
Researchers warn that residential proxies used to route malicious traffic are a big problem for IP reputation systems, as there is no clear distinction between attackers and legitimate users.
This occurs because residential proxies are too short-lived, uninvolved, or systematically rotated, preventing defense systems from cataloging them in time.
Cybersecurity intelligence platform GreyNoise determined this after examining a massive dataset of 4 billion malicious sessions targeting the edge over a three-month period.
Roughly 39% of those sessions appear to originate from home networks, most certainly part of residential proxies, but 78% of them are invisible to reputation feeds.
“The data reveals a pattern that challenges a core assumption of network defense: that you can tell attackers from legitimate users by where the traffic comes from,” explains GreyNoise.
According to the company, most residential IPs are used once or twice, and then vanish, with attackers rotating them with others, keeping the pace at a level that reputation systems will not flag them.
About 89.7% of residential IPs are active in malicious operations for under a month, with only 8.7% lasting 2 months, and 1.6% persisting for 3 months.
Those that are kept alive for longer seem to carry a specialization according to the researchers, being SSH-focused and using Linux TCP stacks.
Source: GreyNoise
Diversity is another factor that complicates flagging and blocking, as GreyNoise’s data shows the residential IPs participating in attacks belong to 683 internet service providers.
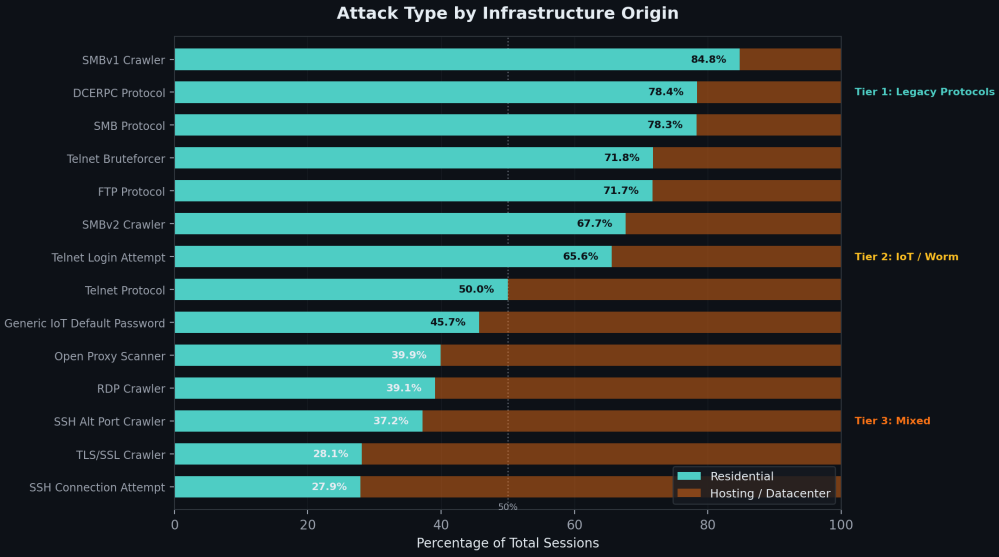
Another reason for their stealthiness is that they are primarily used for network scanning and reconnaissance, with only 0.1% involved in actual exploits, the researchers say.
A small percentage (1.3%) targeted enterprise VPN login pages, while some limited cases also involved residential IPs to path traversal and credential stuffing attempts.
