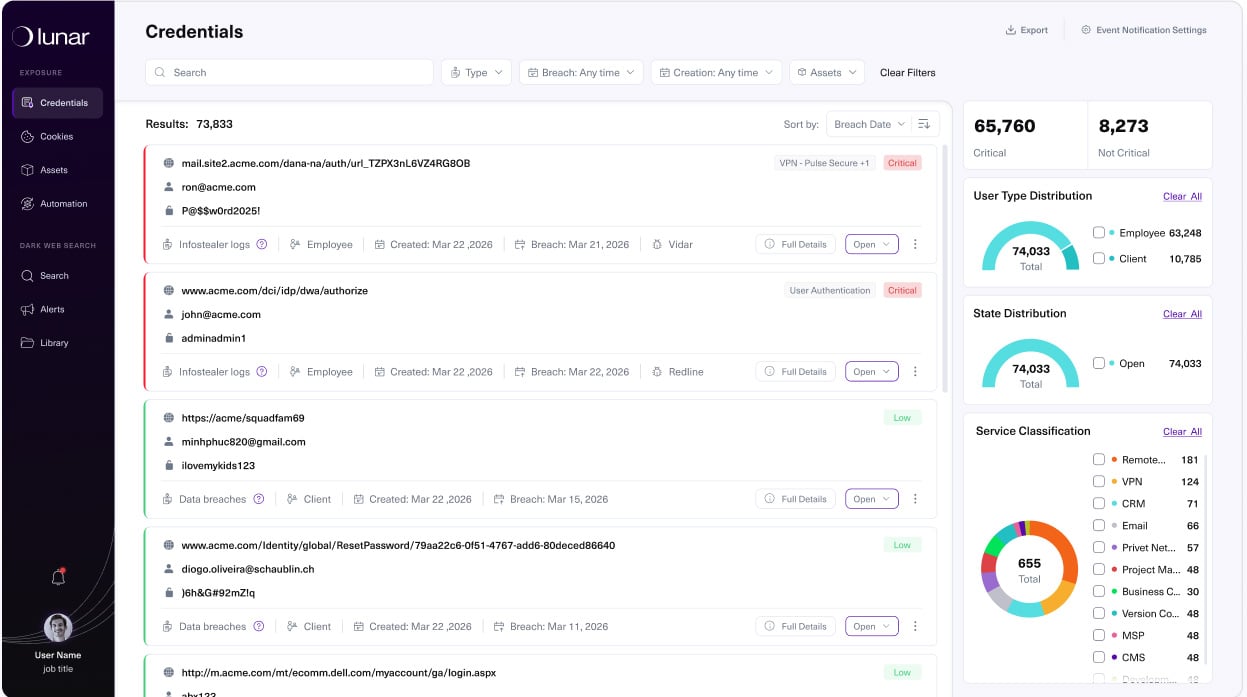
Organizations we work with that make the switch to a mature breach monitoring program have the tools they need to collect information from channels like stealer logs, Telegram groups, and marketplaces. Instead of relying on ad-hoc checks, they focus on three practical capabilities:
-
Continuous monitoring and normalization of key sources (breaches, stealer logs, combolists, marketplaces, and relevant channels), so security teams have a clear and deduplicated view of breach exposures.
-
Targeted automation that reduces false positives and noise, ensuring that analysts spend time on identities and sessions that actually matter.
-
Integrations into existing security and identity stacks (SIEM, SOAR, IDP) that execute playbooks end-to-end, resetting credentials, invalidating sessions, and blocking accounts as soon as exposures are confirmed.
Among Lunar users, we’ve seen a clear mindset shift once they get this right. They treat the infostealer threat as its own domain, complete with ownership, metrics, and playbooks, instead of managing their breach monitoring using unrelated tools.
This all goes back to Lunar’s core mission, which is to provide a free breach monitoring solution to any organization, regardless of budget, that delivers enterprise-grade coverage of compromised credentials, infostealers, and session cookies.
Our philosophy is to openly provide enriched compromised credential intelligence, enabling organizations to regain true visibility and resilience.
Redefining Breach Monitoring in 2026
Even seasoned and knowledgeable security teams can fall into the breach monitoring paradox, where they know the threat but behave as if monthly checks, MFA, and EDR are enough. But in 2026, infostealers move at a speed and scale that checkbox monitoring solutions were never designed to handle.
Treating breach monitoring as a must-have program, instead of a one-off product, provides your enterprise with the visibility needed to view compromised credentials wherever they appear, the context to understand what those exposures mean, and the playbooks to automatically react when an attack is detected.
To see how Lunar can help you find your organization’s compromised credentials, sign up for free access.
Sponsored and written by Lunar.