
Hackers are increasingly exploiting newly disclosed vulnerabilities in third-party software to gain initial access to cloud environments, with the window for attacks shrinking from weeks to just days.
At the same time, the use of weak credentials or misconfigurations has dropped significantly in the second half of 2025, Google notes in a report highlighting the trends on threats to cloud users.
According to the report, incident responders determined that bug exploits were the primary access vector in 44.5% of the investigated intrusions, while credentials were responsible for 27% of the breaches.

Source: Google
The most frequent vulnerability type exploited in attacks is remote code execution (RCE), the highlights being React2Shell (CVE-2025-55182) and the XWiki flaw tracked as CVE-2025-24893, leveraged in RondoDox botnet attacks.
Google believes this shift in focus was likely due to increased security measures for accounts and credentials.
“We assess that this change in behavior from threat actors is potentially due to Google’s secure-by-default strategy and enhanced credential protections successfully closing traditional, more easily exploitable paths, raising the barrier to entry for threat actors,” Google says.
The exploitation window has collapsed from weeks to a few days, as Google observed cryptominers deployed within 48 hours of vulnerability disclosure, indicating that hackers are highly ready to weaponize new flaws and incorporate them into their attack flows.
Both state-sponsored actors and financially-motivated hackers mostly leveraged compromised identities, via phishing and vishing impersonating IT help desk staff, to obtain access to a target organization’s cloud platform.
In most of the investigated attacks, the actor’s objective was silent exfiltration of high volumes of data without immediate extortion and long-term persistence.
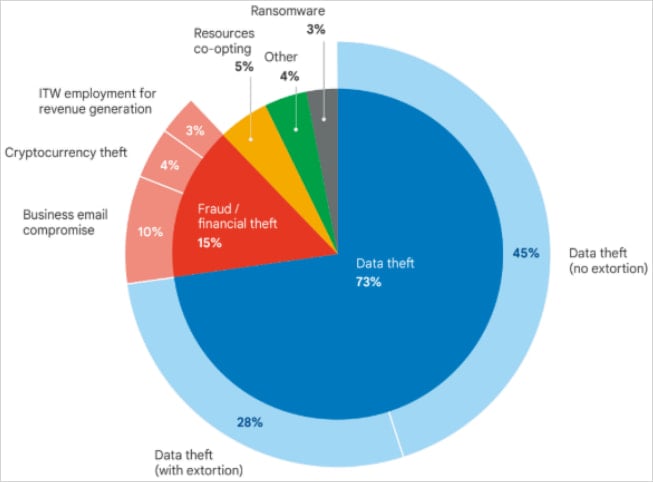
Source: Google
Google highlights some espionage campaigns from actors linked to Iran and China, who maintained access to the victim environment well over a year and a half.
For more than two years, Iran-linked threat actor UNC1549 had access to a target environment using stolen VPN credentials and the MiniBike malware. This allowed the hackers to steal from the victim nearly one terabyte of proprietary data.
In another example, the China-sponsored actor UNC5221 used the BrickStorm malware to keep access to a victim’s VMware vCenter servers for at least 18 months and steal source code.
North Korean hackers stealing millions
Google attributes 3% of the intrusions analyzed in the second half of 2025 to North Korean IT workers (UNC5267) using fraudulent identities to obtain a job and generate revenue for the government.
Another North Korean threat actor tracked as UNC4899 compromised cloud environments specifically to steal digital assets. In one case, UNC4899 stole millions of U.S. dollars in cryptocurrency after tricking a developer into downloading a malicious archive under the pretext of an open-source project collaboration.
The developer then used the Airdrop service to transfer the file from the personal computer to the corporate workstation and open it in an AI-assisted integrated development environment (IDE).
Inside the archive was malicious Python code that deployed a binary posing as a Kubernetes command-line tool.
“The binary beaconed out to UNC4899-controlled domains and served as the backdoor that gave the threat actors access to the victim’s workstation, effectively granting them a foothold into the corporate network” – Google
In the next stages, UNC4899 pivoted to the cloud environment and carried out reconnaissance activities, which included exploring specific pods in the Kubernetes cluster, established persistence, and “obtained a token for a high-privileged CI/CD service account.”
This allowed them to move laterally to more sensitive systems, such as a pod responsible for enforcing network policies that allowed them to break out of the container and plant a backdoor.
After additional reconnaissance, UNC4899 moved to a system that handled customer information (identities, account security, cryptocurrency wallet data) and hosted database credentials stored insecurely.
This data was enough for the threat actor to compromise user accounts and steal several million dollars in cryptocurrency.
OpenID Connect Abuse
In an attack leveraging a compromised npm package name called QuietVault, the attacker stole a developer’s GitHub token and used it to create a new admin account in the cloud environment by abusing the GitHub-to-AWS OpenID Connect (OIDC) trust.
In just three days from the initial compromise, QuietVault obtained the developer’s GitHub and NPM API keys by leveraging AI prompts with local AI command-line interface tools, abused the CI/CD pipeline to get the organization’s AWS API keys, stole data from the S3 storage, and then destroyed it in production and cloud environments.
The incident was part of the “s1ngularity” supply-chain attack in August 2025, when an attacker published compromised npm packages of the Nx open-source build system and monorepo management tool.
During the attack, sensitive info (GitHub tokens, SSH keys, configuration files, npm tokens) from 2,180 accounts and 7,200 repositories were exposed after the threat actor leaked them in public GitHub repositories that included the name “s1ngularity.”
Malicious insiders like cloud services
Although email and portable storage devices were primarily used for data exfiltration, the researchers noticed that insiders are increasingly using Amazon Web Services (AWS), Google Cloud, Microsoft Azure, Google Drive, Apple iCloud, Dropbox, and Microsoft OneDrive.
The conclusion comes after an analysis of 1,002 insider data theft incidents, which revealed that 771 of them occurred while the insider was still employed and 255 occurred after their employment was terminated.
Google says that the threat is significant enough for companies to implement data protection mechanisms against both internal and external threats. An employee, contractor, or consultant may sometimes violate trust and end up stealing corporate data.
The tech giant says that trend analysis indicates that cloud services will soon replace email as the preferred method to exfiltrate information.
The researchers report that, in a growing number of cases, attackers delete backups, remove log files, and wipe forensic artifacts to make the recovery of evidence and data harder.
Google underscores that cloud attack speeds are now too fast for manual response schemes, sometimes resulting in payload deployment within one hour of a new instance’s creation, making the implementation of automated incident response urgent.
For the trends that could shape cloud security this year, Google expects threat activity to increase, as geopolitical conflicts, the FIFA World Cup, and U.S. midterm elections will act as magnets for malicious operations.


