
Cybersecurity firm F5 Networks has reclassified a BIG-IP APM denial-of-service (DoS) vulnerability as a critical-severity remote code execution (RCE) flaw, warning that attackers are exploiting it to deploy webshells on unpatched devices.
BIG-IP APM (short for Access Policy Manager) is a centralized access management proxy solution that enables admins to secure and manage user access to their organizations’ networks, cloud, applications, and application programming interfaces (APIs).
Tracked CVE-2025-53521, this security flaw can be exploited by attackers without privileges to perform remote code execution when targeting BIG-IP APM systems with access policies configured on a virtual server.
In addition to flagging the vulnerability as being exploited in the wild, F5 published indicators of compromise (IOCs) and advised defenders to check their BIG-IP systems’ disks, logs, and terminal history for signs of malicious activity.
“This known vulnerability was previously categorized and remediated as a Denial-of-Service (DoS) vulnerability. Due to new information obtained in March 2026, the original vulnerability is being re-categorized to an RCE. The original CVE remediation has been validated to address the RCE in the fixed versions. We have learned that this vulnerability has been exploited in the vulnerable BIG-IP versions,” F5 warned in an advisory update published this Sunday.
“F5 strongly recommends that you consult your corporate security policy for guidelines about incident handling procedures including but not limited to forensic best practices, that are specific to your organization. More specifically, review the policies to ensure that they comply with evidence collection and forensics procedures for a security incident before you attempt to recover the system,” the company added.
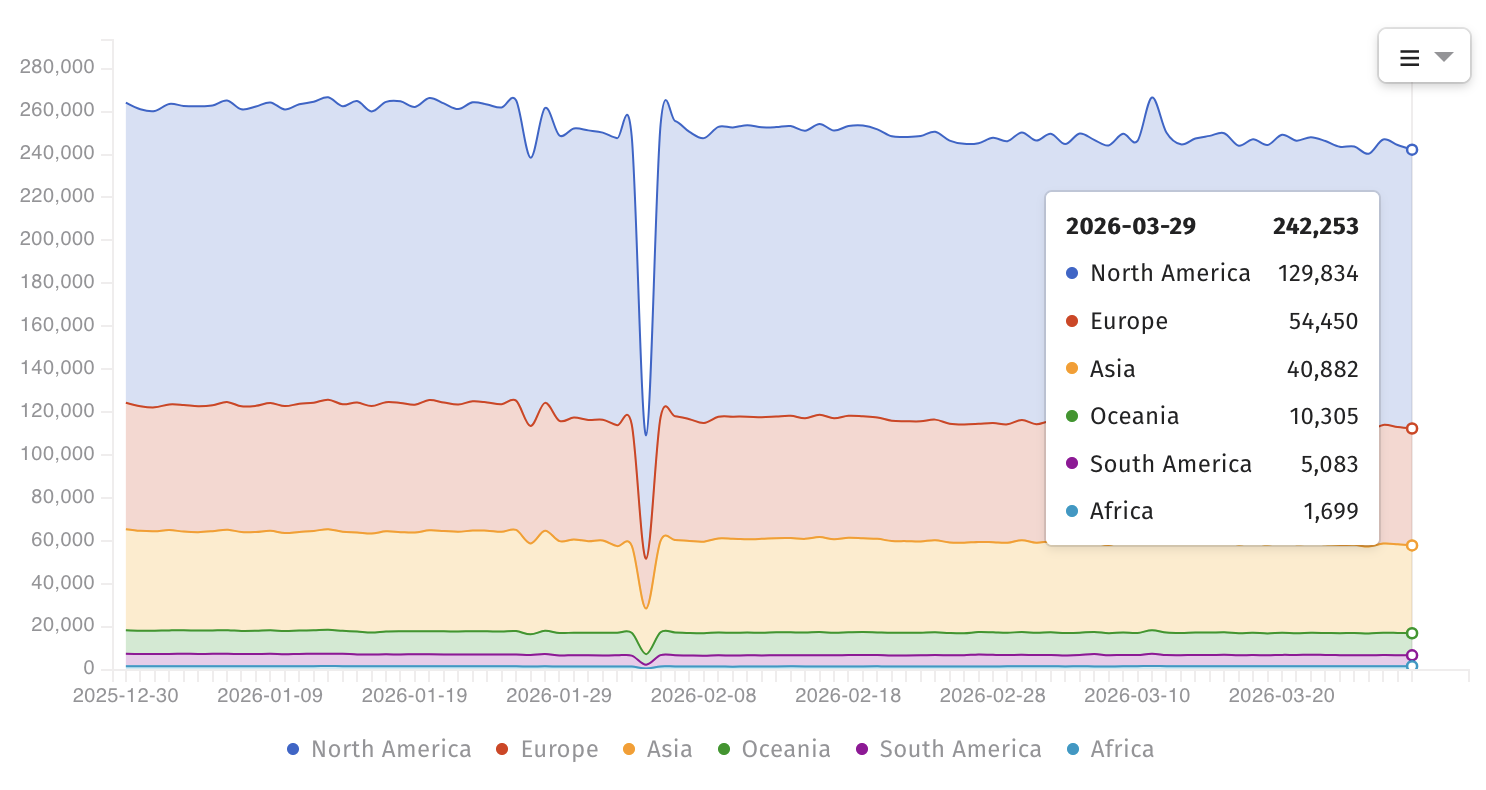
Internet threat-monitoring non-profit organization Shadowserver now tracks over 240,000 BIG-IP instances exposed online; however, there is no information on how many have a vulnerable configuration or have already been secured against CVE-2025-53521 attacks.
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) also added the vulnerability to its list of actively exploited flaws on Friday and ordered federal agencies to secure their BIG-IP APM systems by midnight on Monday, March 30.
“This type of vulnerability is a frequent attack vector for malicious cyber actors and poses significant risks to the federal enterprise,” it warned.
“Apply mitigations per vendor instructions, follow applicable BOD 22-01 guidance for cloud services, or discontinue use of the product if mitigations are unavailable.”
In recent years, BIG-IP vulnerabilities have been exploited by nation-state and cybercrime threat groups to breach corporate networks, map internal servers, deploy data-wiping malware, hijack devices, and steal sensitive documents from victims’ networks.
F5 is a Fortune 500 technology giant that provides cybersecurity, application delivery networking (ADN), and various other services to more than 23,000 customers worldwide, including 48 of the Fortune 50 companies.