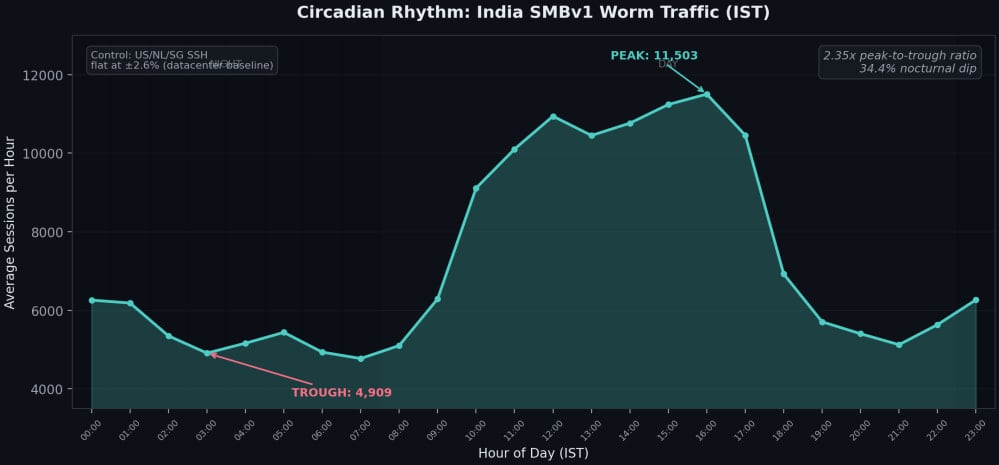
Regarding the source of the residential proxies, GreyNoise says China, India, and Brazil are major contributors, with traffic from the IPs following human sleep patterns, dropping by a third at night, when most people power off their devices.
Source: GreyNoise
The researchers report that residential proxy traffic is generated by two distinct, non-overlapping ecosystems: IoT botnets and infected computers.
In cases involving the latter, the proxies come from SDKs in free VPNs, ad blockers, and similar apps, which enroll user devices in bandwidth-selling schemes.
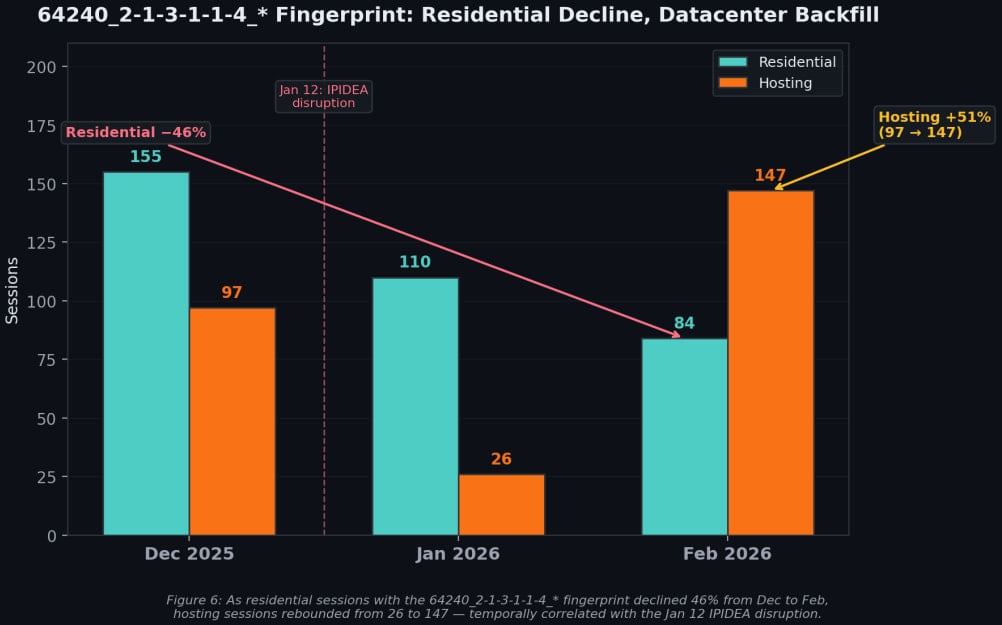
GreyNoise has also highlighted the resilience of these networks using the example of IPIDEA, one of the world’s largest residential proxy networks, which was recently disrupted by Google Threat Intelligence Group (GTIG) and partners.
The disruption reduced its proxy pool by roughly 40%, but in the period that followed, datacenter traffic increased, indicating that demand can be absorbed by others when needed and that lost capacity is quickly replaced.
Source: GreyNoise
GreyNoise says residential proxying evasion tactics require abandoning IP reputation as a primary signal and focusing instead on behavior.
The researchers suggest detecting sequential probing from rotating residential IPs, blocking clearly illegitimate protocols like SMB from ISP space, and tracking device fingerprints that survive IP rotation.


